I installed Utopia so you don't have to
published: 2023-02-01
Because this post deals with a potentially sensitive topic, I feel the need to put the following disclaimers:
- I AM NOT A SECURITY RESEARCHER. I don't do malware testing for a living, or even as a hobby. Just because I didn't find any concrete evidence of spyware/malware in Utopia doesn't mean that there isn't any at all; it just means that, if there is any, it's not blatantly obvious to the amateur eye.
- Near the middle of this post, I show some analysis I did using
strace. Programs can likely see that they're attached tostraceand act differently if so. My analysis only shows what the Utopia client does when connected tostraceand not when it isn't. - Utopia devs or cryptobros, do not misinterpret this post as approval or endorsement of Cryptons or the Utopia ecosystem. I hope you crash and burn along with every other shitcoin. Tell your devs to spend less time spamming people on Twitter who even so much as mention Monero and more time fixing their hopelessly broken app.
Now, with that out of the way...
Once upon a time, there was a chat app called ANOM. Marketed towards drug cartels, human traffickers, and other criminals, it was distributed on Android phones specially modified to leak as little data about their surroundings as possible: no texting, no cellular radios, no GPS, et cetera. To conceal its existence on the phone, it pretended to be a calculator app and would only reveal to the user that it was ANOM after the user inputted a very specific calculation. ANOM claimed to use end-to-end encryption to protect its messages in the case of the servers being seized by a law enforcement agency. It used a number of proxy servers to route traffic between the user and the ANOM servers, thus concealing the purpose of the traffic to anyone running a network sniffer.
However, it turned out that those proxy servers were... ran by the FBI. Along with the rest of the app, developed by a man who was already writing a chat app, then got charges slapped on him, and chose to work with the FBI for a reduced sentence. And the "criminal influencers" who recommended ANOM to other criminals were mainly FBI informants or criminals unknowingly influenced by FBI informants. As far as I can tell, ANOM was closed-source, meaning very few people were able to figure out that it was a scam before over eight hundred people got arrested in the FBI's Operation Trojan Shield.
Why do I bring this up? Well, ANOM and Utopia have a lot in common. Both are closed-source, supposedly encrypted, distributed by a shady group of unknown people, (allegedly) connected to money laundering...
For those unaware of what Utopia is, exactly: Utopia is a self-proclaimed "P2P ecosystem" that effectively amounts to yet another chat app with a shitty browser and cryptocurrency tacked on at the end. The homepage has the usual slew of buzzwords like "censorship-free", "decentralized", and "anonymous". Its unique integrated cryptocurrency, "Cryptons", is billed as a "privacy coin" similar to Monero (their official Twitter account seemingly exists solely to encourage its users to spam Monero users with ads for Crypton) that can somehow be mined without an increase to power consumption or CPU load and doesn't have a whitepaper. And no, a "frostbox" for HODLing crypto doesn't count. Utopia also comes with its own darknet, accessed using the bundled "Idyll Browser", billed as a Tor alternative but without the outproxy function that was the whole point of Tor in the first place. You'd think a SUPER SECRET cabal of EPIC HACKERS would know that a darknet meant for hidden services that maybe might get an outproxy function later is better compared to I2P. As we zoomers say, "SMH my head."
Utopia, Cryptons, Idyll, and the other myriad pieces of the Utopia ecosystem have one glaring problem: THERE IS NO PUBLICALLY AVAILABLE SOURCE CODE. (Community-contributed accessories don't count. I want the source to the NETWORK.) The reason for this is a bunch of whining from the devs on the FAQ about potential forks of the protocol causing instability, despite the fact that ZeroNet's "main network" is unstable precisely because nobody there is competent enough to fix the code and Freenet has existed for over twenty years now and yet there is still no good alternate implementation of the Freenet protocols other than the original Java reference daemon, proving that the availability of the source has no bearing on the stability of the network and does not guarantee that the community is going to go out of their way to break compatibility without good reason.
But since people keep harassing me to add Utopia to Let's Decentralize, I suppose the only way to get the emails to stop (server-side email filtering doesn't do shit against GPG-encrypted messages) is to install it and give it a spin.
I installed a fresh copy of Linux Mint in a new VirtualBox VM, downloaded the Utopia client (not the mining bot) from the Utopia website, and installed it. At the time of writing, the latest version was 1.2.166, and this was the version I used throughout testing. Because I wanted to see what files on my machine the Utopia client would access, just in case it really was a Trojan horse like ANOM, I didn't launch Utopia through the Cinnamon desktop's application menu but through a terminal so I could attach strace to it and whatever other processes it spawned:
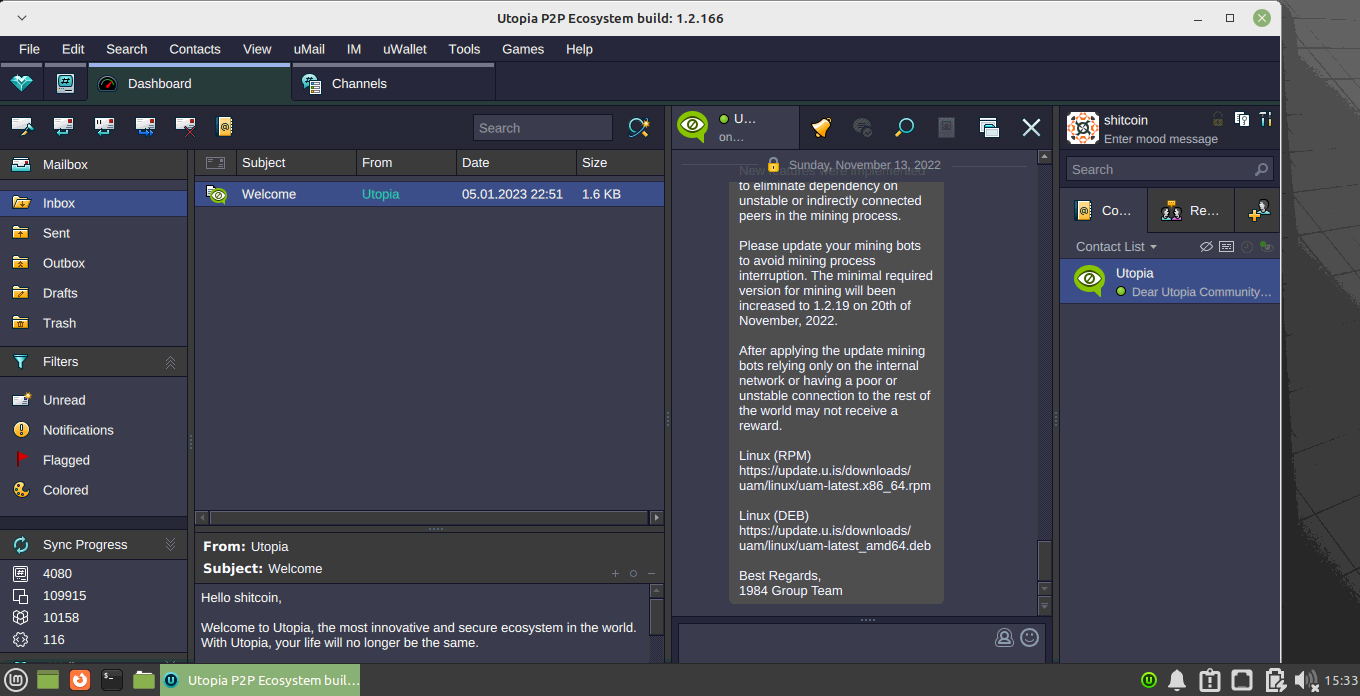
strace -f -e execve,access,openat -o ~/utopia.txt /opt/utopia/messenger/utopia
Utopia didn't like my virtual machine's screen resolution of 1360x696 (the biggest I could get it with my host running i3 with only a small status bar on the top and fullscreen otherwise) because the bottom of the window was cut off and the program refused to allow me to resize it smaller. The default UI is full of visual clutter on first launch, and I couldn't find a way to close "Dashboard", really just a messaging inbox, or "Channels". I was automatically added to an announcements channel last updated in November of last year. Bonus points if you can find the grammar error in this screenshot.
Since I don't have anyone already on Utopia to chat with, and I don't want to expose anyone else to Utopia in case it actually is malware, I couldn't chat with anyone. I saw that there are two games available, chess and poker, but I don't know how to play poker and the chess game doesn't let you play singleplayer.
No chats, no email, no games. What's left to do on Utopia? The darknet, I suppose.
So I launched Idyll, Utopia's built-in darknet browser. I got a blank page. No directory or anything. I went back to the main Utopia window, opened the Tools menu, and then started the uNS manager. uNS is Utopia's version of DNS, where you can pay cryptons to register a "domain" that you can then use to forward traffic from the network to your computer. Forwarding is port-based, so you can host pretty much any arbitrary program on Utopia. Going to "Registry" and then opening the "Sync Progress" tab, I could see that the last registered domain was "utopia.forever". An apt name, since it took... forever to load in Idyll, and then just timed out.
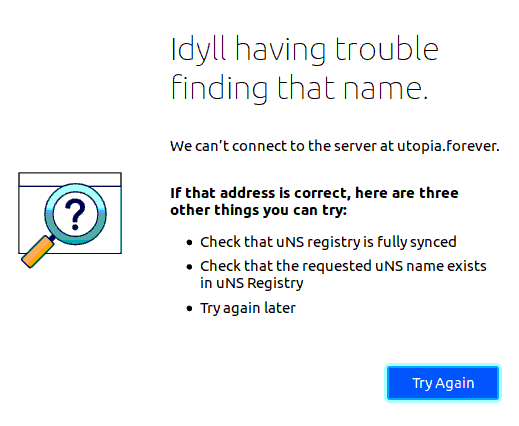
Going back to the main Utopia window, I went to the "Search" tab and started typing in random terms. The first one that came to mind was "music", which returned the domain... "justinbiebermusic.com". That site didn't load. I tried "utopia", which returned "darkutopia" and "utopia-google", neither of which loaded. (uNS doesn't require a domain to have a TLD, and you can just add whatever arbitrary TLDs you want to your registered domain.) Most domains were registered sometime in 2019, but I couldn't sort for new ones because clicking the "registration date" title on the table doesn't trigger any sorting. I looked in the manual to see if I was doing something wrong, but the troubleshooting section only gave instructions to reinstall the proxy configuration file and nothing else. The manual also claimed that I could go to "http://utopia" to test if the browser was working, but that domain also timed out. The only uNS site I could get working was "http://crp"... which is an internal crptocurrency exchange.
I thought about setting up a test site in Utopia. My usual modus operandi when it comes to darknets is to eschew any centralized domain service, like how I2P users insist you register a domain on one of three barely-functional services: one of them tried to set up mayvaneday.i2p without my knowledge, but I blocked requests from that domain pretty quickly- and just use the public key I'm given. So I opened up the uNS registry and went to "Packet Forwarding", but Utopia insisted that I could only set up packet forwarding after I bought a uNS record, costing about 10 CRP. (At the time of writing, that's about $6.25.)
So I can't chat or email because I have nobody to do it with. I can't play chess by myself. (And there are better ways to do so.) I can't access websites unless it's to buy a shitcoin. I can't host my own website because I don't have the money to burn on shitcoins for a network where almost none of the websites work. There's nothing for me to do on Utopia. So I closed the program and copied my strace capture to the host computer and shut down the VM.
Now for the allegations of the Utopia client being malware...
According to strace, Utopia did not attempt to access any sensitive files in my home directory. If it had tried to access something sensitive like ~/.ssh, it would have shown up in the logs, even if the file or directory was nonexistent. In my home directory, Utopia accessed:
- directory
/home/lethe/.cache/Utopia/ - directory
/home/lethe/.cache/qtshadercache-x86_64-little_endian-lp64/ - directory
/home/lethe/.cache/mesa_shader_cache/ - directory
/home/lethe/.icons/ - directory
/home/lethe/.config/pulse/ - directory
/home/lethe/.local/share/Utopia/ - directory
/home/lethe/.local/share/sounds/ - directory
/home/lethe/.local/share/flatpak/exports/share/sounds/ - file
/home/lethe/.Xauthority - file
/home/lethe/.config/mimeapps.list.new - file
/home/lethe/.fonts.conf.d - file
/home/lethe/.local/share/fonts/.uuid - file
/home/lethe/.drirc - file
/home/lethe/.pulse/client.conf - file
/home/lethe/.asoundrc - file
/home/lethe/.config/alsa/asoundrc
When running the Idyll browser, Utopia also accessed:
- directory
/home/lethe/.idyll/idyll browser(with the space in it) - directory
/home/lethe/.cache/idyll/idyll browser - directory
/home/lethe/.config/gtk-3.0/ - directory
/home/lethe/.local/share/themes/ - directory
/home/lethe/.local/share/flatpak/exports/ - directory
/home/lethe/Idyll
Utopia did not attempt to access any personal files I did not explicitly tell it to open.
However, Utopia DID read from /etc/passwd:
3270 openat(AT_FDCWD, "/etc/passwd", O_RDONLY|O_CLOEXEC) = 11
and /etc/hosts:
3270 openat(AT_FDCWD, "/etc/hosts", O_RDONLY|O_CLOEXEC) = 10
and may have attempted to determine what security measures were on the device:
3387 access("/etc/selinux/config", F_OK) = -1 ENOENT (No such file or directory)
Utopia also, for whatever reason, looks for Firefox, Thunderbird, and Hexchat:
2864 openat(AT_FDCWD, "/usr/share/applications/firefox.desktop", O_RDONLY) = 86
2864 access("/usr/local/sbin/firefox", X_OK) = -1 ENOENT (No such file or directory)
2864 access("/usr/local/bin/firefox", X_OK) = -1 ENOENT (No such file or directory)
2864 access("/usr/sbin/firefox", X_OK) = -1 ENOENT (No such file or directory)
2864 access("/usr/bin/firefox", X_OK) = 0
2864 access("/usr/local/sbin/firefox", X_OK) = -1 ENOENT (No such file or directory)
2864 access("/usr/local/bin/firefox", X_OK) = -1 ENOENT (No such file or directory)
2864 access("/usr/sbin/firefox", X_OK) = -1 ENOENT (No such file or directory)
2864 access("/usr/bin/firefox", X_OK) = 0
2864 openat(AT_FDCWD, "/usr/share/applications/io.github.Hexchat.desktop", O_RDONLY <unfinished ...>
2864 access("/usr/local/sbin/hexchat", X_OK) = -1 ENOENT (No such file or directory)
2864 access("/usr/local/bin/hexchat", X_OK) = -1 ENOENT (No such file or directory)
2864 access("/usr/sbin/hexchat", X_OK) = -1 ENOENT (No such file or directory)
2864 access("/usr/bin/hexchat", X_OK) = 0
2864 openat(AT_FDCWD, "/usr/share/applications/io.github.Hexchat.desktop", O_RDONLY) = 86
2864 access("/usr/local/sbin/hexchat", X_OK) = -1 ENOENT (No such file or directory)
2864 access("/usr/local/bin/hexchat", X_OK) = -1 ENOENT (No such file or directory)
2864 access("/usr/sbin/hexchat", X_OK) = -1 ENOENT (No such file or directory)
2864 access("/usr/bin/hexchat", X_OK) = 0
2864 openat(AT_FDCWD, "/usr/share/applications/io.github.Hexchat.desktop", O_RDONLY) = 86
2864 access("/usr/local/sbin/hexchat", X_OK) = -1 ENOENT (No such file or directory)
2864 access("/usr/local/bin/hexchat", X_OK) = -1 ENOENT (No such file or directory)
2864 access("/usr/sbin/hexchat", X_OK) = -1 ENOENT (No such file or directory)
2864 access("/usr/bin/hexchat", X_OK) = 0
2864 openat(AT_FDCWD, "/usr/share/applications/io.github.Hexchat.desktop", O_RDONLY) = 86
2864 access("/usr/local/sbin/hexchat", X_OK) = -1 ENOENT (No such file or directory)
2864 access("/usr/local/bin/hexchat", X_OK) = -1 ENOENT (No such file or directory)
2864 access("/usr/sbin/hexchat", X_OK) = -1 ENOENT (No such file or directory)
2864 access("/usr/bin/hexchat", X_OK) = 0
2864 openat(AT_FDCWD, "/usr/share/applications/thunderbird.desktop", O_RDONLY) = 86
2864 access("/usr/local/sbin/thunderbird", X_OK) = -1 ENOENT (No such file or directory)
2864 access("/usr/local/bin/thunderbird", X_OK) = -1 ENOENT (No such file or directory)
And Utopia also really wants to know when your version of Debian is EOL:
3074 openat(AT_FDCWD, "/usr/share/distro-info/debian.csv", O_RDONLY|O_CLOEXEC) = 3
To be fair, I didn't even know this file existed. I suppose this'll save me a few trips to Wikipedia in the future. Thanks, Utopia!
I was also able to take a Wireshark capture of the traffic going in and out of my VM... for the first half-hour, anyway. I realize now as I write this that I could have ran it on the host machine attached to the virtual network interface VirtualBox creates, but I was in a rush to get set up, so I had Wireshark running inside the VM because that's what I knew would work. I only allocated two gigabytes to the virtual machine, so cue my surprise when the entire thing slowed to a crawl for a few minutes until the Linux OOM killer nuked Wireshark. Thankfully I discovered the .pcapng file in the VM's /tmp directory (and it was two gigabytes large! fancy that!) so I was still able to salvage what Wireshark had managed to capture of Utopia's network traffic. I also learned that Wireshark has a command-line version, tshark, which makes it far easier to rip data from a packet capture file than waiting for the GUI to load and then figure out how to export traffic as a text file.
tshark -T fields -e ip.dst -r /home/lethe/Documents/wireshark_enp0s3Y4PGY1.pcapng | grep -Ev "10.0.2" > /home/lethe/Documents/ip.txt
About twenty minutes or so (I wasn't counting because I was eating dinner) later, I had condensed the two-gigabyte packet capture into a twelve-megabyte list of only the IPs that the VM had talked to, minus any LAN traffic. I then had to create two new lists: one with each IP address ranked by the number of times Utopia had connected to it, and one with only unique IPs so that I could see how many people Utopia had connected to. As it turns out, uniq, the command-line tool that can do both of those jobs, has a bug where it only counts a line as a duplicate of another line if those two lines are adjacent to each other. Thus I had to run sort twice.
For the first list, I ran cat ~/Documents/ip.txt | sort | uniq -c | sort -gr | head -n 15, and it gave me the following data for the fifteen most connected-to IPs:
| Number of connections | IP address | Country |
|---|---|---|
| 79778 | 142.202.241.229 | USA |
| 71747 | 142.202.241.227 | USA |
| 68267 | 142.202.242.91 | USA |
| 63915 | 142.202.242.235 | USA |
| 56505 | 142.202.241.181 | USA |
| 54366 | 95.217.32.101 | Finland |
| 50786 | 95.216.226.81 | Finland |
| 49881 | 138.201.223.188 | Germany |
| 47458 | 195.201.196.58 | Germany |
| 42893 | 23.88.71.29 | Germany |
| 42166 | 95.217.45.95 | Finland |
| 38891 | 88.198.1.111 | Germany |
| 38819 | 185.222.66.220 | Germany |
| 37368 | 85.14.248.179 | Germany |
| 25267 | 173.208.183.82 | USA |
All (but one) of the top IPs seem to really hate AbuseIPDB user Tha_14, as this user has reported each one at least once within the past year for port scanning. While this isn't definitive evidence of a botnet, the fact that each one was active in Utopia within a day or two of my test (otherwise my device would not have connected to them) and port-scanned the same person definitely implies some kind of coordinated attack.
For the second list, I ran cat ~/Documents/ip.txt | sort | uniq | wc -l and fed the results of that list to a custom script that queries the AbuseIPDB API for the purpose of each IP. (Well, it gives the full information about each IP, so I could see that Russia only showed up once or twice, but I had it filtered further with jq.) The list only returned about three hundred and eighty unique IP addresses, which was well within the daily limits for AbuseIPDB's free tier of membership.
| IP allocation | Number of occurrences |
|---|---|
| Data Center/Web Hosting/Transit | 329 |
| Fixed Line ISP | 12 |
| Commercial | 6 |
| Mobile ISP | 4 |
As shown in the table, the vast majority of IP addresses that Utopia connected to during the tests were owned by VPS hosting companies, not residential ISPs as I would have first guessed. I have three hypotheses as to why this is the case.
Firstly, as I wrote in the beginning of this post, Utopia's devs nowadays mainly focus on their cryptocurrency, Cryptons. When attempting to debug why no sites were loading in Idyll, I forgot to mention that there was a "Console" feature, which I thought would allow me to run tools like ping, but instead it was a glorified log viewer that showed that Utopia was making thousands of connections a minute to fetch "mining history updates" and "finance balance requests". The vast majority of these mackets were marked "skipped", but that doesn't negate that they were sent to my node in the first place. Given how gung-ho the Utopia devs are about crypto, and considering that the official mining bot apparently requires four gigabytes of RAM at minimum and a public IP, it's not that far of a stretch to assume that these VPSes were running the Crypton mining bot. Please note that the bot is also closed-source, so these people trying to scrape pennies together have effectively given the Utopia devs access to lots of VPSes trusting that they won't become part of a botnet.
Secondly, if these are potential command-and-control centers for a Utopia botnet, then it would make sense to have as many IPs as possible in case of some of them going down from seizure and to get them from virtual private server providers to reduce the cost of quickly rotating IPs. But that doesn't explain why so many of the IP addresses are owned by the same company. In the case of an active botnet, that company would have the power to kill a large part of the infected machines.
Thirdly, less likely but still worth mentioning, is that some of these virtual private servers might be set up as personal VPNs to save users from a nasty letter from their ISP should the closed-source Utopia client generate some shady traffic. Depending on how the VPN was set up and if the VPN blocks local LAN traffic, it could make it harder for Utopia, if it was really a Trojan horse, to attempt to infect the rest of the machines in one's house.
To close out this investigation, I downloaded the Utopia installers for every operating system Utopia supports (Windows, macOS, and Debian-based and RPM-based Linux) and threw them into VirusTotal. Someone had tested the Debian installer before me, which came back clean. The RPM installer also passed VirusTotal's scans, but the Windows installer came back with a high chance of being unclassified malware. The Mac version also read some sensitive system files, may have attempted to determine if it was in a sandbox, and tripped an IDS rule relating to two CVEs.
In conclusion, while Utopia didn't immediately lock up my virtual machine and demand crypto to restore my files or start DDoSing some poor schmuck's server, it still displayed quite a lot of shady behavior. An open-source project, if a debugger caught it looking around in sensitive system files, could point to the exact points in the code where this behavior occurs and justify the access. If an end-user still did not trust the binaries, if they were competent enough at programming, they could attempt to patch out this behavior and compile from source. But Utopia is closed-source, and its developers are more concerned with the value of their cryptocurrency than with addressing any of the real concerns about trust and privacy due to the lack of source code. Considering the lack of public source code, the clear priorities of the developers, and the lack of things to do from the viewpoint of a user who cannot acquire money to spend in the ecosystem, Utopia has no function, no worth, and no future except as a platform for a future exit scam.
CC BY-NC-SA 4.0 © Vane Vander