AWS Key Patterns
This commit is contained in:
parent
fc36b38430
commit
e9c1ce1c09
|
|
@ -8,7 +8,6 @@
|
|||
- [Exploit](#exploit)
|
||||
- [Google Maps](#google-maps)
|
||||
- [Algolia](#algolia)
|
||||
- [AWS Access Key ID & Secret](#aws-access-key-id--secret)
|
||||
- [Slack API Token](#slack-api-token)
|
||||
- [Facebook Access Token](#facebook-access-token)
|
||||
- [Github client id and client secret](#github-client-id-and-client-secret)
|
||||
|
|
|
|||
|
|
@ -8,7 +8,9 @@
|
|||
- [Summary](#summary)
|
||||
- [Training](#training)
|
||||
- [Tools](#tools)
|
||||
- [AWS Patterns](#aws-patterns)
|
||||
- [AWS - Patterns](#aws---patterns)
|
||||
- [URL Services](#url-services)
|
||||
- [Access Key ID & Secret](#access-key-id--secret)
|
||||
- [AWS - Metadata SSRF](#aws---metadata-ssrf)
|
||||
- [Method for Elastic Cloud Compute (EC2)](#method-for-elastic-cloud-compute-ec2)
|
||||
- [Method for Container Service (Fargate)](#method-for-container-service-fargate)
|
||||
|
|
@ -188,9 +190,12 @@
|
|||
|
||||
|
||||
|
||||
## AWS Patterns
|
||||
## AWS - Patterns
|
||||
|
||||
### URL Services
|
||||
|
||||
| Service | URL |
|
||||
|-------------|--------|
|
||||
|--------------|-----------------------|
|
||||
| s3 | https://{user_provided}.s3.amazonaws.com |
|
||||
| cloudfront | https://{random_id}.cloudfront.net |
|
||||
| ec2 | ec2-{ip-seperated}.compute-1.amazonaws.com |
|
||||
|
|
@ -217,6 +222,26 @@
|
|||
| mediapackage | https://{random_id}.mediapackage.{region}.amazonaws.com/in/v1/{random_id}/channel |
|
||||
|
||||
|
||||
### Access Key ID & Secret
|
||||
|
||||
> IAM uses the following prefixes to indicate what type of resource each unique ID applies to.
|
||||
|
||||
| Prefix | Resource type |
|
||||
|--------------|-------------------------|
|
||||
| ABIA | AWS STS service bearer token |
|
||||
| ACCA | Context-specific credential |
|
||||
| AGPA | User group |
|
||||
| AIDA | IAM user |
|
||||
| AIPA | Amazon EC2 instance profile |
|
||||
| AKIA | Access key |
|
||||
| ANPA | Managed policy |
|
||||
| ANVA | Version in a managed policy |
|
||||
| APKA | Public key |
|
||||
| AROA | Role |
|
||||
| ASCA | Certificate |
|
||||
| ASIA | Temporary (AWS STS) access key |
|
||||
|
||||
|
||||
## AWS - Metadata SSRF
|
||||
|
||||
> AWS released additional security defences against the attack.
|
||||
|
|
|
|||
|
|
@ -288,6 +288,9 @@ PS C:\> Add-MpPreference -ExclusionPath "C:\Temp"
|
|||
PS C:\> Add-MpPreference -ExclusionPath "C:\Windows\Tasks"
|
||||
PS C:\> Set-MpPreference -ExclusionProcess "word.exe", "vmwp.exe"
|
||||
|
||||
# exclude using wmi
|
||||
PS C:\> WMIC /Namespace:\\root\Microsoft\Windows\Defender class MSFT_MpPreference call Add ExclusionPath="C:\Users\Public\wmic"
|
||||
|
||||
# remove signatures (if Internet connection is present, they will be downloaded again):
|
||||
PS > & "C:\ProgramData\Microsoft\Windows Defender\Platform\4.18.2008.9-0\MpCmdRun.exe" -RemoveDefinitions -All
|
||||
PS > & "C:\Program Files\Windows Defender\MpCmdRun.exe" -RemoveDefinitions -All
|
||||
|
|
|
|||
|
|
@ -57,10 +57,11 @@
|
|||
|
||||
## Tools
|
||||
|
||||
- [SSRFmap - https://github.com/swisskyrepo/SSRFmap](https://github.com/swisskyrepo/SSRFmap)
|
||||
- [Gopherus - https://github.com/tarunkant/Gopherus](https://github.com/tarunkant/Gopherus)
|
||||
- [See-SURF - https://github.com/In3tinct/See-SURF](https://github.com/In3tinct/See-SURF)
|
||||
- [SSRF Sheriff - https://github.com/teknogeek/ssrf-sheriff](https://github.com/teknogeek/ssrf-sheriff)
|
||||
- [swisskyrepo/SSRFmap](https://github.com/swisskyrepo/SSRFmap) - Automatic SSRF fuzzer and exploitation tool
|
||||
- [tarunkant/Gopherus](https://github.com/tarunkant/Gopherus) - Generates gopher link for exploiting SSRF and gaining RCE in various servers
|
||||
- [In3tinct/See-SURF](https://github.com/In3tinct/See-SURF) - Python based scanner to find potential SSRF parameters
|
||||
- [teknogeek/SSRF Sheriff](https://github.com/teknogeek/ssrf-sheriff) - Simple SSRF-testing sheriff written in Go
|
||||
* [assetnote/surf](https://github.com/assetnote/surf) - Returns a list of viable SSRF candidates
|
||||
|
||||
## Payloads with localhost
|
||||
|
||||
|
|
|
|||
|
|
@ -42,6 +42,16 @@
|
|||
|
||||
|
||||
|
||||
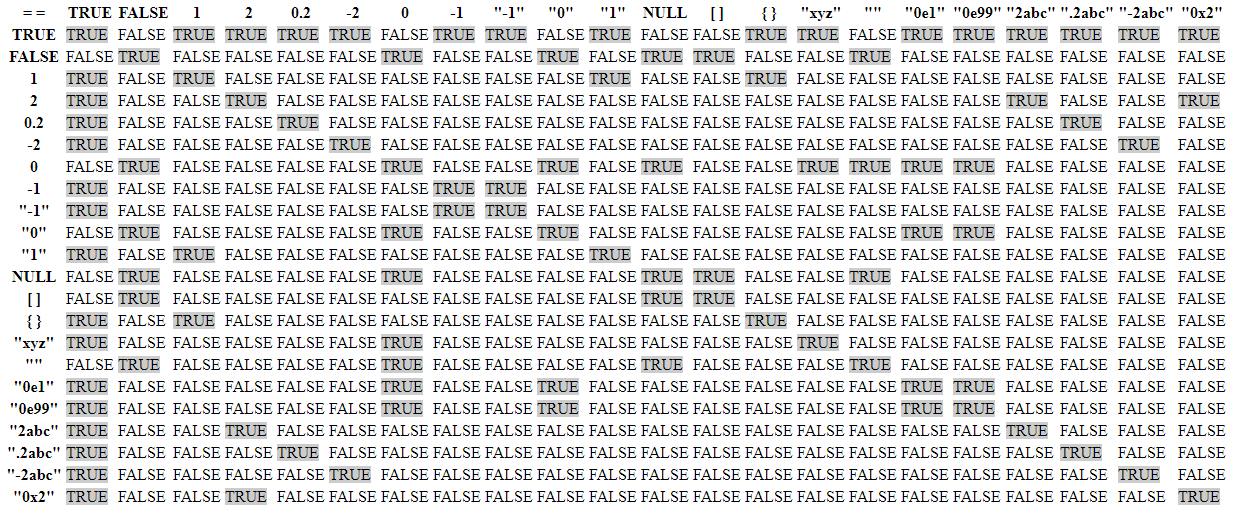
Loose Type Comparisons occurs in many languages:
|
||||
* [MariaDB](https://github.com/Hakumarachi/Loose-Compare-Tables/tree/master/results/Mariadb)
|
||||
* [MySQL](https://github.com/Hakumarachi/Loose-Compare-Tables/tree/master/results/Mysql)
|
||||
* [NodeJS](https://github.com/Hakumarachi/Loose-Compare-Tables/tree/master/results/NodeJS)
|
||||
* [PHP](https://github.com/Hakumarachi/Loose-Compare-Tables/tree/master/results/PHP)
|
||||
* [Perl](https://github.com/Hakumarachi/Loose-Compare-Tables/tree/master/results/Perl)
|
||||
* [Postgres](https://github.com/Hakumarachi/Loose-Compare-Tables/tree/master/results/Postgres)
|
||||
* [Python](https://github.com/Hakumarachi/Loose-Compare-Tables/tree/master/results/Python)
|
||||
* [SQLite](https://github.com/Hakumarachi/Loose-Compare-Tables/tree/master/results/SQLite/2.6.0)
|
||||
|
||||
|
||||
### NULL statements
|
||||
|
||||
|
|
|
|||
Loading…
Reference in New Issue